Compiled by: DoraFactory
This article will dive into the three main reasons Buterin points out that Ethereum could fail.
As we navigate the transformational maze of blockchain technology, it is crucial to examine the trajectory of Ethereum. According to co-founder Vitalik Buterin, Ethereum faces several major challenges that, if not properly addressed, could lead to its failure.
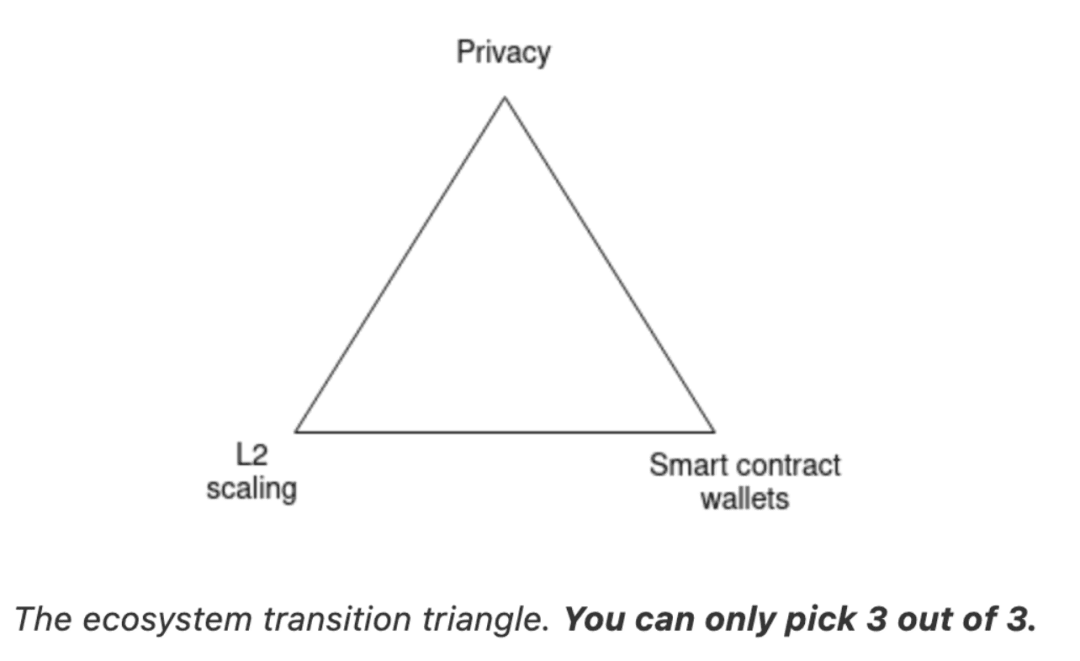
The first obstacle: the transition to Layer 2 expansion. As blockchain capabilities expand and demand grows, Ethereum needs to provide a scalable solution that maintains its decentralized philosophy. This is a balance issue - if this issue is not resolved, users may become frustrated by high transaction costs and turn to centralized workarounds, thereby weakening Ethereum's core selling point.
Secondly, Ethereum wallet security. Like an experienced fortress guard, Ethereum must ensure the safety of user assets. If users cannot trust Ethereum to protect their funds, they may flock to centralized exchanges, which will pose another potential threat to Ethereum.
Finally, privacy is crucial in today’s digital world. If Ethereum fails to provide strong privacy protection mechanisms, it may lose users, who may turn to centralized solutions that can provide at least some data protection.
1. What is Ethereum?
Ethereum is the second largest cryptocurrency by market capitalization, created by Vitalik Buterin. It rose to prominence in the industry by introducing smart contracts. Its significance is considered to exceed that of Bitcoin. Ethereum has built an entire ecosystem for decentralized applications (DApps) and has become the cornerstone of many other cryptocurrencies.
Ethereum represents an ecosystem of interconnected diverse communities and toolsets that empower individuals to transact and communicate without centralized control.
Ethereum, which debuted in 2015, expands on the groundbreaking concepts introduced by Bitcoin and has several unique features. Both platforms allow the use of digital currencies without the involvement of banks or payment service providers. However, Ethereum introduced programmability, allowing decentralized applications to be created and deployed on its platform.
While Bitcoin only allows simple value transfer messages, Ethereum takes this concept to a higher level: it allows not only message exchange, but also the creation of any general program or contract. This unlimited contract creation potential has led to tremendous innovation in the Ethereum network.
Unlike Bitcoin, which is primarily used as a payment network, Ethereum is a diversified market. It hosts a variety of services, including financial platforms, games, and social networks. These applications respect user privacy and resist censorship, cementing Ethereum's unique position in the digital world.
