The cryptoeconomics of slashing
Original author: Sreeram Kannan & Soubhik Deb (EigenLayer), a16z
Compilation: Overnight porridge, the way of DeFi
Of all the mechanisms designed for Proof of Stake (PoS) protocols, none is as controversial as slashing. Slashing provides a way to financially punish any specific node that does not act in accordance with the protocol in a targeted manner. It does this by taking away some or all of a validator's stake, without imposing externalities on other nodes that act in accordance with the protocol.
Slashing is unique to Proof of Stake (PoS) protocols because it requires the blockchain to be able to enforce penalties. Such enforcement is obviously not feasible in Proof of Work (PoW) systems, and is akin to burning mining hardware used by misbehaving nodes. This ability to apply punitive incentives opens up a new design space in blockchain mechanism design, and is therefore worthy of careful consideration.
Despite the clear benefits it provides in the form of “karma”, the main objection to slashing is that nodes can be over-slashed due to inadvertent mistakes such as running outdated software. As a result, many protocols avoid slashing and instead rely on so-called token toxicity (i.e., the loss of value of the underlying token if the protocol is successfully attacked). Many believe that stakers will view this toxicity as a threat to compromise the security of the protocol. In our evaluation, token toxicity is not sufficient to prevent adversarial attacks in certain typical scenarios. In fact, in this case, the cost incurred by the adversary to attack and subvert the protocol (called the bribe cost) is essentially zero.
In this article, we show how slashing can be incorporated into the mechanism design of PoS protocols in order to significantly increase the bribe cost that any adversary can incur. In the presence of bribes, slashing guarantees a high and measurable bribe cost for decentralized protocols as well as for protocols (centralized or decentralized) that do not satisfy the token toxicity assumption.
Situations that could lead to bribery and lack of token toxicity are ubiquitous. Many PoS protocols avoid falling into either of these two categories by having a tight-knit community, which is only feasible at a small scale. (1) Delegating validation to a small group of well-known and legally regulated node operators by relying on strong leadership to steer them in the right direction; or (2) Relying on concentrated staking of tokens within a small group. None of these solutions are entirely satisfactory for developing a large and decentralized community of validating nodes. If a PoS protocol is characterized by only a few validators (or, in extreme cases, only one validator), then it would be good to have a way to penalize these large validators to prevent them from engaging in hostile behavior.
In the rest of this article, we:
Propose a model to analyze complex bribery attacks;
Showing that PoS protocols without slashing mechanisms are vulnerable to bribery attacks;
Demonstrated that PoS protocols with slashing mechanisms are quantifiably secure against bribery attacks;
As well as discussing some of the shortcomings of forfeiture and proposing mitigating measures;
1. Model
Before we introduce the case for slashing, we first need a model under which we will conduct our analysis. The two most popular models for analyzing PoS protocols (the Byzantine model and the game theory equilibrium model) fail to capture some of the most destructive real-world attacks, for which slashing acts as a strong deterrent. In this section, we discuss these existing models to understand their shortcomings and propose a third model (which we call the bribery analysis model). Although the bribery analysis model is able to simulate a large number of attacks, it has not yet been used to analyze many protocols.
Existing Models
In this section, we briefly describe the Byzantine and game-theoretic equilibrium models and their shortcomings.
Byzantine Model
The Byzantine model states that at most a certain percentage (?) of nodes can deviate from the actions prescribed by the protocol and perform any action of their choice, while the rest of the nodes still follow the protocol. Proving that a particular PoS protocol is resistant to Byzantine actions that adversarial nodes can take is a non-trivial problem.
For example, consider the longest-chain PoS consensus protocol, where liveness takes precedence over safety. Early research on the safety of the longest-chain consensus focused on demonstrating safety against one specific attack (namely, a private double-spend attack, where all Byzantine nodes privately collude to build an alternative chain and then reveal it only when it is longer than the longest chain). However, the nothing-at-stake phenomenon provided an opportunity to propose many blocks using the same staked stake and use independent randomness to increase the probability of building a longer private chain. It was not until much later that extensive research was conducted to show that certain constructions of the longest-chain PoS consensus protocol could resist all attacks for certain values of ?. (For more details, see Everything is a Race and Nakamoto Always Wins and PoSAT: Proof-of-Work Availability and Unpredictability, Without the Work)
A whole class of Byzantine Fault Tolerant (BFT) consensus protocols that prioritize safety over liveness. They also need to assume a Byzantine model to prove that, for an upper bound of ?, these protocols are deterministically secure against any attack. (For more details, see HotStuff: BFT Consensus in the Lens of Blockchain, STREAMLET, Tendermint.)
