Introduction
In today's digital communications, the sender and receiver of a message are rarely in direct contact. When you communicate with a friend, it is a private exchange of information, but the relevant information is recorded and stored on a central server.
You may not want the server that delivers your messages to read your private messages. In this case, end-to-end encryption (abbreviated "E2EE") is a viable option.
End-to-end encryption is a technical means of encrypting the communication between the receiver and the sender, so that only the two parties can decrypt the data. The origin of end-to-end encryption can be traced back to the 1990s, when Phil Zimmerman launched "Pretty Good Privacy" (the famous PGP).
Before we get into why E2EE is used and how it works, let’s first understand how unencrypted messaging works.
How Unencrypted Messaging Works
This section explains how a general smartphone messaging platform works. You install the app and create an account, which lets you communicate with other users who are doing the same. You write a message and enter your friend's username, posting it to a central server. The server forwards the message to your friend, successfully delivering it to its destination.

User A communicates with B. The two must pass data through the server (S) to establish a connection.
You can call it a "client-server model". The client (your phone) does very little, and all the heavy lifting is done by the server. Thus, the service provider acts as a middleman between you and the recipient.
In most cases, the data between A<>S and S<>B is already encrypted. For example, Transport Layer Security (TLS) is widely used to protect the connection between client and server.
TLS and similar security solutions prevent messages from being intercepted as they pass from client to server. While these measures prevent outsiders from accessing the information, the central server is responsible for encrypting the information and therefore has access to read the data. If A's data is encrypted using B's encryption key, the server cannot read or access it.
Without E2EE, the server would store this information in a database along with millions of other pieces of information. As has been proven time and again by large-scale data breaches, this vulnerable mechanism can lead to disaster for users.
How end-to-end encryption works
End-to-end encryption ensures that no one, not even the server, has access to your communications. Communications can be in the form of plain text, emails, files, video calls, etc.
Data is encrypted in apps like Whatsapp, Signal or Google Duo and (in theory) only the sender and the intended recipient can decrypt it. In end-to-end encryption, you start the process with a method called key exchange.
What is Diffie-Hellman key exchange?
The Diffie–Hellman key exchange, conceived by cryptographers Whitfield Diffie, Martin Hellman, and Ralph Merkle, is a powerful technique for generating and sharing secrets between parties in potentially dangerous environments.
In other words, even if the keys are created in an unsecure forum (even in the presence of bystanders), it will not affect the confidentiality of future communications. In the information age, this mechanism is extremely valuable because it allows two parties to communicate without physically exchanging keys.
The exchange itself involves a lot of numbers and fancy cryptography, which we won’t go into in detail here. Instead, let’s use a common analogy with paint colors: suppose Alice and Bob book a room at each end of a hotel corridor, and they want to share a specific color of paint, but they don’t want to reveal the specific color.
Unfortunately, the floor is full of spies. Suppose Alice and Bob cannot enter each other's rooms and can only interact in the hallway. In the hallway, they decide to paint their room yellow. They split the yellow paint in half and go back to their rooms.
In the room, they mix another secret color that no one knows. Alice uses a dark blue and Bob uses a dark red. Crucially, the spy cannot learn the secret color they used, but can see the resulting mixture because Alice and Bob now leave the room with a mixture of blue-yellow and red-yellow.
The two exchanged the mixture openly. Even if the spies saw it, it would not matter, they would not know what the dark shade was added. This is just an analogy, the real mathematical system is very complex, and guessing the secret "color" is not easy.
Alice and Bob take each other's mixture and return to the room again, then add their own secret color to the mixture.
Alice mixes the secret color "dark blue" with Bob's red and yellow to form a red-yellow-blue mixture
Bob mixes the secret color "dark red" with Alice's blue and yellow to form a blue-yellow-red mixture.
Both combinations have the same color and look the same. Alice and Bob have successfully created a unique color that the spy doesn't know about.
