Don’t ask for help when it comes to network security! Be careful before signing your MetaMask wallet!
MetaMask is a very famous and most widely used EVM (Ethereum Virtual Machine) encrypted digital wallet. I believe that anyone familiar with the encrypted digital field has used the MetaMask wallet to some extent. However, as more and more people enter the encrypted digital field, the number of digital fraud cases derived from it is also increasing. There are even more cases of digital assets being stolen due to unfamiliarity with the operation mode of blockchain.

A friend once had such a situation. He clearly did not make any transactions, but found that the digital assets in his wallet were transferred for no reason. He was sure that the mnemonic phrase was not leaked to others, but he had used the wallet to log in to different accounts many times. website, participate in different dApp interactions, etc. Therefore, it is very likely that the problem lies in the signature.
This time we will take MetaMask as an example to talk about three signature issues on the blockchain.
The so-called signature is actually an identity authentication process. Just like when you go to a bank to withdraw money, in addition to receiving your operation instructions, the bank must also conduct identity authentication to ensure that you are the real account owner. Bank identity authentication can be carried out by password, signature, seal, etc.
Blockchain signature
The same is true for transactions on the blockchain. When you conduct a transaction, in addition to instructing the blockchain "what to do", you also need to perform identity authentication to ensure that you are the real account owner before you can perform the corresponding operation. This identity authentication is what we call "signature".
The specific method of signing is to use your private key (Private Key) saved in a blockchain wallet (such as MetaMask) to digitally sign the instructions you issued through an encryption algorithm. This signature can be done with Your address public key (Public Key) is compared to verify that it is indeed the corresponding instruction issued by you, and the authentication process is completed. In addition, the action of "signing" does not require winding. It can also be done without internet connection.
Therefore, as long as you have a valid transaction signature and match the corresponding transaction instructions (such as transfer), you can complete a transaction normally.
At this point, I believe smart readers can see the mystery. The transaction signature is the top priority in the entire process. In other words, a fraudster can forge a transaction and defraud your transaction signature. Then the fraudster can use this signature to execute the forged transaction, causing you to lose assets under inexplicable circumstances. The leakage of transaction signatures is one of the culprits of the theft of many digital assets.
Personal Sign
Common Web3 login signing
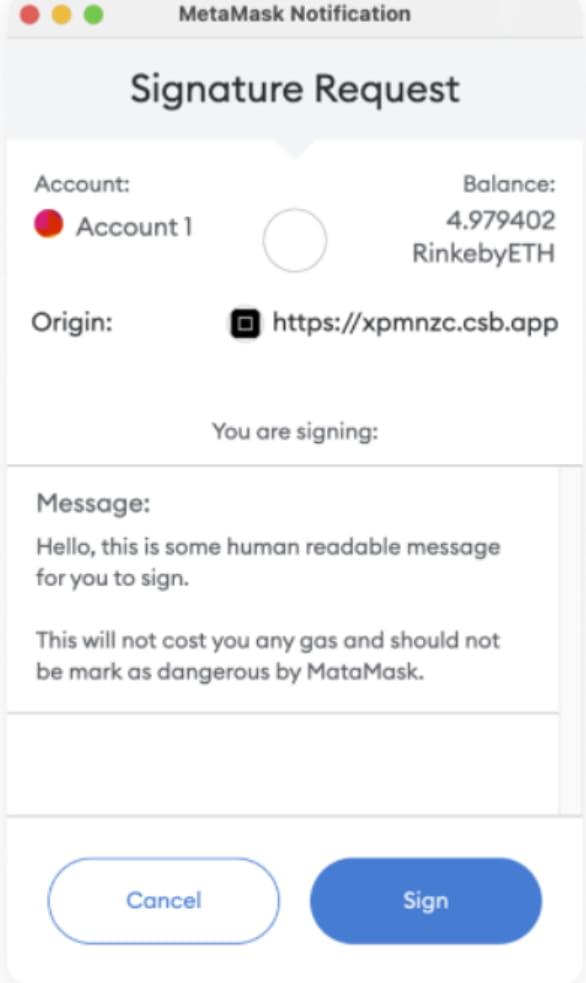
Personal Sign can be used to sign a piece of UTF-8 encoded text. Using this method, MetaMask will clearly display the signed content. This method is commonly used for website logins.
The OpenSea login we mentioned above uses the Personal Sign method.