While the Byzantine model is useful, it does not take into account any economic incentives. From a behavioral perspective, ? of these nodes are completely adversarial in nature, while (1-?) of the nodes are fully compliant with the protocol specification. In contrast, a large portion of nodes in a PoS protocol may be motivated by economic gain and run a modified version of the protocol that favors their own interests rather than simply complying with the full protocol specification. As a prominent example, consider the case of the Ethereum PoS protocol, where most nodes today do not run the default PoS protocol, but instead run the MEV-Boost modification, because participating in the MEV auction market generates additional rewards that are not available from running the exact specification protocol.
Game Theory Equilibrium Model
Game theory equilibrium models attempt to address the shortcomings of the Byzantine model by using solution concepts such as Nash equilibrium to investigate whether rational nodes have an economic incentive to follow a given strategy when all other nodes also follow the same strategy. More specifically, assuming that everyone is rational, the model investigates two questions:
If all other nodes follow the protocol-mandated policy, will it bring me the greatest economic benefit to implement the same protocol-mandated policy?
If every other node is executing the same protocol deviation strategy, is it the most incentivized for me to still follow the protocol policy?
Ideally, the protocol should be designed to ensure that the answer to both questions is "yes".
An inherent shortcoming of the game-theoretic equilibrium model is that it excludes scenarios where exogenous agents could influence node behavior. For example, an external agent could set bribes to incentivize rational nodes to act in accordance with their prescribed strategy. Another limitation is that it assumes that each node has independent agency and can decide for itself what strategy to adopt based on its ideology or economic incentives. This does not cover scenarios where a group of nodes collude to form a cartel, or where economies of scale encourage the creation of a centralized entity that essentially controls all staked nodes.
Separating bribery costs from bribery benefits
Some researchers have proposed a bribery analysis model to analyze the security of any PoS protocol, although no one has used it for a deeper analysis. The model begins by asking two questions: (1) What is the minimum cost for any adversary to successfully perform a security or liveness attack on the protocol? (2) What is the maximum profit that an adversary can gain from successfully performing a security or liveness attack on the protocol?
The opponent in question might be:
Nodes that unilaterally deviate from the policy specified in the protocol;
A group of nodes actively cooperating with each other to subvert the protocol, or
External adversaries who attempt to influence the decisions of many nodes through external actions such as bribery;
Calculating the costs involved requires taking into account any costs of bribes, any financial penalties for executing Byzantine strategies, etc. Similarly, calculating profits is all-encompassing, including in-protocol rewards obtained from successfully attacking the protocol, any value captured from DApps sitting on top of the PoS protocol, holding protocol-related derivatives on secondary markets, and profiting from volatility caused by the attack, etc.
Comparing the lower bound of the minimum cost for any adversary to launch an attack (bribe cost) with the upper bound of the maximum profit the adversary can extract (bribe profit) shows that attacking the protocol is economically profitable (note: this model has been used to analyze Augur and Kleros), which gives us a simple equation:
Bribery Profit – Bribery Cost = Total Profit
If the total profit is positive, then the adversary has an incentive to launch an attack. In the next section, we consider how increasing the cost of bribery through slashing can reduce or eliminate the total profit. (Note that a simple example of an upper bound on bribery profit is the total value of assets protected by the PoS protocol. More complex bounds can be established to take into account circuit breakers that restrict the transfer of assets over a period of time. A detailed study of methods to reduce and limit bribery profit is beyond the scope of this article.)
2. Slashing
Slashing is a way for the PoS protocol economy to punish a node or group of nodes for executing a policy that is provably different from a given protocol specification. Typically, to implement any form of slashing, each node must have previously committed a certain amount of stake as collateral. Before diving into the analysis of slashing, we will first look at PoS systems with native tokens that rely on token toxicity as an alternative to slashing.
We focus primarily on studying slashing mechanisms for safety violations, rather than liveness violations. We make this restriction for two reasons: (1) safety violations are fully attributable to some BFT-based PoS protocols, but liveness violations are not attributable to any protocol, and (2) safety violations are often more severe than liveness violations, resulting in loss of user funds rather than the inability to post transactions.
What would be the problem if there were no fines?
Consider a PoS protocol consisting of N rational nodes (no Byzantine or altruistic nodes). Let us assume, for simplicity of calculation, that each node deposits an equal amount of stake. We first explore how token toxicity does not warrant significant bribery costs. For the sake of consistency throughout the document, we also assume that the PoS protocol used is a BFT protocol with a ⅓ opponent threshold.
