introduction
Fake recharge attacks refer to attackers taking advantage of loopholes or system errors in the exchange's recharge process to send forged transaction information to the exchange's wallet address. These forged transaction information are mistaken by the exchange as real recharge requests, and the corresponding digital assets or currencies are added to the attacker's account. In this way, the attacker can obtain unpaid digital assets, resulting in asset losses for the exchange.
This article aims to explore in depth how fake deposit attacks break through the defense mechanisms of exchanges. We will analyze the principles of fake deposit attacks and reveal the vulnerabilities and strategies used by attackers. At the same time, we will analyze fake deposit attacks through examples to better understand the attack methods and impacts. In addition, we will also discuss the emergency measures and preventive measures that exchanges can take to deal with fake deposit attacks, and provide relevant suggestions for protecting assets and dealing with similar attacks.
Recharge principle analysis
Before understanding fake recharge, we need to first understand the recharge principle of the exchange.
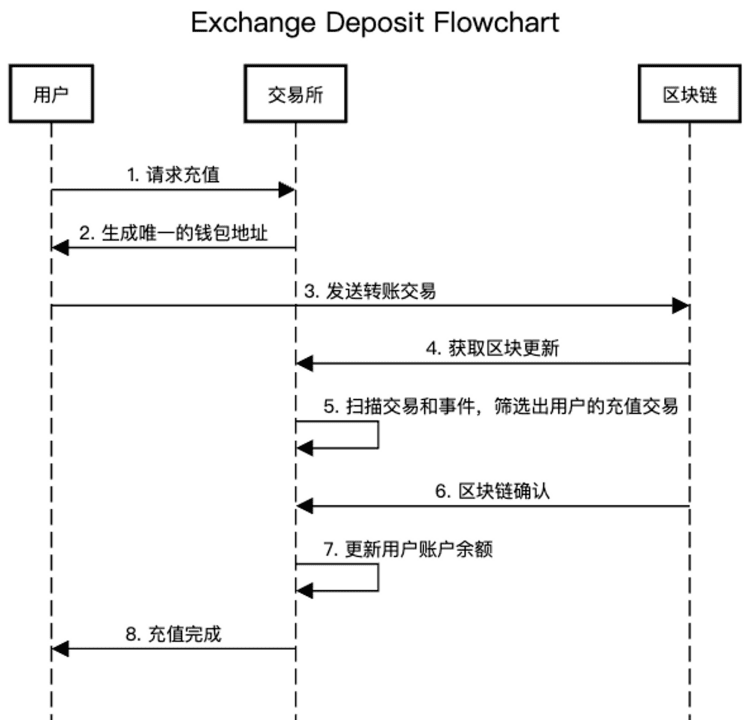
A typical process is as follows:
1. Wallet address generation
The exchange assigns each user a unique wallet address to receive the user's top-up. These addresses are usually automatically generated by the exchange's system. When a user makes a top-up, they need to send the digital asset to a specific wallet address in the exchange account.
2. Blockchain ledger scanning
The exchange's nodes will synchronize with other nodes in the blockchain network to obtain the latest blockchain status and transaction information. When the exchange node receives a new block, it will extract the user's recharge transaction ID and the corresponding amount from the transaction content contained in the block or the transaction execution event triggered by the block, and add it to the list of pending recharges.
3. Confirm the deposit
Exchanges usually require that transactions receive a certain number of confirmations in the blockchain network before they are considered valid. Confirmation means that the transaction is referenced by a certain number of blocks and verified and confirmed by other miners. The number of confirmations set by the exchange can vary depending on the digital asset and network.