Ethereum relies on three fundamental elements to thrive: Layer 2 (L2) scaling, wallet security, and privacy. These three elements are intrinsically interrelated, each plays a vital role in Ethereum's function, and if one of them fails, the entire system is at risk of collapse. Please do not confuse this with the blockchain trilemma, which refers to the fact that no blockchain can optimize all three characteristics of decentralization, security, and scalability at the same time.
2. Three key elements of Ethereum
L2 Extension
It is essential for Ethereum to handle increased usage. Imagine a busy bar with only one bartender struggling to serve the growing crowd. In this case, L2 scaling is like hiring an extra bartender, which enables Ethereum to process transactions faster and avoid high costs per transaction. Without efficient L2 scaling, Ethereum transaction costs could be as high as $3.75 ($82.48 during the bull run), which would drive users to seek centralized solutions.
Wallet Security
Wallet security: Similar to the trust we place in the stability of a stool. Users must feel safe storing their funds and assets in the system. Without strong wallet security, users may turn to centralized exchanges.
privacy
Public visibility of all transactions is a sacrifice of privacy for many users, who may turn to centralized solutions that provide at least some data hiding. Without strong privacy protections, Ethereum may lose most of its users.
L2 Extension
L2 scaling involves moving much of the computational load from the main Ethereum chain (layer 1) to “sidechains,” or layer 2 networks. These sidechains can process transactions faster and at a lower cost, just like additional highways easing traffic congestion.
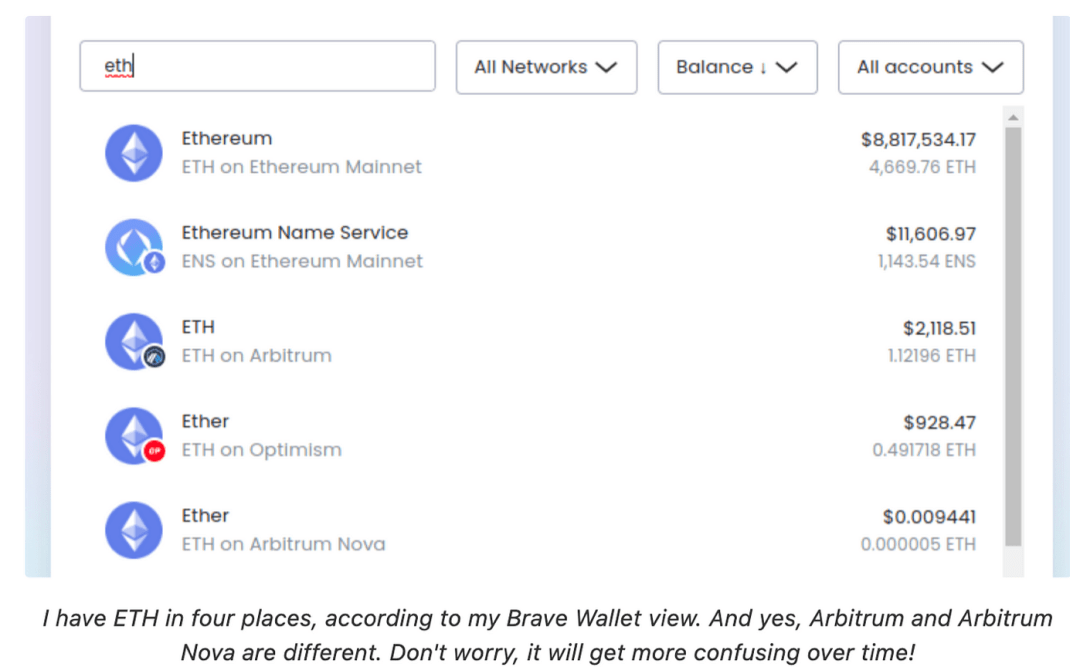
However, this transition is not without its challenges. It requires users to adapt to a new framework that exists on multiple L2s instead of just one address. This transition is similar to having multiple bank accounts at different institutions, each with different purposes, rather than relying on a single account.
There is already evidence of this trend, such as the use of Optimism in ExampleDAO, the implementation of ZkSync in stablecoin systems, and the application of Kakarot in other use cases. In each case, users must create an account on the respective L2, and the transition to L2 scaling is both challenging and critical. In order for Ethereum to continue to move towards its goal of becoming a global, open, and permissionless platform, migrating to L2 scaling is a hurdle that must be overcome.
4. Wallet Security
The second key point in the Ethereum ecosystem is wallet security. Wallet security is an important feature in the cryptocurrency space as the first line of defense against unauthorized access and potential theft of digital assets. Since digital wallets are a key component of the overall operation of the Ethereum blockchain, any security issues or vulnerabilities can cause serious losses and reduce trust in the platform.