Token toxicity is not enough
A common view is that token toxicity protects staking protocols from any attacks on their security. Token toxicity implies the fact that if the protocol is successfully attacked, the underlying tokens used to stake in the protocol will lose value, thereby disincentivizing participating nodes to attack the protocol. Consider a scenario where 1/3 of the stakers join forces: these nodes can cooperate to undermine the security of the protocol. But the question is whether this can be done with impunity?
If the total valuation of the tokens deposited at stake depends strictly on the security of the protocol, then any attack on the security of the protocol could potentially drive its total valuation down to zero. Of course, in practice it doesn’t go directly to zero, but to some smaller value. But to show the strongest possible case for token toxicity, we’ll assume here that token toxicity works perfectly. The bribe cost of any attack on the protocol is the tokens held by rational nodes attacking the system, all of which they must be willing to lose.
We now analyze the incentives for collusion and bribery in a PoS system with token toxicity without slashing. Assume that the external adversary sets the bribe conditions as follows:
If a node follows the strategy instructed by the adversary but the attack on the protocol is unsuccessful, the node receives a reward B1 from the adversary.
If the node executes according to the strategy instructed by the adversary and the attack on the protocol is successful, the node receives a reward B2 from the adversary.
For a node that deposits equity S, we can derive the following payoff matrix, where R is the reward for participating in the PoS protocol:
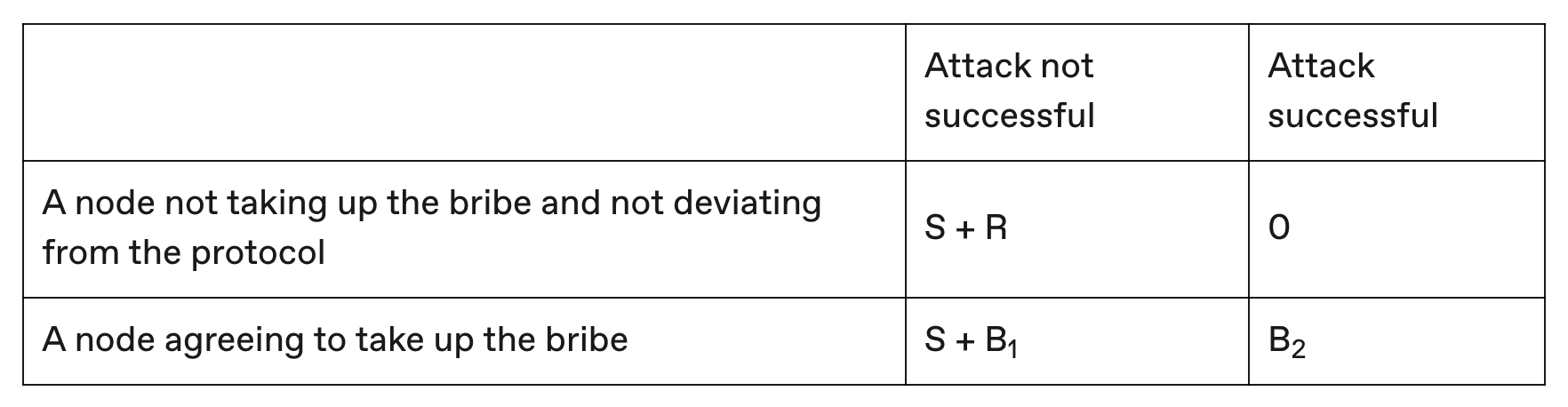
Assume that the adversary sets the bribe payoff to B1>R and B2>0. In this case, no matter what strategy the other nodes take (the dominant strategy), the payoff from accepting a bribe from the adversary is higher than any other strategy the node could take. If 1/3 of the other nodes end up accepting the bribe, they can attack the security of the protocol (this is because we assume we are using a BFT protocol with an adversary threshold of ⅓). Now, even if the current node does not accept the bribe, the token will lose its value anyway due to token toxicity (the top right cell in the matrix).
Therefore, it is incentive compatible for nodes to accept a bribe of B2. If only a small fraction of nodes accept the bribe, the token does not lose value, but the node benefits from giving up the reward R and instead receiving B1 (the left column in the matrix). If 1/3 of the nodes agree to accept the bribe and the attack succeeds, the total cost to the adversary of paying the bribe is at least ?/3 × B2, which is the cost of the bribe. However, the only condition on B2 is that it must be greater than zero, so B2 can be set close to zero, which means that the cost of the bribe is negligible. This attack is called a "P+ε" attack.
