How to Protect Your Crypto From Phishing Emails
Main Takeaways
Phishing is a cyberattack technique where scammers “fish” for sensitive credentials by posing as a person or well-known company you trust.
Common phishing techniques include spoofing, using urgent or threatening language, and inserting harmful links.
Attackers often modify their sender identity to make their email appear as if it’s coming from a trusted source.
If you’re unsure whether or not a Binance email is genuine, please contact Binance Support and provide them with the email’s EML file along with relevant screenshots.
Your Binance account could be a target for phishers. Learn how to secure your crypto funds with this comprehensive guide.
Your average hacker doesn’t have the know-how to break into Binance’s security system. However, what they most certainly have are the tools to trick you into giving them your username, password, and two-factor authentication (2FA) code.
Why drill into a state-of-the-art vault when you could just convince the owner to let you inside? This is the basis of phishing: exploiting human error and emotions.
Keep reading to learn more about phishing, how it works, and how to protect your crypto from common phishing techniques.
What Is Phishing and How Does It Work?
Phishing is a popular cyberattack technique where scammers “fish” for sensitive credentials by impersonating a person or well-known company you trust, such as Binance. The most prevalent method is via email. These sneaky messages are easy to make, and some look nearly identical to their legitimate counterparts.
It sounds simple, but they work, and that’s why most cyberattacks start with a phishing email. According to a study by email security company Valimail, over three billion spoofing messages are sent every day, which accounts for 1% of all email traffic.
To secure your crypto and personal details, it’s crucial to know how to identify and protect yourself from phishing emails. First, let’s look at a few common examples.
Three Examples of Phishing Emails
The following section is a brief overview of phishing email techniques, including spoofing, using urgent or threatening language, and inserting harmful links. We’ve also included real-life examples to help you understand each technique better.
1. Email spoofing
Spoofing is a deceptive technique whereby scammers create fake sender and domain names that resemble an official source. The idea is that you’ll believe the email is legitimate because it contains something like “binance” in the sender's address.
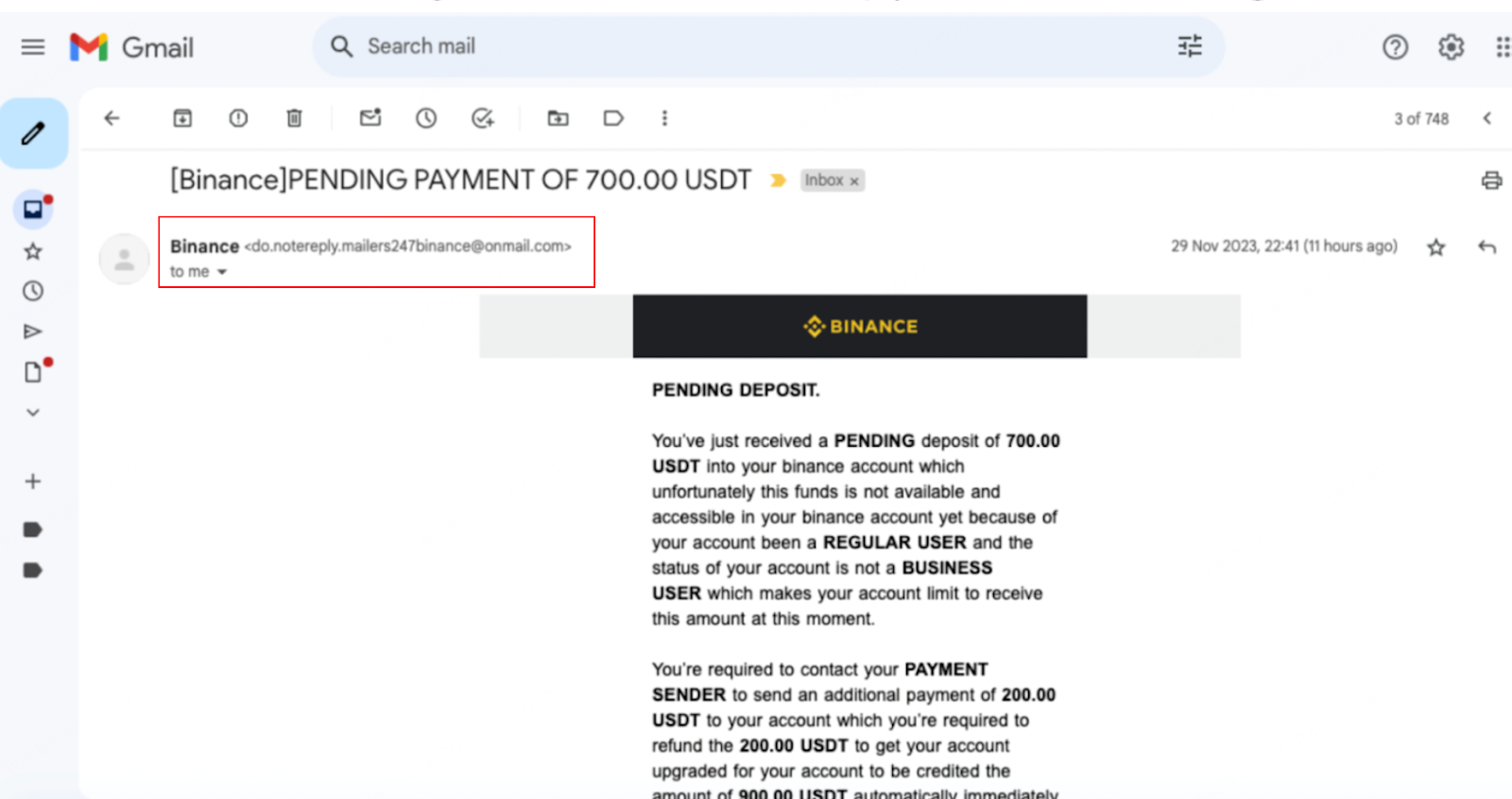
Here’s a real-life example where scammers used the address “do.notereply.mailers247binance@onmail.com.” It may seem official until you notice that the sender’s address reads “onmail.com.”
