A dust attack refers to a new type of malicious activity where hackers or fraudsters attempt to obtain the sensitive data of Bitcoin and cryptocurrency users by sending tiny amounts of coins to their personal wallets. The transactions of these wallets are then tracked by attackers who perform a combined analysis of multiple addresses in an attempt to identify the owner.
What is dust?
In cryptocurrency parlance, the term "dust" refers to a tiny amount of coins or tokens - an amount so small that most users don't even notice it. For example, in Bitcoin, the smallest unit is 1 satoshi (0.00000001 BTC). We can use this term to refer to a couple hundred satoshis.
In cryptocurrency exchanges, dust is also the name of tiny amounts of coins that are "stuck" in user accounts after trading orders are executed. Dust balances are not exchangeable, but Binance users can convert them to BNB.
When it comes to Bitcoin, there is no official definition of dust because each software implementation (or client) can accept different threshold values. Bitcoin Core defines dust as any transaction result lower than the transaction fee, leading to the concept of a dust limit.
From a technical point of view, the dust limit is calculated according to the size of inputs and outputs, which is usually 546 satoshis for regular Bitcoin transactions (non-SegWit) and 294 satoshis for native SegWit transactions. This means that any normal transaction equal to or less than 546 satoshis will be considered spam and likely to be rejected by validating nodes.
Dust attacks
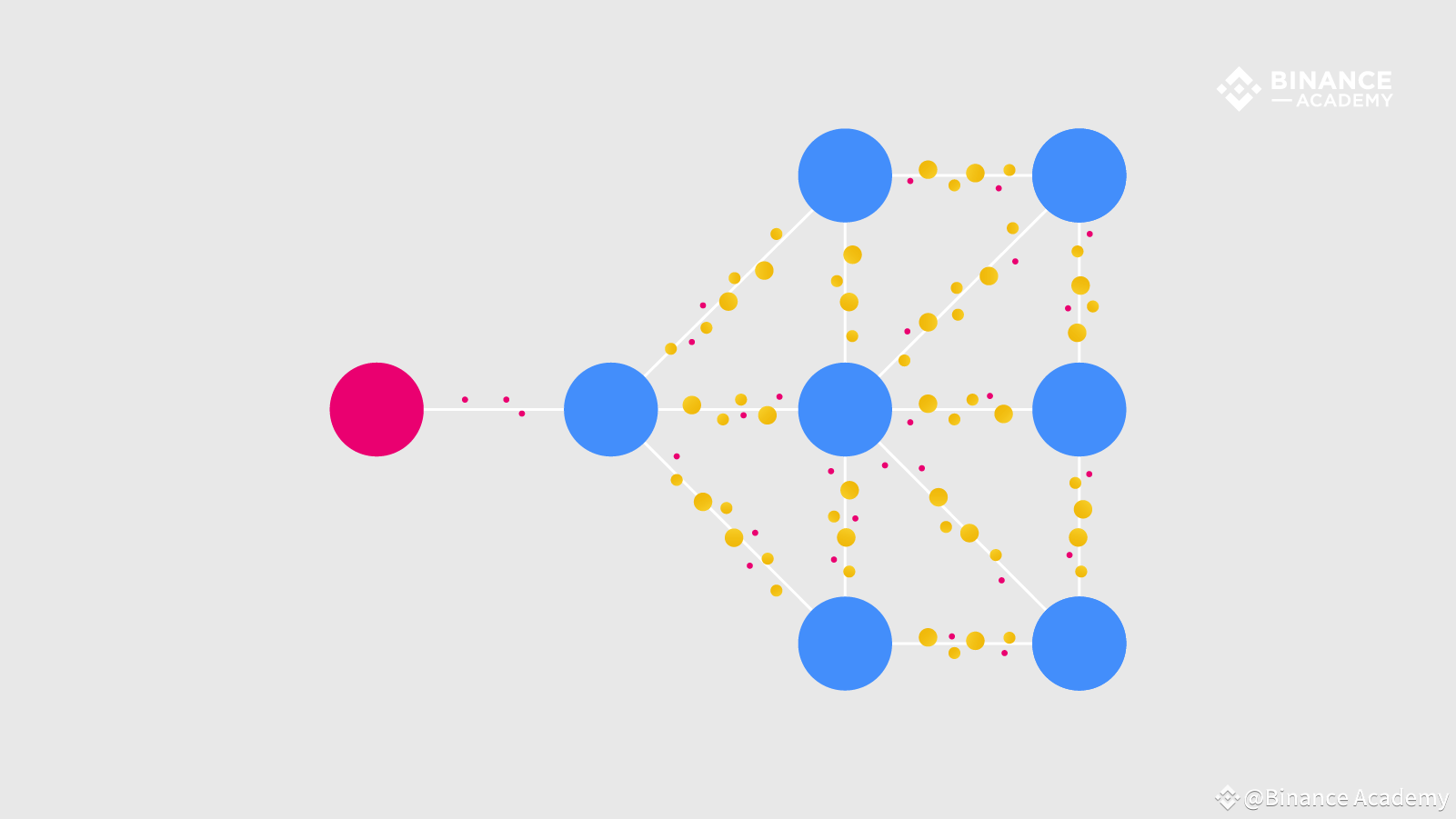
Fraudsters recently realized that cryptocurrency users don't pay much attention to these tiny amounts appearing in their wallets, so they started creating "dust attacks" from a large number of addresses, sending them a few satoshis. After multiple addresses are attacked, the next step involves a combined analysis of these addresses in an attempt to determine which of them belong to the same wallet.
The goal is to eventually be able to link the attacked addresses and wallets to the respective companies or individuals. If successful, attackers can use this knowledge for their own purposes or for elaborate phishing or cyber extortion attacks.
Dust attacks were originally carried out using Bitcoin, but they also occur with other cryptocurrencies that run on top of a public and traceable blockchain.
At the end of October 2018, the developers of the Bitcoin wallet Samourai announced that some of their users were exposed to dust attacks. The company sent out a tweet warning users about the attacks and explaining how they can protect themselves. The Samourai Wallet team has implemented real-time alerts to track dust, as well as a "Do Not Spend" feature that allows users to identify suspicious funds and exclude them from future transactions.