One way to summarize the impact is that token toxicity is not enough because the impact of bad behavior is socialized: token toxicity completely devalues the value of the token, affecting good and bad nodes equally. On the other hand, the benefits of bribery are privatized and limited to those rational nodes that actually accept the bribe. There are no one-to-one consequences for those who accept the bribe, that is, this system has no effective version of "karma".
Is Token Toxicity Always Effective?
Another misleading claim prevalent in the ecosystem is that every PoS protocol can gain some degree of protection from token toxicity. But in fact, exogenous incentives for token toxicity cannot be extended to certain categories of protocols where the valuation of tokens used as staked face value does not depend on the protocol running securely. One such example is a re-staking protocol like EigenLayer, where ETH used by the Ethereum protocol is reused to guarantee the economic security of other protocols.
Consider re-staking 10% of ETH using EigenLayer to perform validation on a new sidechain. Even if all stakers in EigenLayer cooperate to misbehave by attacking the security of the sidechain, the price of ETH is unlikely to drop. Therefore, token toxicity is not transferable to the re-staking service, which means the cost of bribery is zero.
Is the penalty of no help?
In this section, we explain how slashing can significantly increase the cost of bribery in two scenarios:
Decentralized protocols under bribery;
PoS protocol with toxic and non-transferable tokens;
Preventing Bribery
Protocols can use slashing to drastically increase the cost of corruption for an external adversary attempting a bribe attack. To better explain this, we consider the example of a BFT-based PoS chain that requires a stake of the chain’s native token, and that must compromise at least ⅓ of the total stake in order to perform any successful attack on its security (in the form of double signing). Assume that an external adversary is able to bribe at least ⅓ of the total staked stake to perform a double signing. Proof of the double signing can be submitted to a canonical fork that slashes nodes that accept bribes from the adversary and double-sign. Assuming that each node stakes S tokens and all slashed tokens are destroyed, we obtain the following payoff matrix:
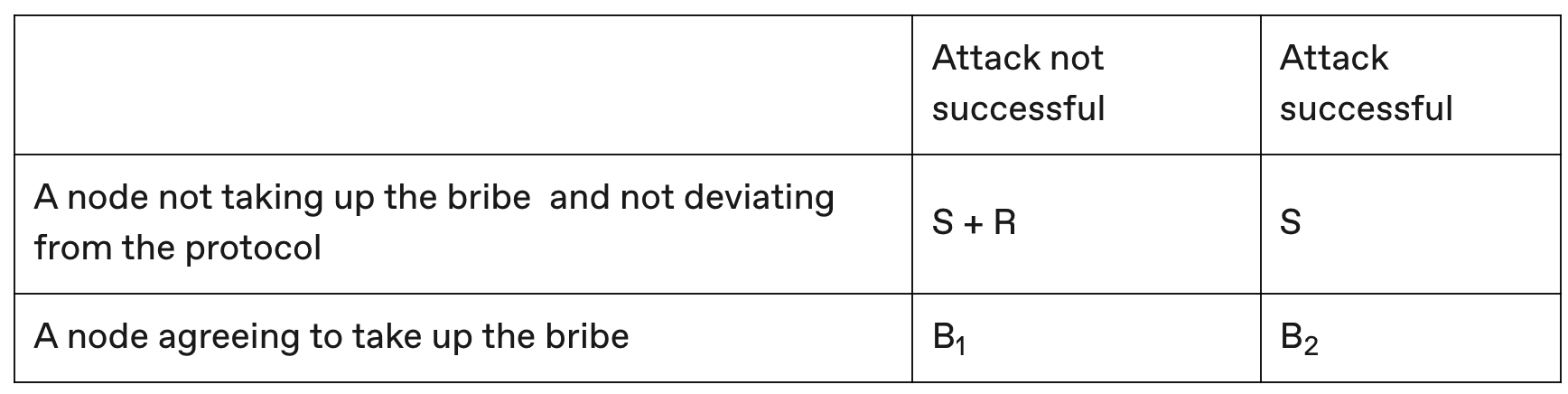
With slashing, if a node agrees to accept the bribe and the attack is unsuccessful, then its stake S is slashed in the canonical fork (the lower left cell of the matrix), in contrast to the previous bribery scenario without slashing. On the other hand, even if the attack is successful, the node does not lose its stake S in the canonical fork (the upper right cell of the matrix). If ⅓ of the total stake needs to be bribed for the attack to succeed, the bribe cost must be at least ?/3 × S, which is significantly higher than the bribe cost without slashing.
