Original source: Certik
On July 1, 2023, an attacker exploited a vulnerability in Poly Network to issue $42 billion worth of assets on multiple chains. Despite the large amount of assets issued, the attacker was unable to obtain more than $10 million in assets from 5 external account addresses due to low liquidity and freezing of some project tokens.
This is the first cross-chain bridge attack this year and the second attack on Poly Network. The total loss of last year's attacks reached $3.7 billion, of which the cross-chain bridge attack accounted for 35%. Although this incident seems to be the largest vulnerability attack in history, the actual profit of the hackers is much lower.
Event Summary
On July 1, 2023 at 14:47 Beijing time, a malicious actor transferred assets from Poly Network's Lock Proxy contract to the attacker's address by initiating several cross-chain bridge transactions. On paper, the attacker made a profit of more than $42 billion worth of assets from 10 chains.
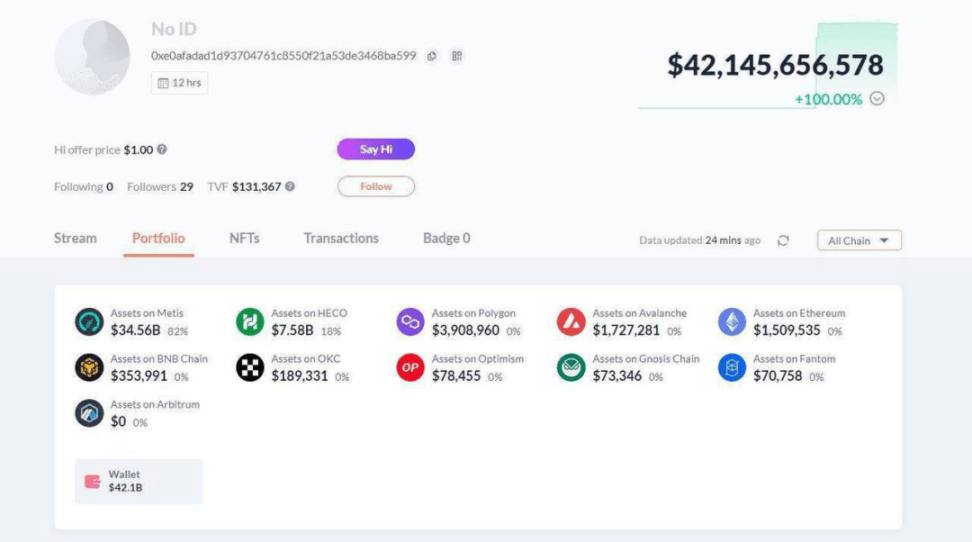
Image: Poly Network attacker wallet address. Source: Debank
But in fact, this number is misleading. For example, the attacker held more than $34 billion of poly-pegged BNB and BUSD on the Metis blockchain, but these tokens could not be sold due to lack of liquidity. Later, Metis also confirmed in a tweet that those newly minted BNB and BUSD had no available liquidity and were therefore worthless.
Likewise, a large number of remaining tokens became worthless. After hearing about the incident and the tokens issued by the attacker, several projects took prompt action to remove liquidity to prevent token dumping and price collapse. For example, OpenOcean, StackOS, Revomon, and NEST all removed liquidity from the project to prevent the attacker from selling.
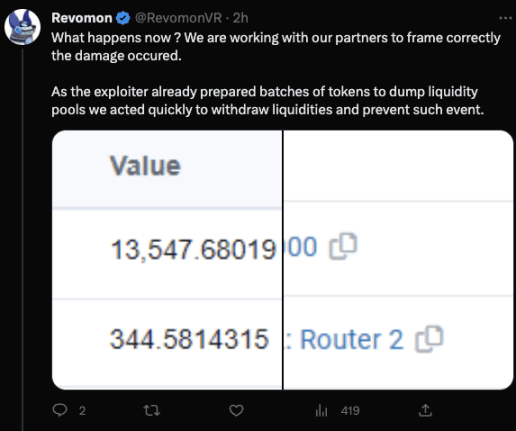
Revomon Twitter
Although the $42 billion figure does not accurately reflect the losses caused by this incident, CertiK has confirmed that at least $10 million in assets are stored in 5 Ethereum wallets.