as the picture shows:
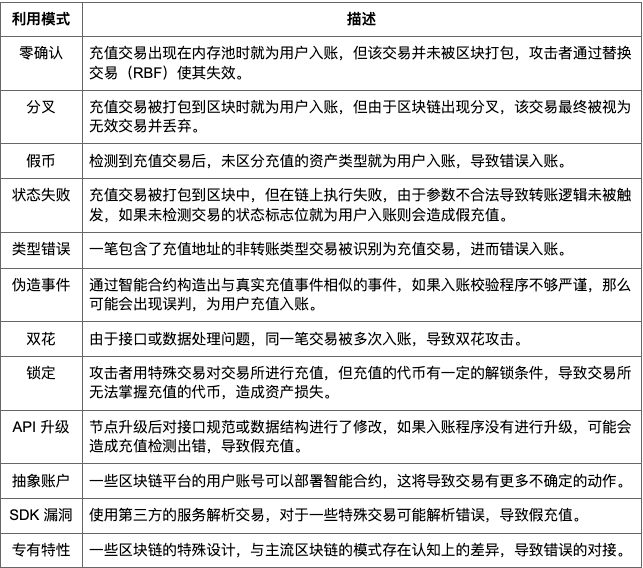
Fake recharge attack mode
Exchanges are the hardest hit by hacker attacks, so exchanges usually place their servers behind multiple defense systems, and even host their core services for fund management offline. However, due to the blockchain system's requirement for data integrity, malicious transactions will not be intercepted by the peripheral security system.
It should be noted that fake recharge attacks are not loopholes in the blockchain, but attackers use some characteristics of the blockchain to construct special transactions. These malicious transactions will cause exchanges to mistake them for real recharge requests, or process the same recharge request multiple times. After long-term actual combat, the SlowMist security team has summarized several common fake recharge attack methods:
Since 2018, the SlowMist security team has disclosed several fake recharge attacks, including:
USDT Fake Transfer Security Risk Analysis [1]
EOS Fake Deposit (hard_fail state attack) Red Alert Details Disclosure and Repair Solution [2]
Details of the Ethereum token “fake recharge” vulnerability and its fix [3]
Analysis of Bitcoin RBF Fake Deposit Risk [4]
In addition to these public fake recharge attacks, there are also several classic attack methods that we have not disclosed, as well as some universal attack methods. For example:
Bitcoin Multi-Signature Fake Deposit
Ripple Partial Payment Fake Top-up
Filecoin double spending fake recharge
TON rebound fake deposit
If you want to know more details, please contact us for further discussion.
Case Analysis: TON Rebound Fake Recharge
Almost all blockchains have the problem of fake recharge, but some attacks are easy to avoid, while others require very in-depth research on the characteristics of blockchain to avoid being harmed.
Taking TON’s fake deposit as an example, we will show you how cunning attackers can exploit the characteristics of TON to attack exchanges.
TON (The Open Network) is a blockchain project initiated by the well-known communication software Telegram, which supports the deployment of smart contracts on users' accounts.
When the exchange connects to TON recharge, according to the method described before, it will first generate a recharge address for the user, and then the user will transfer the assets to the recharge address, and finally confirm the account.
How does an exchange confirm that a transaction is from its user? Let’s use the RPC interface to check a normal transfer:
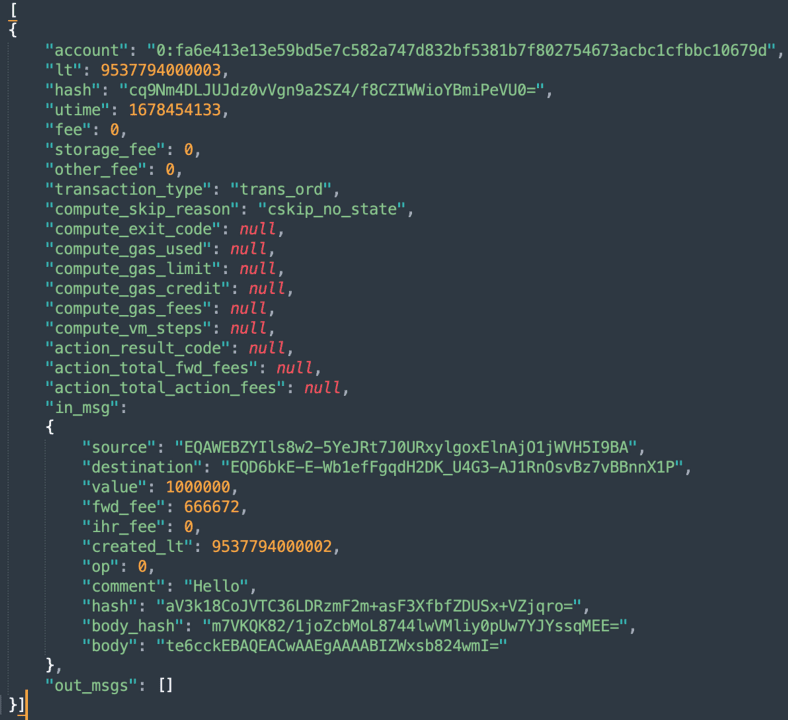
Usually the exchange will determine whether the destination in in_msg is the user's deposit address. If so, the amount value will be converted according to the accuracy and then credited to the user. But is this safe?