2. Urgent or threatening language
Phishing emails often create a sense of urgency, fear, or curiosity to manipulate your emotions and prompt immediate action. For example, they may make you believe there’s an unexpected withdrawal from your account, leading you to “reset” your password. In reality, you’ve just exposed your password to a scammer.
Here’s an example of a phishing email that claims the recipient has made an unexpected withdrawal. Note the language in the highlighted portion. It’s purposefully constructed to confuse and scare you with words like “lock your account” and “secure all your funds.”
3. Malicious links and fake attachments
Phishing emails frequently contain links that take you to fake websites resembling legitimate ones. They might also include attachments such as PDFs, executable files, or repackaged applications that contain harmful scripts or malware. Opening these attachments can give attackers unauthorized access to your devices or enable them to steal sensitive information or transfer funds without your consent.
Below is an example of a phishing email containing a malicious link. Clicking [Verify Email] would lead you to a fake Binance login page where you are asked to enter your username and password. Scammers could then collect your data to either resell it or steal your account and funds.
Four Ways to Identify a Phishing Attack
Now that we’ve gone through a few examples of phishing emails, let’s dive into some different ways you can identify a phishing email.
1. Binance Verify
Have you received an email from Binance, but something looks suspicious? Search the sender address on Binance Verify first. If you receive a “Source Not Verified” message, the email likely has ill intent.
However, the source address could still be a spoofed email even if it passes an initial check on Binance Verify. As mentioned previously, email spoofing is a common technique scammers use to make an email appear as if it was sent from a trusted source. They do this by using look-alike sender domains or spoofing email headers via the “Reply-To” or “Return-Path” fields.
Besides sender addresses, Binance Verify can also help validate any social media accounts or website links listed in the email’s contents.
Social media accounts
If the email asks you to contact a “Binance employee” via social media platforms like Telegram, Facebook, or WeChat, make sure to verify the username on Binance Verify.
The image below displays what should appear if the account has a genuine Binance username. Note that criminals will often impersonate employees from our company. Binance Verify is only one of many steps you should take to verify someone’s identity.
Website links
Exercise caution when clicking on website links in emails. To verify a Binance URL, right-click on the link and select “Copy link address.” Next, use Binance Verify to check if the website is legitimate. The image below displays what Binance Verify should show if the website is an official domain from Binance.
2. Anti-phishing code
We strongly encourage setting up your anti-phishing code if you haven’t already. It’s simple and only takes a few minutes. Once set up, every genuine email you receive from Binance will include the unique combination of numbers and letters you set.
Here’s what an official email from Binance looks like with and without an anti-phishing code. Steer clear of any “Binance” emails that don’t contain your anti-phishing code.

3. EML file verification
Downloading the email as an EML file provides additional hidden information for verification purposes. While more technical, this method is very adept at detecting phishing attacks.
SPF/DMARC/DKIM
For example, you can open the file and perform an SPF/DMARC/DKIM check. If all three or some of the checks fail (e.g., the check shows “dkim=fail”), the email is likely from an unauthorized source.
IP reputation
You can also find the IP address inside the EML file to check for any reported illicit activities. Simply copy and paste the address onto an IP reputation checker, such as abuseipdb or virustotal. Note: These databases may not have information if an IP address is too new. Always check with multiple trusted sources before coming to a conclusion.
4. Contact Binance Support
If you’re suspicious of an email, we recommend contacting Binance Support with screenshots and the EML file. This is the most foolproof method out of every tip listed in this guide. Once we receive your case file, our security team, which has years of experience dealing with phishing attacks, will help verify your email’s authenticity.
If you need help downloading the EML file, you can follow the steps listed in the next section.
How to Download an EML File
Let’s take a look at how you can download email content as an EML file on Gmail and Outlook.
Gmail
Open the email you want to download as an EML file. Click on the three-dot icon located in the top-right corner of the email.
Select “Download message” from the drop-down menu.
