List of contents
Introduction
What is a private key?
What is a hardware wallet?
Why should you use a hardware wallet?
Weaknesses of hardware wallets
Review hardware wallet 2020
Ledger Nano S
Ledger Nano X
Trezor One
Model T safe
Cobo Vault
CoolWallet S
SafePal S1
KeepKey
Conclusion
Introduction
When it comes to cryptocurrencies, the wallet is the most important thing. The world of crypto is very dangerous – fraudsters are everywhere, and they have many strategies to steal user funds. Creating a strategy for securing your coins should be priority number one.
You have many storage options available, each with advantages and disadvantages. Most newcomers will probably use exchanges. The platform provides many people with their first experience with cryptocurrency, and allows its users to store their funds in online wallets. But technically, users don't control their coins. If an exchange is hacked or goes bankrupt, they may not get their funds back.
Users may not see the need to move their cryptocurrency off the exchange. They may not be skilled enough to do so, or even view a custodial solution as safer. After all, being your own custodian can result in the loss of funds if the user makes a mistake.
The idea of taking control of your own cryptocurrency may be a little intimidating. But from a security perspective, hardware wallets are the best choice. In this article, we will explain what it means, how it works, and why you should use it.
What is a private key?
Your private key is your passport to enter the cryptocurrency ecosystem. It's like a key in the real world – with the information inside, you can unlock your funds and spend them. If someone else finds out, they can steal your crypto. If you lose this key, you lose access to your coins – there is no forgot password button in a decentralized environment. There is also no bank you can contact to reverse a fraudulent transaction.
The point is that private keys must be stored safely and confidentially, because they are very valuable for cryptocurrency users. But it cannot be denied that hackers and fraudsters are always trying to steal them – using phishing or malware techniques to take coins from their rightful owners.
Storing a key is easy – a key is just a string of numbers and letters. You can write it down on a piece of paper and keep it in the safest place. However, to move funds, you must use this key on a device that can show proof that you are the person authorized to spend the coins.
What is a hardware wallet?
A hardware wallet is a device specifically designed to store private keys safely. This device is considered safer than a desktop or smartphone wallet, because it is not connected to the internet. This property significantly reduces the attack vectors available to malicious parties, as they cannot damage the device remotely.
A good hardware wallet guarantees that the private key never leaves the device. Usually private keys are designed not to be deleted and are located in a special place on the device.
Because the hardware wallet is always offline, it requires another machine to use it. The shape is designed so that it can be plugged into a PC or smartphone without any risk of private key leakage. From there, the wallet interacts with software that allows users to view their balance or make transactions.
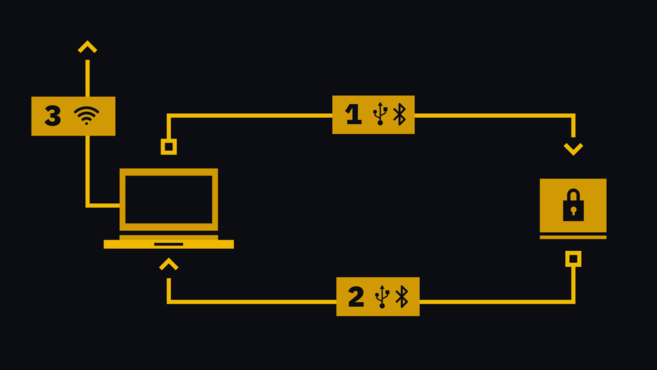
Once a user makes a transaction, it is sent to the hardware wallet (1 in the diagram below). Note that the transaction is not complete: it still needs to be signed by the private key on the device. Users confirm that the number and address are correct when prompted on the hardware. It is then signed and sent back to the software (2), which broadcasts it to the cryptocurrency network (3).
Why should you use a hardware wallet?
Wallets that store private keys on computers or smartphones connected to the internet make user funds vulnerable to many attacks. Malware can detect crypto-related activity on these devices and drain all funds.
Hardware wallets are like vaults that cannot be penetrated and have small gaps. When a user wants to make a transaction that the network will accept, the transaction is pushed through this loophole. Imagine, on the other side of the gap, there is a fairy doing cryptographic magic signing transactions. The elf would never leave the vault – because it had no door, and could not squeeze through the cracks. All it can do is accept the transaction, and push it back.