TON transactions have a feature that almost all internal messages sent between smart contracts should be bounceable, that is, their bounce flag should be set. In this way, if the target smart contract does not exist, or throws an unhandled exception when processing this message, the message will be "bounced" back and carry the balance of the original value (minus all message transfers and gas fees).
That is to say, if a malicious attacker sets the bounce flag to transfer money to an account that has not deployed a contract, the deposited amount will be bounced back to the original account after deducting the handling fee. The exchange detected the user's deposit record, but did not expect that the deposited coins would actually return to the attacker's account.
Let's take a look at this transaction. Compared with a normal transaction, we can find that there is an extra out_msg. This out_msg is the operation of funds being bounced back to the original account.
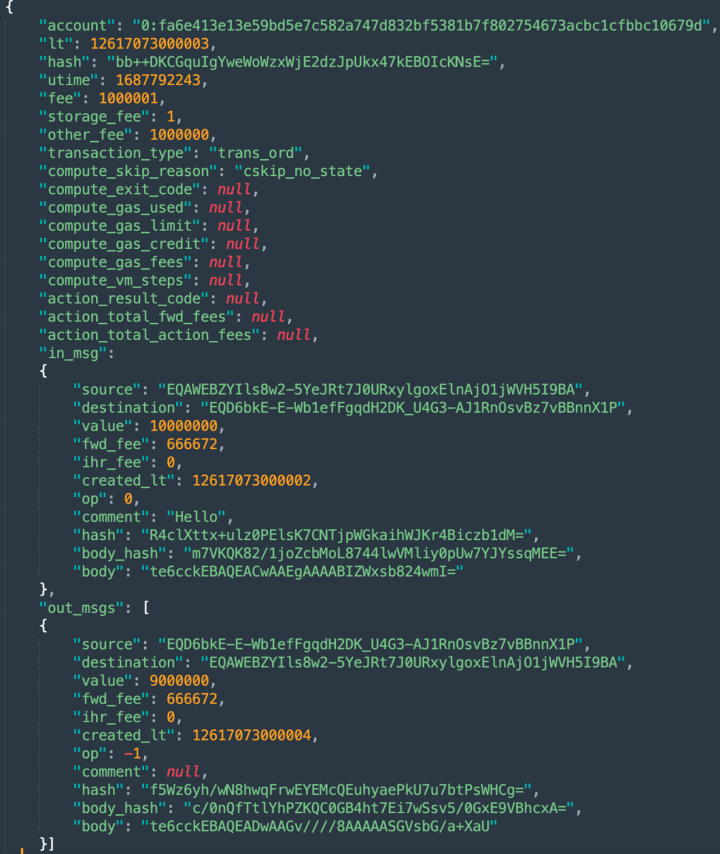
If the exchange only verifies in_msg, it will mistakenly credit the attacker and cause asset losses on the platform.
Best practices for preventing fake deposit attacks
Some basic strategies to prevent fake recharge attacks are:
1. Multiple confirmation mechanism: Set multiple confirmation requirements for recharge to ensure that the transaction is considered valid only after sufficient confirmation on the blockchain. The number of confirmations should be set according to the security of different digital assets and the confirmation speed of the blockchain;
2. Strict transaction matching: When filtering user transactions from the block, only transactions that completely match the normal transfer pattern can be automatically set as received, and the balance change must be checked at the end;
3. Risk control system: Establish a comprehensive risk control system to monitor and detect abnormal trading activities. The system can identify potential risks and abnormal behaviors by analyzing factors such as recharge patterns, transaction frequency, and transaction size;
4. Manual review: For transactions with larger amounts or high risks, a manual review mechanism is used for additional review. Manual review can increase the credibility of transactions, detect abnormal transactions, and prevent malicious recharges;
5. API security: Perform security authentication and authorization on external API interfaces to avoid unauthorized access and potential vulnerabilities. Regularly review the security of API interfaces and perform timely security updates and repairs;
6. Restrict withdrawals: After a deposit occurs, temporarily restrict users from withdrawing deposited assets. This gives the exchange enough time to confirm the validity of the deposit and prevent potential fake deposit attacks;
7. Security Updates: Update the exchange software and systems in a timely manner to fix possible security vulnerabilities. Continuously monitor the security status of the exchange and work with cybersecurity experts to conduct regular security audits and penetration tests.