Protection against token toxicity and non-transferability
In some PoS protocols where token valuation is not affected by protocol security, token toxicity is non-transferable. In many such systems, the PoS protocol sits on top of another base protocol. The base protocol then shares security with the PoS protocol by deploying a dispute resolution mechanism on the base protocol to resolve disputes and giving the base protocol the power to provably slash nodes associated with the PoS protocol.
For example, if a Byzantine action in a PoS protocol can be objectively attributed to a hostile node in the base protocol, then its stake in the PoS protocol will be forfeited in the base protocol. An example of such a PoS protocol is EigenLayer, which features restaking, enabling different verification tasks to derive security from the Ethereum base protocol. If a node restakes a Byzantine strategy in a verification task on EigenLayer, where the Byzantine behavior can be objectively attributed, then it can be proven that the node is hostile on Ethereum and its staked stake will be forfeited (no matter how large the stake is).
Assuming that each node heavily stakes S, all forfeited tokens are destroyed, and receives a reward R from participation, we construct the following reward matrix:
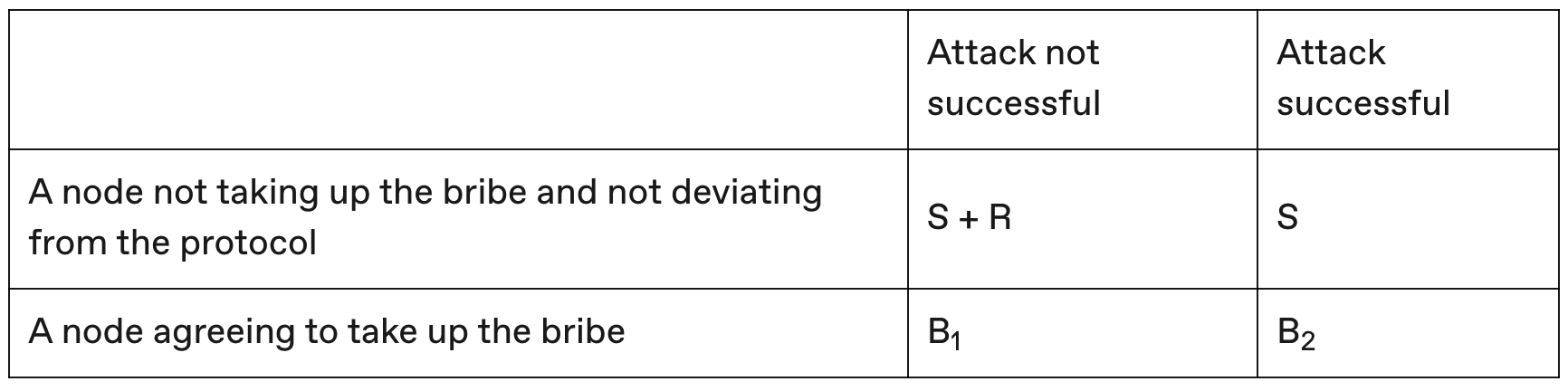
Since we are considering validation tasks where any Byzantine behavior can be objectively attributed, even if a node behaves honestly but the attack succeeds, the node will not be slashed on Ethereum (the top right cell in the matrix). On the other hand, a node that agrees to accept a bribe and exhibits hostile behavior will be objectively slashed on Ethereum (the bottom row in the matrix). If ⅓ of the total stake needs to be bribed for the attack to succeed, the bribe cost is at least ?/3 × S.
We also considered the extreme case where all staked interest in the PoS protocol is concentrated in the hands of a single node. This is an important scenario because it foreshadows the eventual centralization of interest. Given our assumption that there is no token toxicity for heavily staked tokens, without slashing, the centralized node could operate in a Byzantine manner without being punished. But with slashing, this Byzantine centralized node can be punished in the base protocol.
Slashing of Attributed Attacks vs. Slashing of Non-Attributed Attacks
There is an important subtle difference between slashing for attributable attacks and slashing for non-attributable attacks. Consider the case of security failures in Byzantine fault-tolerant protocols. Typically, they stem from Byzantine behavior of double-signing, intended to weaken the security of the blockchain - this is an example of an attributable attack, as we can pinpoint which nodes attacked the security of the system. On the other hand, Byzantine behavior of censoring transactions to weaken the liveness of the blockchain is an example of a non-attributable attack. In the former case, slashing can be algorithmically achieved by providing evidence of the double signature to the blockchain's state machine.