Outlook
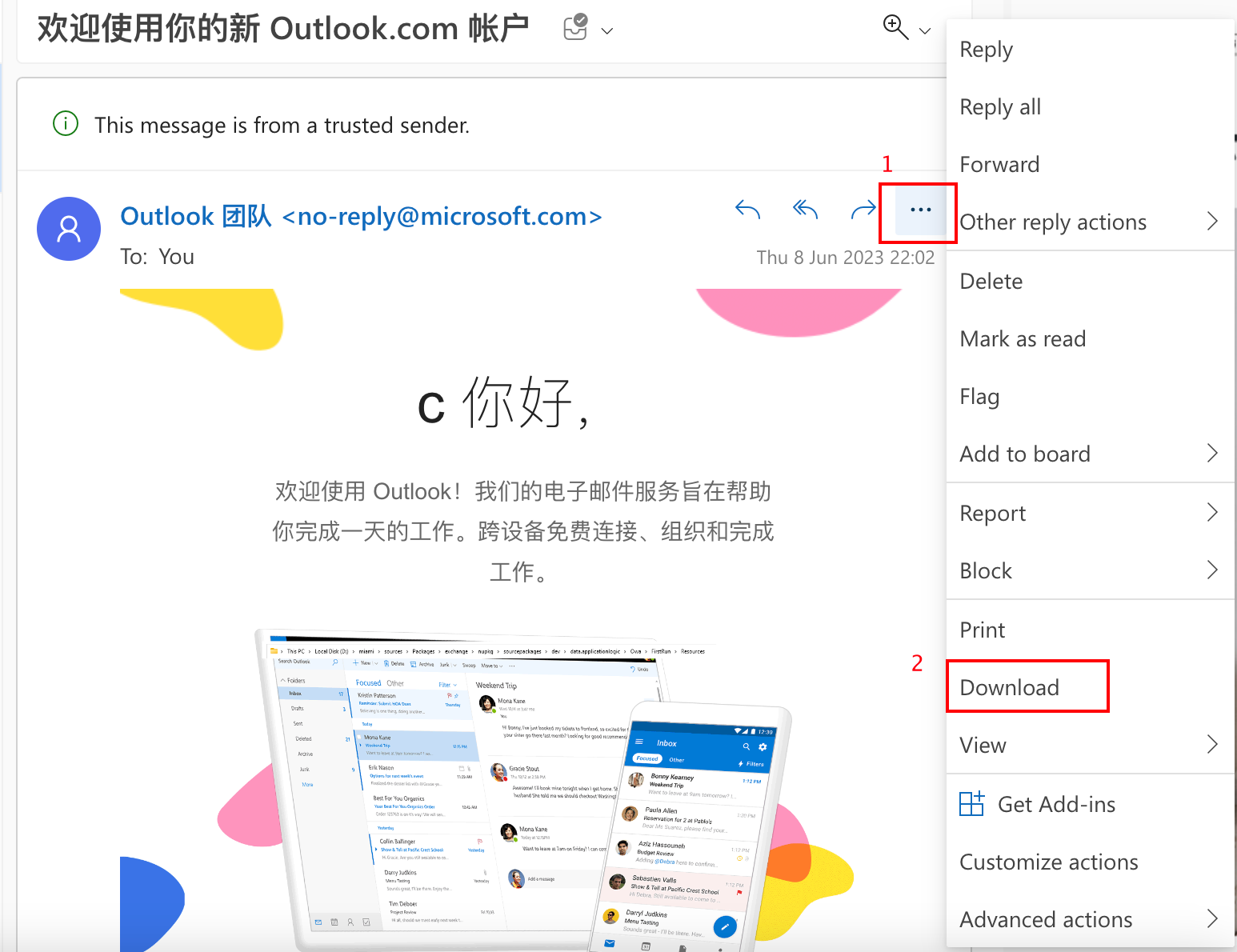
Open the email you want to download as an EML file. Click on the three-dot icon located in the top-right corner of the email.
Select “Download” from the drop-down menu.
Once downloaded, right-click the EML file and press [Open With], followed by [Other]. Then, select TextEdit if you’re using macOS or Notepad(++) if you’re using Windows.
Don’t Get Caught by Phishers
Stay vigilant against phishing attempts. Learn to protect your funds today, and you may end up saving yourself from a future disaster. Here’s a quick summary of the best practices to follow:
Set up your anti-phishing code by following this guide.
Search for any “Binance” email address, username, or URL on Binance Verify first.
Don’t click on suspicious links. You might unknowingly install malware on your device or find yourself on a spoofed site designed to collect sensitive information.
Don’t share your personal information with a stranger, including user credentials, phone numbers, bank accounts, wallet seed phrases, or private keys.
Enable two-factor authentication (2FA). If your account details are stolen, 2FA can make it more difficult for scammers to take over your account.
Only participate in activities with a legitimate company. Be cautious of “free giveaways” and “airdrop” invitations you receive in your email.
If you’re still uncertain about an email, contact Binance Support for help! We’re more than happy to verify the EML file for you.