Introduction
The nature of modern digital communications is such that you rarely interact directly with the recipients. It may appear that you and your friends are exchanging private messages, when in fact they are being recorded and stored on a central server.
You may not want your messages to be read by the server responsible for transferring them between you and the recipient. In this case, end-to-end encryption (or E2EE) may be the solution for you.
End-to-end encryption is a method of encrypting messages between the receiver and the sender so that they are the only parties who can decrypt the data. Its origins can be traced back to the 1990s when Phil Zimmerman released Pretty Good Privacy (known as PGP).
Before we talk about why you need E2EE and how it works, let's take a look at how unencrypted messages are sent.
How are unencrypted messages sent?
Let's talk about how a regular messaging platform for smartphones can work. You install the app and create an account that allows you to communicate with other people who have done the same. You write a message and enter your friend's nickname, then send it to a central server. The server sees who you addressed the message to and sends it to the recipient.

Communication between users A and B. They must send data through the server (S) to communicate with each other.
You may know this process as the client-server model. The client (your phone) doesn't do much - instead, the server does all the heavy lifting. But it also means that the service provider acts as an intermediary between you and the recipient.
In most cases, the data between A <> S and S <> B in the chart is encrypted. An example is Transport Layer Security (TLS), which is widely used to secure connections between clients and servers.
TLS and similar security solutions prevent a message from being intercepted in transit from the client to the server. Although these measures can prevent third parties from accessing the data, the server can still read it. This is where encryption comes in handy. If the data from A has been encrypted with a cryptographic key belonging to B, the server will not be able to read or access it.
Without E2EE methods, a server can store information in a database along with millions of other data. With large-scale data breaches happening all the time, a lack of encryption can have catastrophic consequences for end users.
How does end-to-end encryption work?
End-to-end encryption ensures that no one, not even the server connecting you to other users, can access your messages. It can be anything from simple text and emails to files and video calls.
The data is encrypted in apps like Whatsapp, Signal or Google Duo (presumably) so only the senders and intended recipients can decrypt it. In end-to-end encryption schemes, this process begins with a so-called key exchange.
What is Diffie-Hellman Key Exchange?
The idea of Diffie-Hellman key exchange was invented by cryptographers Whitfield Diffie, Martin Hellman and Ralph Merkle. This is a powerful technique that allows parties to generate a shared secret in a potentially hostile environment.
In other words, key generation can occur in insecure forums (even with possible channel listening) without compromising further messages. In the information age, this is especially valuable, since the parties do not need to physically exchange keys for communication.
The exchange itself involves big numbers and cryptographic magic. We will not go into finer details. Instead, we'll use the popular analogy of paint colors. Suppose Alice and Bob are in different hotel rooms at opposite ends of the corridor and want to use the same paint color. They don't want anyone else to know which one.
Unfortunately, the corridor is full of spies. Suppose that in this example, Alice and Bob cannot enter each other's rooms, so they can only interact in the hallway. What they can do is agree on a common color in the hallway, say yellow. They take a can of this yellow paint, divide it among themselves, and return to their rooms.
In their rooms, they will mix a secret paint that no one knows about. Alice uses a shade of blue and Bob uses a shade of red. Importantly, spies cannot see these secret colors they use. Now Alice and Bob leave the rooms with their blue-yellow and red-yellow mixtures, and only the result of the mixture becomes known to the spies.
They exchange these mixtures in the fresh air. It doesn't matter that the spies see it - they can't tell the exact shade of the added colors. Remember, this is just an analogy - the actual math behind this system makes guessing the secret "color" even more difficult.
Alice takes Bob's mixture, Bob takes Alice's mixture, and they go back to the rooms again. Now they are mixing their secret colors again.
Alice combines her secret shade of blue with Bob's red-yellow mixture, producing a red-yellow-blue mixture.
Bob mixes his secret red paint with Alice's blue-yellow mixture, producing a blue-yellow-red color.
Both combinations have the same colors, so they should look the same. Alice and Bob have successfully created a unique color that the spies don't know about.