Cross-chain bridge vulnerability
In 2022, security incidents affecting cross-chain bridges resulted in $1.3 billion in economic losses, and this $1.3 billion was caused by just five incidents, which shows the destructive power of cross-chain bridge security vulnerabilities. The difficulty of protecting cross-chain bridges, coupled with their huge value and various attack paths that can be exploited, makes these infrastructures often the first target of malicious actors. Cross-chain bridges are composed of multiple parts such as custodians, issuers, oracles, etc. Due to the large amount of funds locked in the bridge, any misconfiguration, vulnerability or malicious exploitation can result in significant losses.
Attack Process
Poly Network uses the "Lock" and "Unlock" functions to bridge assets between different networks. Users must first "lock" tokens on the source chain before they can "unlock" on the target chain.
The following example is based on a cross-chain transfer from BSC to ETH.
The attacker first called the Lock function on the BSC network to initiate a cross-chain transfer of a small amount of 8PAY tokens.
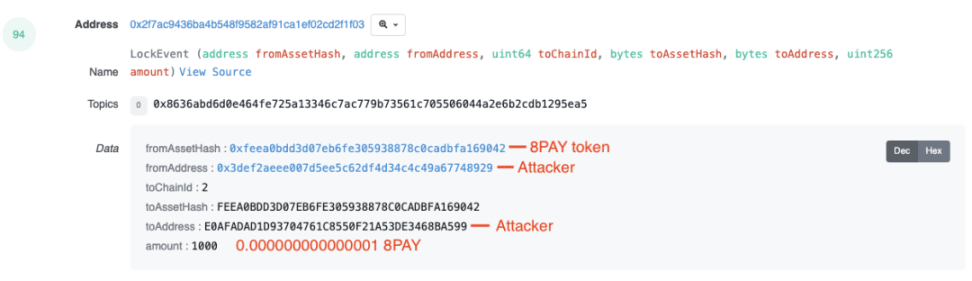
Image: The attacker used a small amount of 8PAY tokens to initiate a cross-chain transfer. Source: Etherscan
In this transaction, the data is specified as “0x4a14feea0bdd3d07eb6fe305938878c0cadbfa16904214e0afadad1d93704761c8550f21a53de3468ba599e8030000000000000000000000000000000” and the four bytes starting with “0x4a” represent the data length.
The attacker called the EthCrossChainManager.verifyHeaderAndExecuteTx() function, triggering the corresponding UnlockEvent "unlock" function. We can see from the 4 bytes at the beginning indicating the data length that the current transaction data has changed.
「0x14feea0bdd3d07eb6fe305938878c0cadbfa16904214e0afadad1d93704761c8550f21a53de3468ba59900e00fc80b54905e35ca0d000000000000000000000000000000000000000000」
In this transaction, the number of 8pay tokens increased significantly.
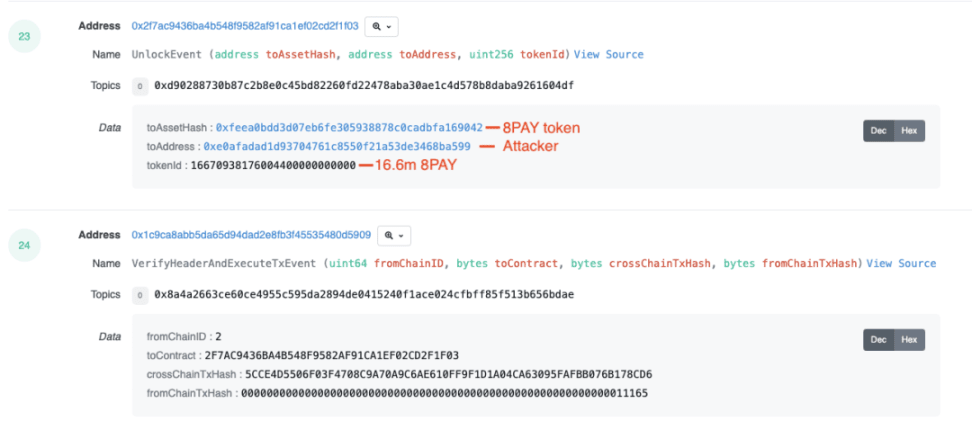
The attacker repeated the process according to the above steps. 57 tokens were involved and distributed on 11 different blockchains. The attacker profited from approximately $42 billion in assets (calculated by book value).