To prevent fake deposits on a specific blockchain, you need to read the official documentation to understand the characteristics of the transaction.
Badwhale Fake Recharge Detection System
The SlowMist security team has developed the Badwhale fake recharge test system in its long-term attack and defense practices, which is specially developed for digital asset management platforms. The system is designed to help them detect and evaluate their ability to prevent fake recharge attacks and optimize their defense mechanisms to ensure the security of user assets and the reliability of digital asset management platforms.
Badwhale is an exclusive and long-established commercial system of the SlowMist security team. It has been serving dozens of platforms for many years and has avoided the risk of fake recharges of an estimated billions of US dollars in assets.
Special feature:
1. Simulate fake recharge attacks: Badwhale can simulate various types of fake recharge attacks and automatically send fake recharge requests to the digital asset management platform being tested. This helps to assess the weaknesses of the digital asset management platform and discover potential vulnerabilities and security risks;
2. Diverse test scenarios: The system provides diverse test scenarios and attack modes, which can conduct comprehensive tests on the fake recharge defense of the digital asset management platform according to actual conditions;
3. High Scalability: Badwhale is designed as a highly scalable testing system that supports testing for different digital asset management platforms and blockchain platforms, and can flexibly adapt to the needs of different system architectures and technical environments.
Badwhale currently supports fake recharge tests for hundreds of public chains and tens of thousands of tokens, including:
Bitcoin Families (BTC/LTC/DOGE/QTUM...)
BitcoinCash
Ethereum Families
(ETH/BSC/HECO/RON/CFX-evm/FIL-evm/AVAX-evm/FTM-evm/RSK/GNO/MOVR-evm/GLMR-evm/KLAY/FSN/CELO/CANTO/EGLD/AURORA-evm/TLC/WEMIX/CORE/VS/WAN/KCCL/OKX...)
ERC20 Tokens (USDT...)
Ethereum L2 (ARB/OP/METIS...)
Polygon
Polygon Tokens
Cosmos Families (ATOM/LUNA/KAVA/IRIS/OSMO...)
EOS Families and EOS Tokens (EOS/WAX/XPR/FIO/TLOS...)
Ripple
Flow
Apartments
Solana
Solana SPL-Tokens
Confused
Polkadot Families (DOT/ASTR/PARA/MOVR/GLMR...)
Tron
Filecoin
Ton
Mina
Come on
Ordinals (ORDI...)
…
With the powerful functions of Badwhale, digital asset management platforms can conduct comprehensive false recharge defense tests to understand their performance in the face of false recharge attacks, optimize their defense mechanisms, and improve the security of user assets. The introduction of Badwhale will help digital asset management platforms strengthen security protection, improve their ability to fight false recharge attacks, and ensure the reliability of digital asset transactions and user trust.
Conclusion
By deeply studying the breakthrough methods of fake recharge attacks, we can better understand the importance of digital asset management platforms in protecting user assets and maintaining security. Only by strengthening security defense measures, continuously monitoring vulnerabilities and taking appropriate countermeasures can digital asset management platforms effectively respond to fake recharge attacks and other security threats and ensure the credibility and reliability of digital asset transactions.
Reference Links:
[1] https://mp.weixin.qq.com/s/CtAKLNe0MOKDyUFaod4_hw
[2] https://mp.weixin.qq.com/s/fKINfZLW65LYaD4qO-21nA
[3] https://mp.weixin.qq.com/s/3cMbE6p_4qCdVLa4FNA5-A
[4] https://mp.weixin.qq.com/s/OYi2JDbAoLEdg8VDouqbIg