Since dust attacks are based on the combined analysis of multiple addresses, if dust funds do not move, attackers cannot establish the connections necessary to "de-anonymize" wallets. The Samourai wallet already has the ability to automatically notify its users about suspicious transactions. Despite dust limits of 546 satoshi, many dust attacks today far exceed it and typically range from 1,000 to 5,000 satoshi.
Bitcoin pseudo-anonymity
Because Bitcoin is open and decentralized, anyone can create a wallet and join the network without providing any personal information. Although all Bitcoin transactions are public and visible, it is not always easy to find the person behind each address or transaction, and this is what makes Bitcoin somewhat anonymous, but not completely.
Peer-to-peer (P2P) transactions are more likely to remain anonymous because they are done without the involvement of any intermediary. However, many cryptocurrency exchanges collect personal data through KYC verification processes, which means that when users transfer funds between their personal wallets and exchange accounts, they risk losing their anonymity in some way. Ideally, a new Bitcoin address should be created for each new receiving transaction or payment request to preserve user privacy.
It is important to remember that Bitcoin is not really an anonymous cryptocurrency. In addition to the recently created dust attacks, there are numerous companies, research labs and government agencies performing blockchain analysis in an attempt to de-anonymize the network and some even claim to have already made significant progress.
Final thoughts
While the Bitcoin blockchain is virtually impossible to hack or destroy, wallets often cause serious problems. Since users don't provide their personal information when creating an account, they can't prove theft if some hacker gets access to their coins - and even if they could, it would be useless.
When a user stores their cryptocurrency in a personal wallet, they act as their own bank, which means there is nothing they can do if their private keys are hacked or lost. Privacy and security are becoming more and more valuable every day, not only for those with something to hide, but for all of us. And this is especially valuable for cryptocurrency traders and investors.
Along with dust attacks and other de-anonymizing attacks, it's also important to be wary of other security threats that are part of the cryptocurrency space, such as cryptojacking, ransomware, and phishing. Other security measures can include installing a VPN along with a solid antivirus on all your devices, encrypting your wallets, and storing your keys in encrypted folders.