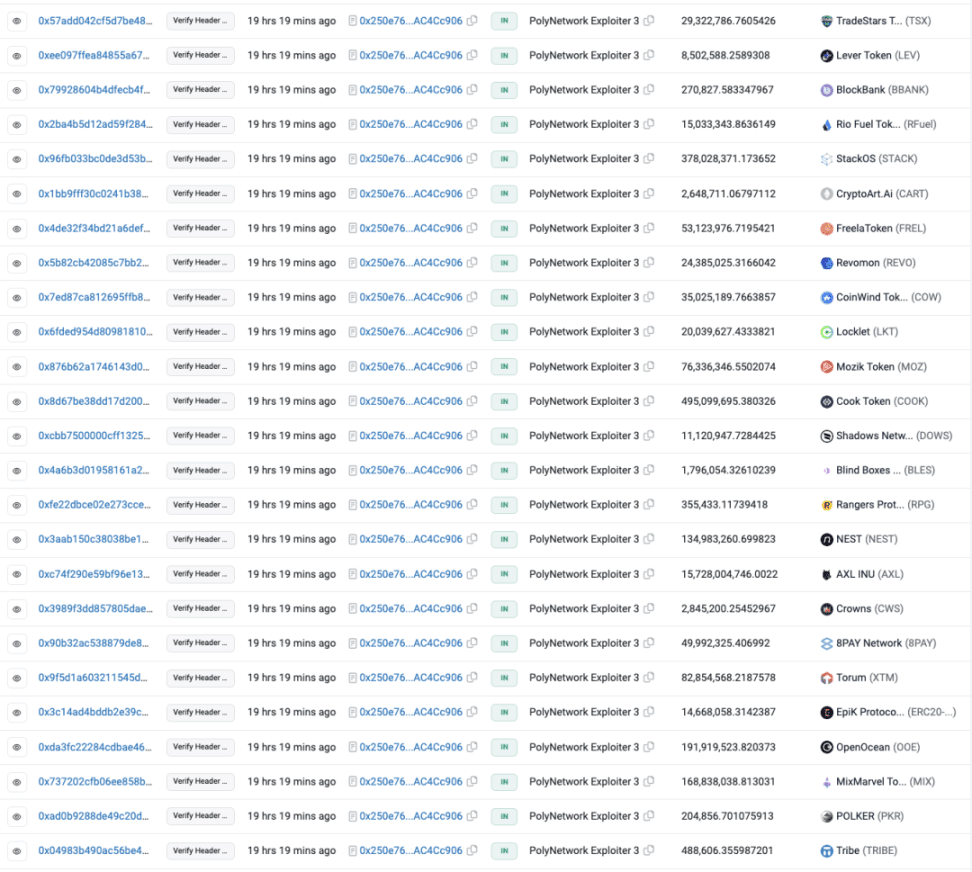
Image: Tokens unlocked by the Poly Network attacker on Ethereum. Source: Etherscan
Asset Tracking
On the Ethereum network, the attacker successfully converted some tokens into ETH. The process is as follows:
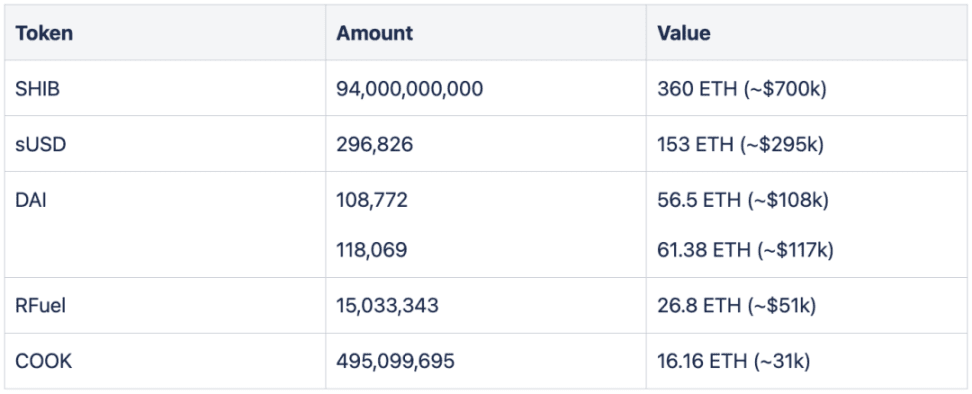
During the attack, the attacker also transferred 1,592 ETH (about $3.05 million) through a transaction and transferred 2,240 ETH to three EOA external accounts. In addition, the attacker also obtained about 3.01 million USDC and 2.65 million USDT, which were exchanged for 1,557 and 1,371 ETH respectively.