A key challenge facing Ethereum is the potential risk of wallet security. Essentially, if Ethereum fails to provide users with strong and reliable wallet security, there is a high probability that users will move their funds to centralized exchanges. Centralized exchanges can provide advanced security measures such as two-factor authentication, cold storage, and insurance against potential theft, making them a more attractive option for storing digital assets.
There have been several instances in the past where Ethereum wallet security has been compromised, adversely affecting the ecosystem. For example, in 2017, Parity, an Ethereum-based company, suffered a major security breach, where attackers exploited a vulnerability in their multi-signature wallet, resulting in the loss of more than $30 million in Ether. This security breach not only resulted in a huge financial loss, but also shook trust in the security of Ethereum wallets.
These events highlight the importance of developing advanced digital wallet security features in the Ethereum ecosystem. Without proper wallet security, Ethereum risks losing users and their trust in the platform’s ability to securely protect digital assets. Therefore, in order for Ethereum to succeed and maintain its position in the cryptocurrency space, a high priority must be placed on enhancing wallet security and ensuring the safe storage of digital assets. This is an issue that needs to be given the highest priority in the Ethereum development roadmap.
V. Privacy
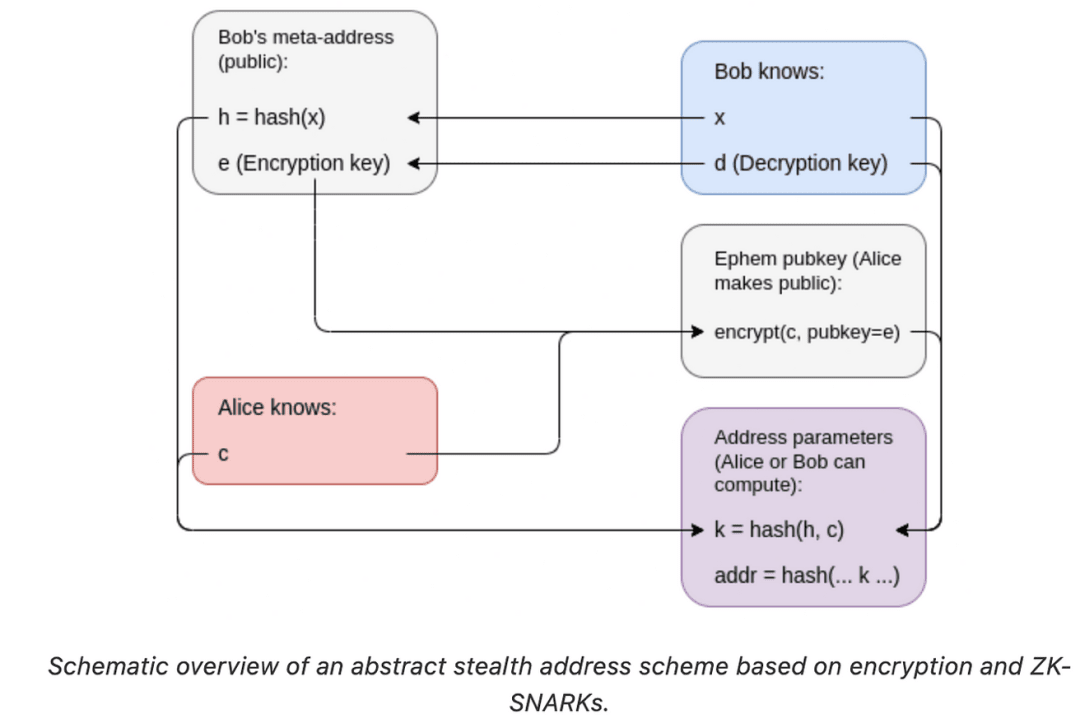
Privacy carries the heavy responsibility of protecting the confidentiality of transactions in the Ethereum network. However, as we continue to move forward in the digital maze, we must face the reality that the privacy in Ethereum operations is not as secure and reliable as we expect.
The essence of a blockchain is a public ledger that records every transaction and every interaction between users. In Ethereum, every transaction, every proof-of-presence protocol (POAP), can be seen by anyone. In principle, this provides transparency, an important factor of trust in any transaction. But at the same time, it also poses a major challenge to personal and transaction privacy. The public nature of these transactions reveals a lot of information about the participants and their transactions, leading to potential abuse.
If privacy measures are insufficient or fail, it will have far-reaching consequences for the entire Ethereum ecosystem.
