With the fall of FTX in the crypto world, in the days after the FTX incident on November 9, major centralized exchanges (CEX) have announced that they will announce or directly disclose the exchange’s Merkle-tree proof-of-reserves in the near future, hoping to make the originally opaque CEX asset reserves transparent through Merkle proofs, thereby proving the asset reserves of their own CEX centralized exchanges and proving that the funds have not been misappropriated or moved.
There is no doubt that the fall of FTX has cast a shadow on the black box operation mechanism of the entire CEX, and even an indelible stain, while the Merkle tree reserve proof seems to bring a glimmer of hope to this industry. As far as this technical solution is concerned, it has been proposed and applied a few years ago. So what exactly is the "Merkle proof", and how to prove that the user assets in the exchange have not been misappropriated, and can it prove that their assets are safely kept?
The Merkle tree is the data structure of cryptocurrencies such as Bitcoin and Ethereum. It is a cryptographic technology that can compress data. By using the Merkle tree, multiple data can be merged into one data, and the larger data summary results can be stored. At the same time, cryptographic means can be used to prove that the corresponding data is compressed in the summary results. In addition, by verifying the data integrity of the Merkle tree root, the integrity of all data that constitute the Merkle tree can be proved.
The leaves of the Merkle tree are composed of the hash values of each data in the data set. Specifically, the construction of the leaves is to connect two adjacent hash values, package them together and hash them again to generate a parent hash value. The hash value finally packaged to the top layer is called the Merkle root, the root hash value (Merkle Root). The hash value of the Merkle root contains the hash characteristics of all data, which means that if the data is tampered with on which node, it will present a completely different value, that is, the hash value recorded in the Merkle tree cannot be tampered with.
Assuming that our account and balance information is recorded in the Merkle root as data A, we can use the following data as proof to verify whether data A is recorded in the Merkle tree:
Data A (account and balance information)
B's hash value
Hash value of CD
Root Hash
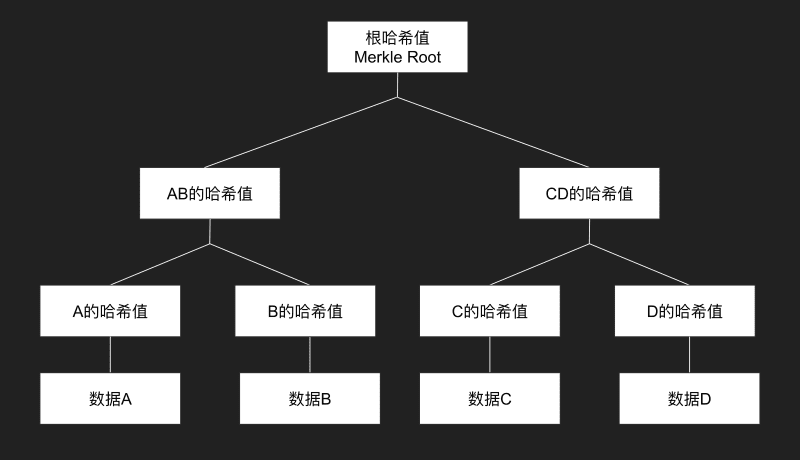
Figure 1: Schematic diagram of Merkle tree data storage
Next, we calculate the hash of A through data A, and then calculate the hash of AB together with the hash of B. Finally, we use the hash of AB and the hash of CD to calculate the root hash. We compare the root hash we calculated with the root hash we obtained. If they are equal, it verifies that A is recorded in the Merkle tree.
If the assets of all users of a centralized exchange are recorded in the Merkle tree and proven to be authentic, the exchange can prove to each user that "the data record has been added to the Merkle tree and the user's assets are real" without disclosing other users' information.
How is this proof system used in practice? The trust of this system is based on the Merkle tree (dynamic deterrence) and audit (third-party professional responsibility). Dynamic deterrence is based on the fact that any user can serve as a detection node and prove that they are not on the Merkle tree, thereby revealing that the root provided by the exchange is fake. There is no other function, such as the root does not have the function of showing the sum of all user balances. Both are indispensable. It does not mean that relying solely on cryptographic proof methods can prove all problems. In practice, it is much more complicated than in theory, and there are many points that can be manipulated.
However, compared to the previous CEX which only had audit monitoring, the addition of the Merkle tree actually gives users the right to blow the whistle, allowing the CEX's asset reserves to be monitored in a decentralized manner to a certain extent. This is a great improvement and a good thing for the current market where confidence is strongly insufficient.
However, can the Merkle tree reserve proof prove that the user's assets are safe? Although through the Merkle proof, we can verify that our assets are recorded in an unalterable hash, but can this fully prove that the funds have not been misappropriated or moved?
Centralized exchanges have a large number of transactions per second, and it is impossible to update the root of the tree every second, so the root we see is probably not the latest one. But from another perspective, the Merkle tree calculation is mainly composed of a series of hash function calculations, and the hash function calculation speed is relatively fast, so in this sense, the update frequency will not be very slow.
In addition to the above-mentioned update frequency issues, the Merkle Tree Reserve Proof has the following important issues:
Front-end fraud problem: Merkle tree data is stored on the exchange's own server. The front-end page where users interact with the exchange is controlled by the exchange. The exchange may return a fake page to deceive users, which may lead to front-end fraud. This problem needs to be solved through third-party software supervision.
The credibility issue of third-party audits: Similarly, in traditional finance, there are often audit errors and even illegal behavior. Although this has not yet been widely used in the Crypto field, audits are not always objective and fair.
Related-party transactions, debt relationships, margin transactions, etc. cannot be reflected through reserves.
The cryptocurrency market needs more open and transparent information. Merkle tree reserve proof becoming a standard feature of Crypto exchanges will help establish industry norms and rebuild user confidence.
Whether for investors or users, ensuring the safety of funds is always a sword of Damocles hanging over the heads of every practitioner. In this bear market, no matter who falls or who is left, the wheel of Web3 will not stop and will roll forward.