Eth_Sign
Users need to be more alert to sign
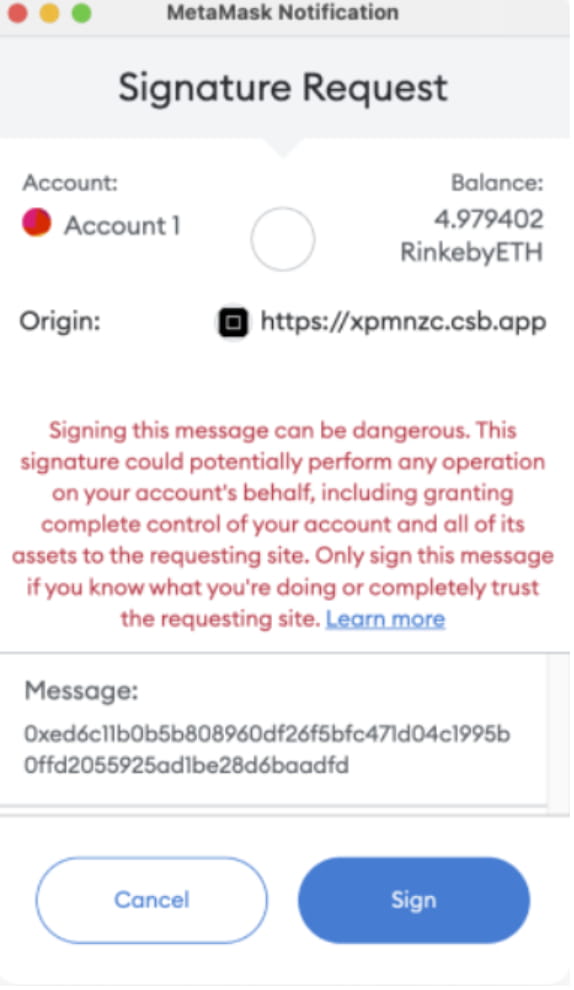
ethsign is a signature method provided very early by MetaMask. This method requires passing in a 32-byte hash number (Hash) for signature, and the hash number can be obtained from any content. Therefore, with this meaningless hash number alone, the signature The author will have no idea what content he is signing. This content may be a transaction, an authorization, a website login request, or anything else. Therefore, there is a very high risk. Now MetaMask has begun to sign such signatures. Request a red warning to pop up to warn users to avoid falling into a scam.
Dang, ring the bell. Ethsign is a very dangerous signature method, and it is also the signature method used by many scams. The OpenSea login we mentioned above uses the Personal Sign method.
EIP712 Sign
A more advanced and secure method of signing transactions
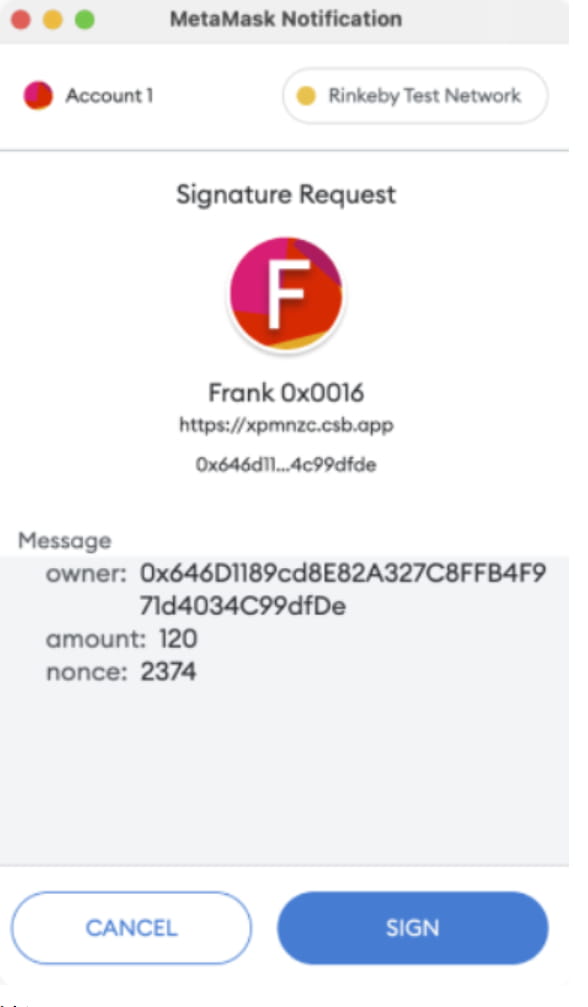
EIP712 Sign is a more secure signature standard. This standard specifies the structure of signature data and also adds scope restrictions on data, such as domain, verification contract address, etc.
ERC712 signatures are often used in contract execution such as metatransactions. For example, EIP712 signature requests will appear during OpenSea NFT listing, price reduction and other processes.
The advantage of this standard is that signers can clearly see what they are signing, which greatly reduces the risk of being phished. However, this does not mean that this kind of signature is absolutely safe. When signing, you must clearly see what you are signing.
Conclusion
To sum up, you can never think that there is no risk if the signature is not on the chain. On the contrary, blockchain signatures can actually be considered omnipotent, especially signatures that pop up using ethsign. Both development teams and individuals must be extra careful.
In addition to the security of the metamask interaction itself, other security recommendations include:
1. The private key and mnemonic phrase cannot be given out under any circumstances, and do not use the clipboard to copy, nor can you take photos, screenshots, or store them in a network disk. Remember the private key or mnemonic phrase is everything in your wallet
2. Separate hot and cold wallets. All transactions must be done in hot wallets. Cold wallets only perform transfer-in and transfer-out operations. If you want to sell an NFT in a cold wallet, you would rather spend a little gas to transfer it out to the hot wallet first.
3. When going to mint, or when trying some dApps, it is best to use a small wallet
4. It is best to store large amounts of assets in exchanges or hardware wallets. Mnemonic phrases for hardware wallets can only be written by hand and cannot be stored on the Internet.
I hope everyone will be happy in the crypto world and protect their wallets. Wallets are the key to our survival in the web3 world. If the key is lost or stolen, the wallet no longer belongs to you. If this happens, immediately remove the contents of the wallet. assets, wallets are deprecated.