Ethereum’s history is littered with privacy breaches that led to serious consequences. In particular, in 2016, the Decentralized Autonomous Organization (DAO) suffered a hacker attack worth 60 million ether. In another example, a privacy vulnerability in 2020 led to Ethereum’s “accidental hard fork,” in which a glitch split Ethereum into two independent blockchains.
In summary, Ethereum’s success and its ambition to become a mature technology stack heavily relies on how it handles the delicate balance between transparency and privacy. Failure to address this critical issue will destabilize Ethereum’s infrastructure and hinder its evolution towards a global, open, and permissionless experience.
VI. Transition solutions to meet these challenges
Adjusting to these major transitions will necessarily reshape the familiar relationship between Ethereum users and addresses, potentially creating a more complex landscape. Take the L2 scaling transition, for example. In this new world, users will no longer be restricted to a single address. Instead, they will have multiple accounts, spread across various L2 solutions, each with its own unique address. This change is far from cosmetic, and it introduces new complexities and potential confusion for users who are used to using just one address.
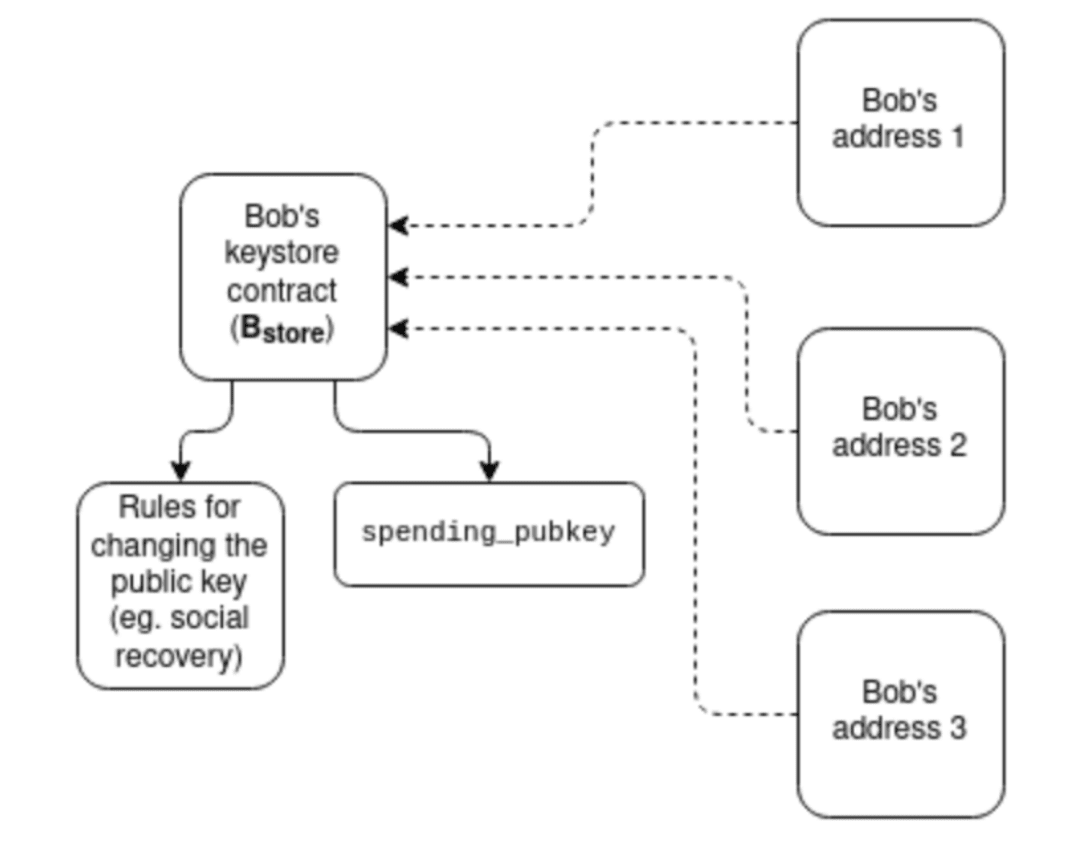
However, these challenges are not limited to the user perspective. These transitions require significant adjustments from developers as well. As Buterin points out, the existing mental model of “one user ≈ one address” is fading away, replaced by the need to coordinate interactions between different addresses, L2s, and applications. This transition requires deep and fundamental changes to how we interact with Ethereum, which may seem daunting at first. The difficulty lies in coordinating these efforts ecosystem-wide to ensure a smooth transition.