Even if someone gets hold of your hardware wallet, there is still additional protection in the form of a PIN code. The device will usually repeat the settings if the combination is entered incorrectly several times.
Funds that are not actively used – funds that are not spent, staked, lent, or traded – should be kept in cold storage. Hardware wallets provide an easy way to do this, even for users with limited technical knowledge.
Hardware wallets must have a backup to prevent problems in the event of loss, theft, or damage. At the start of using a wallet, users will usually be asked to note down their seed phrase – a string of words that can be used to recover funds on a new device. This gives whoever has it the authority to spend the coin, so it's best to keep it carefully. It is recommended that users write them down on paper (or engrave them on metal) and store them in a safe and confidential place.
Weaknesses of hardware wallets
Hardware wallets, just like other means of storage, have advantages and disadvantages. Even though it is one of the safest media for storing coins, this wallet still has several weaknesses. Smartphone/software wallets are easier to use, whereas hardware wallets are more complicated to operate (keeping in mind that two devices must be used to actually send funds).
Also, hardware wallets are not completely secure. Physical threats to users may force them to open their wallets to attackers. Or perhaps a skilled malicious party could exploit the device if they gain physical access to it.
However, to date, no hack has succeeded in retrieving private keys from hardware in the real world. When vulnerabilities are tracked and reported, manufacturers are generally quick to address them. This is not impossible – researchers have demonstrated several attacks against even the most popular wallets.
Supply chain attacks can also compromise the security of hardware wallet devices. This occurs when bad actors obtain wallets before they are sent to users. From there, they can tamper with it to weaken security and steal funds after users deposit coins.
Another downside is that hardware wallets put custody into your own hands. Many consider this to be an advantage, as there is no third party responsible for managing your funds. But this also means that if something goes wrong, there is no way out.
Review hardware wallet 2020
At Binance Academy, we prepared reviews of some of the most popular hardware wallets on the market.
Ledger Nano S
One of the most popular hardware wallets currently, the Ledger Nano S, is considered a must-have device for long-term holders and high-frequency traders. Please read our Ledger Nano S 2020 Review article.
Ledger Nano X
As the successor to the Ledger Nano S, the Nano X offers a number of impressive improvements, including wireless functionality and support for more cryptocurrencies. Read our article regarding the Ledger Nano
Trezor One
The product that sparked the hardware wallet industry still looks strong. Affordable yet powerful, Trezor One remains the gold standard for many cryptocurrency owners. Read our complete article regarding the Trezor One 2020 Review.
Model T safe
Trezor One uses steroids. Even though it's more expensive, you'll enjoy a touchscreen, support for more coins, and SD card compatibility for future upgrades. Read our full article on 2020 Trezor Model T Review.
Cobo Vault
Wallet for those who are preparing for the apocalypse. An air-gapped touchscreen device housed in a very strong metal casing – for those who are serious about security concerns. Read our complete article regarding the 2020 Cobo Vault Review.
CoolWallet S
With a shape similar to a credit card, the CoolWallet S is certainly an easy-to-remember device. Even though it has to make sacrifices in terms of UI/UX, this wallet will still appeal to those looking for something different. Read our complete article regarding the CoolWallet S 2020 Review.
SafePal S1
For its price, SafePal implements some very interesting security features, keeping its interaction with other devices to a minimum. Read our full article on SafePal S1 Review 2020 .
KeepKey
The device is sleek with ShapeShift integration. However, this wallet requires users to register in order to use the full features. Read our complete article regarding KeepKey Review 2020.
Did we miss your favorite device? Let us know by tweeting us at @BinanceAcademy!
Conclusion
The weaknesses of hardware wallets do not outweigh their advantages. When it comes to storing funds, nothing can beat the security of this wallet. Nothing can replace cold storage, which eliminates much of the risk of storing funds with you as custodian.
When looking for a hardware wallet, users should know a little about the various options available to them. There are a number of devices on the market, each with its own features, supported cryptocurrencies, and varying learning curves.