The attackers moved some of the remaining token assets to new EOA addresses, transferring 1 ETH to each address. (Although they have not yet cashed out these tokens.) Some tokens have become worthless as project owners removed liquidity from the tokens to prevent a sell-off. As of now, the attackers appear to have only made about $10 million from the incident.
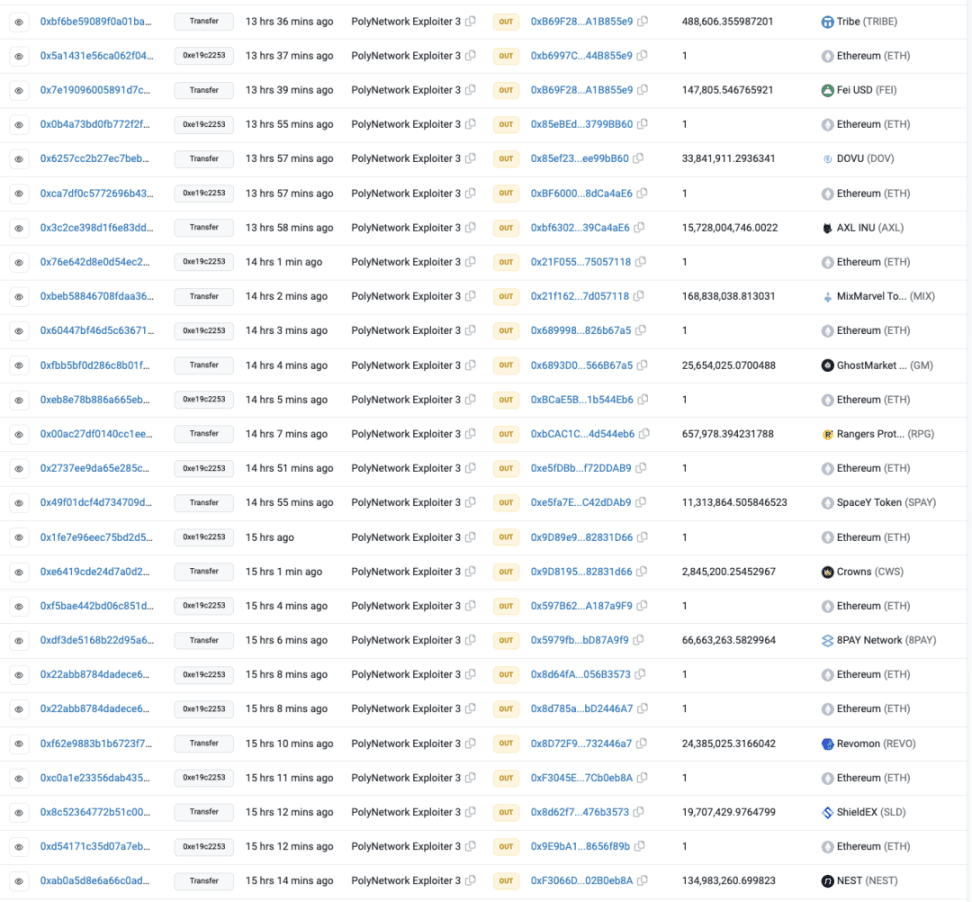
Image: Poly Network attacker transfers assets and 1 ETH to a new EOA address
Final Thoughts
In 2022, the Web3.0 ecosystem experienced the devastating effects of cross-chain bridge attacks, with projects such as Ronin Bridge, Wormhole, and Nomad all suffering from security incidents. Initial detection results of the Poly Network incident show that this is the largest security incident encountered by the Web ecosystem to date, but due to the lack of liquidity support for newly minted tokens, the losses have been controlled to approximately $10 million at the time of writing. There is currently no exact consensus on how the attacker exploited the Poly Network. However, initial signs indicate that due to the normal operation of on-chain functions, it is likely caused by a private key leak or an off-chain vulnerability.
Source link