For example, the simple act of sending a payment now requires more information than just a 20-byte address. It also requires the recipient to provide their L2 solution along with the address, and the sender’s wallet automatically routes the funds to the designated L2 via a bridge system. This is just one example of many changes that need to happen in the Ethereum ecosystem.
7. Looking to the future
Can Ethereum withstand the pressure?
Despite these significant challenges, Ethereum is not sitting on the sidelines. To combat scalability issues, developers are turning to Rollups (Layer 2 solutions), which are designed to process transactions off-chain and then bundle them together and add them to the main Ethereum chain. Doing so can increase throughput and reduce costs while maintaining the security guarantees of the main chain.
In terms of wallet security, efforts are underway to transition users to smart contract wallets. These wallets offer more secure storage solutions that leverage the inherent security mechanisms of Ethereum itself.
Privacy issues are being addressed through various innovative technologies, such as zero-knowledge proofs, which allow users to prove ownership without revealing any significant information.
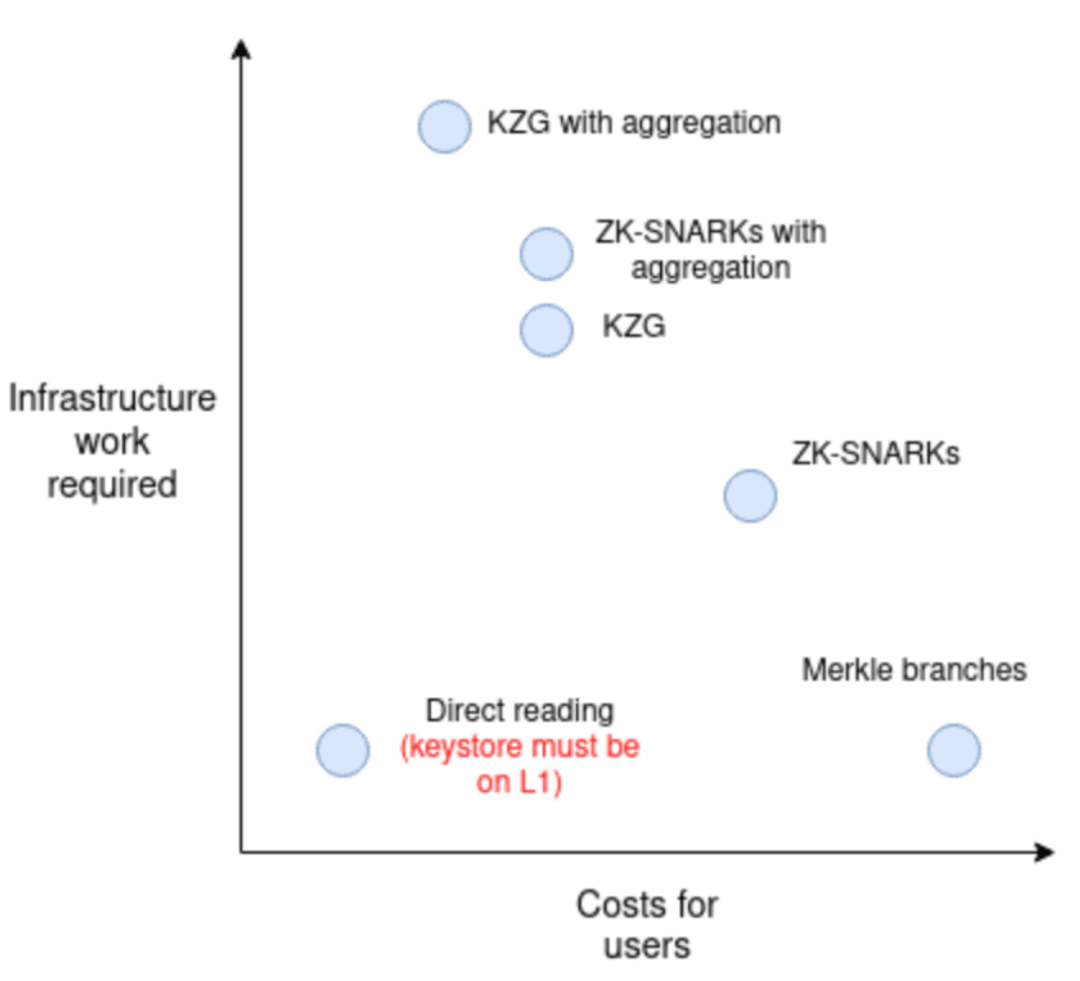
Vitalik's solution to these challenges is based on an architecture that separates verification logic from asset holding. Through the keystore contract, the verification logic can be placed in one location, corresponding to different addresses on L2, greatly reducing the complexity of handling multiple addresses and related security risks.