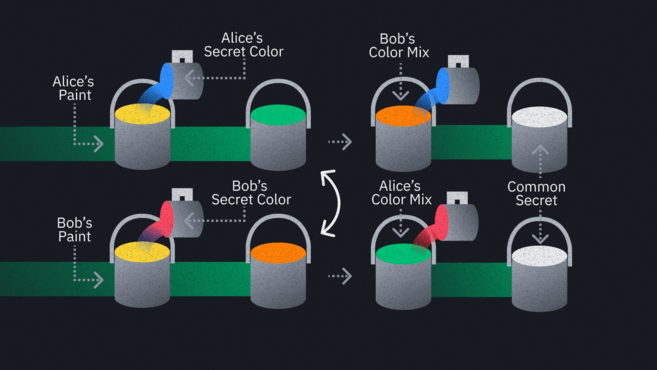
This is how we create shared secrets in an open environment. The difference is that instead of dealing with hallways and paint, we are dealing with insecure channels, public keys and private keys.
Information Exchange
Once other parties have their shared secret, they can use it as the basis for a symmetric encryption scheme. Current mainstream encryption schemes usually use multiple technologies to improve security, but these schemes are all "closed-door" and out of touch with actual needs, so they are of little effect. Once you connect with your friends through an E2EE application, encryption and decryption can only be done on your device unless there is a major software vulnerability.
Hackers, service providers, and law enforcement are all equal: If a service is truly end-to-end encrypted, any messages intercepted will be garbled.
➟ Want to start your digital currency journey? Buy Bitcoin on Binance now!
Pros and Cons of End-to-End Encryption
Disadvantages of end-to-end encryption
There is really only one downside to end-to-end encryption, and whether or not that is a downside is up to the person. To some, the value proposition of E2EE itself is questionable, since your messages cannot be accessed by anyone without the corresponding keys.
Opponents argue that this creates an opportunity for criminals, as they know that governments and technology companies cannot decrypt E2EE communications. And law-abiding individuals have no need to keep their messages and calls private. Many politicians agree. They call for legislation to allow regulators to intervene in the public's communications when necessary. Of course, this undermines the original purpose of using end-to-end encryption.
It is worth noting that applications that use E2EE are also subject to security risks. When two devices communicate, the messages may be mixed up, but they will appear normal on their respective endpoints (i.e. the laptops or smartphones at both ends). This is not a disadvantage of end-to-end encryption in itself, but it is something to be aware of.

The message appears in plain text before and after decryption.
E2EE technology guarantees that no one can read your data during transmission, but other threats still exist:
The device could be stolen: Without the PIN or if an attacker bypasses the PIN protection, they can read your messages.
Your device may be compromised: Your computer may have malware installed that monitors your information before and after you send it.
Another major risk is that a bad actor could forcefully intervene in the communication between the two parties through a man-in-the-middle attack. This usually happens at the beginning of the communication. If a key exchange is in progress, it will be difficult for you to be sure that the key exchange object is indeed your friend. You may have established a secret connection with the attacker without knowing it. Once the attacker receives your message and has the key to decrypt it, he can deceive your friend in the same way and peek or tamper with the relevant content as needed after intercepting the message.
To solve this problem, many apps have integrated a corresponding security code function, which may be in the form of a string of numbers or a QR code, which you can share with your contacts through a secure channel (offline is recommended). If the numbers match, you can be sure that a third party is not listening to your communications.
Advantages of end-to-end encryption
In a setup without any of the above vulnerabilities, E2EE is undoubtedly an effective way to improve confidentiality and security. Similar to onion routing, E2EE has won the favor of privacy activists around the world. This technology can be easily embedded in existing applications and serve all mobile phone users.
E2EE is more than just a mechanism for dealing with criminals and whistleblowers. It turns out that seemingly impregnable companies are also highly vulnerable to cyberattacks, resulting in unencrypted user information being leaked to criminals. The exposure of user data such as sensitive communications and identity documents can have a significant impact on personal lives.
If a company using E2EE is compromised, as long as the encryption is solid, hackers will not be able to steal any meaningful information. In the worst case, they will only get metadata. From a privacy perspective, this risk cannot be ignored, but the security of encrypted messages is indeed improved.
Summarize
In addition to the applications mentioned above, various free E2EE tools have been launched and promoted. Apple and Google have tailored iMessage and Duo for iOS and Android operating systems respectively, and software focusing on privacy and security has also been continuously released.
We must reiterate that end-to-end encryption is not a universal shield against all cyber attacks. However, with some simple settings and operations, this technology can significantly reduce the risk of information leakage and create a secure network communication environment. In addition to Tor, VPN, and cryptocurrencies, the E2EE communication program is also a powerful tool for protecting digital privacy.