In contrast, since there is no algorithmic way to prove whether a node is actively censoring, slashing for censoring transactions cannot be done algorithmically. In this case, the protocol may have to rely on social consensus to enforce slashing. A certain percentage of nodes can execute a hard fork to specify slashing for nodes that are accused of engaging in censorship. Only when social consensus emerges will such a hard fork be considered a canonical fork.
We define the bribe cost as the minimum cost of performing a security attack. However, we require a property of PoS protocols called accountability, which means that if the protocol loses security, there should be a way to attribute the blame to a small fraction of nodes (⅓ of the nodes for BFT protocols). It turns out that the analysis of which protocols are responsible is subtle (see this paper on forensics of BFT protocols). Furthermore, it turns out that dynamically available longest-chain protocols (such as PoSAT) are not accountable (see this paper for the trade-offs between dynamic availability and accountability, and some ways to resolve these fundamental trade-offs.)
3. Pitfalls and Mitigation Measures of Confiscation
Like any technology, slashing comes with its own risks if not implemented carefully:
1. Client misconfiguration/key loss. One of the pitfalls of slashing is that innocent nodes may be disproportionately punished for unintentional errors (such as misconfigured keys or lost keys). To address concerns about excessive slashing of honest nodes due to inadvertent errors, protocols can adopt certain slashing curves that will provide lenient penalties when only a small amount of staked stake behaves inconsistently with the protocol, but will impose severe penalties when the staked stake executed on a strategy that conflicts with the protocol exceeds a threshold ratio. For example, Ethereum 2.0 adopts this approach.
2. Credible slashing threat as a lightweight alternative. If a PoS protocol does not implement algorithmic slashing, it can instead rely on the threat of social slashing, that is, in the event of a security failure, nodes will agree to point to a hard fork where misbehaving nodes lose funds. This does require significant social coordination compared to algorithmic slashing, but as long as the threat of social slashing is credible, the game theory analysis presented above continues to apply to protocols that have no algorithmic slashing but rely on committed social slashing.
3. Social slashing for liveness failures is fragile. Social slashing is necessary to punish unattributable attacks, such as liveness failures like censorship. While social slashing can theoretically be implemented for unattributable failures, it is difficult for newly joined nodes to verify whether such social slashing occurred for the right reason (censorship) or because the node was wrongly accused. When social slashing is used for attributable failures, there is no such ambiguity, even without a software implementation of the slashing. Newly joined nodes can continue to verify that such slashing is legitimate because they can check their double signatures, even if only manually.
4. How to deal with the confiscated funds?
There are two possible ways to deal with forfeited funds: destruction and insurance.
1. Destruction: The straightforward way to deal with confiscated funds is to simply destroy them. Assuming the total value of the tokens has not changed as a result of the attack, the value of each token will increase proportionally and will be more valuable than before. Instead of identifying the parties harmed by the security failure and compensating only them, destruction indiscriminately benefits all non-attack token holders.
2. Insurance: A more complex mechanism for distributing forfeited funds that has not been studied involves insurance bonds issued against forfeitures. Customers transacting on the blockchain may obtain these insurance bonds in advance on the blockchain to protect themselves from potential security attacks and insure their digital assets. When a security-compromising attack occurs, algorithmic forfeitures on stakers generate a fund that can then be distributed to insurers in proportion to the bonds.
5. Current Status of Confiscation in the Ecosystem
To our knowledge, the benefits of slashing were first explored by Vitalik in this article in 2014. The Cosmos ecosystem built the first effective slashing implementation into its BFT consensus protocol, which enforces slashing when validators do not participate in proposing blocks or double-sign ambiguous blocks.
Ethereum 2.0 also incorporates slashing into its PoS protocol. Validators in Ethereum 2.0 can be punished for making ambiguous proofs or proposing ambiguous blocks. Slashing misbehaving validators is how Ethereum 2.0 achieves economic finality. A validator can also be punished relatively mildly for missing proofs or if it does not propose a block when it should have.
***
PoS protocols without slashing mechanisms are extremely vulnerable to bribery attacks. We use a new model (the Bribery Analysis Model) to analyze complex bribery attacks, and then use it to show that PoS protocols with slashing mechanisms have quantifiable anti-bribery security. While there are flaws in incorporating slashing into PoS protocols, we propose some possible ways to mitigate these flaws. We hope that PoS protocols will use this analysis to evaluate the benefits of slashing in certain situations - potentially improving the security of the entire ecosystem.