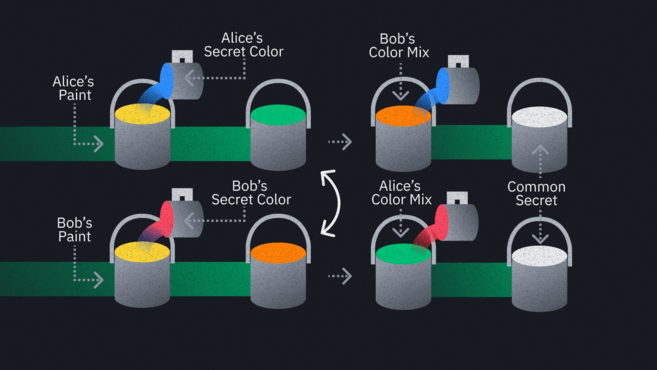
So this is the principle we can use to create a shared secret in the public domain. The difference is that we are not dealing with corridors and paint, but with insecure channels, public and private keys.
Exchange of messages
Once the parties have a shared secret, they can use it as a basis for symmetric encryption. Popular implementations usually include additional methods for more robust protection, but they are all abstractions for the user. After connecting with a friend in E2EE, encryption and decryption can only be performed on your devices (barring some serious software vulnerabilities).
It doesn't matter if you're a hacker, a service provider, or even a law enforcement officer. If the service is truly end-to-end encrypted, any intercepted message will look like garbled gibberish.
➟ Want to start trading cryptocurrency? Buy Bitcoin on Binance!
Pros and cons of end-to-end encryption
Cons of end-to-end encryption
In fact, there is only one downside to end-to-end encryption – and whether or not it's a downside depends entirely on your perspective. For some, the very value of E2EE is problematic precisely because no one can access your messages without the appropriate key.
Opponents argue that criminals can use E2EE knowing that governments and technology companies cannot decipher their messages. They believe that law-abiding people do not need to keep their messages and phone calls secret. That view is shared by many politicians who support legislation that would allow loopholes to be used to access messages. Of course, this defeats the purpose of end-to-end encryption.
Applications using E2EE are not 100% secure. Messages are encrypted in transit between devices, but are accessible at endpoints such as a laptop or smartphone. This is not a disadvantage of end-to-end encryption, but something to keep in mind.

The message is displayed in plaintext before and after decryption.
E2EE ensures that no one can read your data while it is in transit. But other threats still exist:
Your device can be stolen: If you don't have a security code set or an attacker bypasses it, they can access your messages.
Your device may be compromised: Your computer may have malware that tracks information before and after it's sent.
Another risk is that someone can come between you and your colleague, setting up a man-in-the-middle attack. This can happen at the beginning of communication - when you exchange keys, and you cannot be sure of the other party's authenticity. You may unknowingly provide confidential information to an attacker. Then the attacker will receive the message and the key to decrypt it. In this way, he can fool your friend, which means that the attacker will be able to transmit the messages and read or change them at his discretion.
To get around this, many apps integrate a security code feature. It's a string of numbers or a QR code that you can share with your contacts through a secure channel (ideally offline). If the numbers match, you can be sure that a third party is not monitoring your messages.
Advantages of end-to-end encryption
When used without any of the previously mentioned vulnerabilities, E2EE is clearly a very valuable way to improve privacy and security. This technology, like onion routing, is being promoted by privacy activists around the world. End-to-end encryption is easily built into the apps we're used to, meaning it's available to anyone who can use a mobile phone.
It would be a mistake to see E2EE as a mechanism useful only for criminals and whistleblowers. Even the most secure companies have found themselves vulnerable to cyberattacks, exposing unencrypted user information to attackers. Access to user data, such as sensitive messages or identification documents, can have catastrophic consequences for people's lives.
If a company whose users rely on E2EE is compromised, hackers will not be able to obtain any meaningful information about the content of the messages (provided their encryption implementation is reliable). At best, they will be able to get the metadata. This still raises privacy concerns, but importantly, the content of the messages remains anonymous.
Final thoughts
In addition to the applications mentioned earlier, there is a growing number of E2EE tools available. Apple's "iMessage" and Google's "Duo" come bundled with the iOS and Android operating systems, and more privacy and security-focused software continues to be released.
Let's repeat that end-to-end encryption is a magical barrier against all forms of cyber attacks. With relatively little effort, you can actively use it to significantly reduce the risk you expose yourself to online. Along with Tor, VPNs, and cryptocurrencies, E2EE messengers can be a valuable addition to your digital privacy arsenal.

