Author: GoPlus Research Institute
Table of contents
Editor's Note
MEV Evolution History: From PoW to PoS
MEV principle
Common MEV strategies
MEV Advantages and Disadvantages Analysis
How to avoid losing money
How to mitigate the impact of MEV
Summarize
Editor's Note
Imagine that you are ordering food in a crowded restaurant, and the waiter delivers the orders to the chef in the order in which the customers place their orders. At this time, a diner expresses his willingness to pay extra just to have his order processed first and served as soon as possible. This scenario is not only common in restaurants, but also has a parallel example in the world of blockchain - this is a concept called Maximum Extractable Value (MEV).
In this digital "dark forest", miners and validators are like the waiter, who can obtain value when processing blockchain transactions. When users submit transactions to the blockchain, these transaction information is not immediately recorded in the block, but temporarily placed in a public pending transaction pool, just like a customer's order is placed in the restaurant's kitchen waiting to be cooked. However, in this pool, anyone can see the transaction information, just like other diners can see the chef's busy situation.
In this environment, the concept of MEV came into being. Just like the diner in the restaurant who is willing to pay extra for priority service, miners or validators can extract the maximum value from block production beyond the standard block reward and gas fee by including, excluding or reordering transactions. Simply put, MEV is the quantification of the value of priority transaction rights.
This situation reflects a larger problem: in this blockchain world similar to the "dark forest", there is an inherent tension between the openness of information and the fairness of transactions. With a high degree of openness and transparency, the fairness and equity of transactions may be undermined. In the face of such a blockchain dark forest, what measures and attitudes should we take?
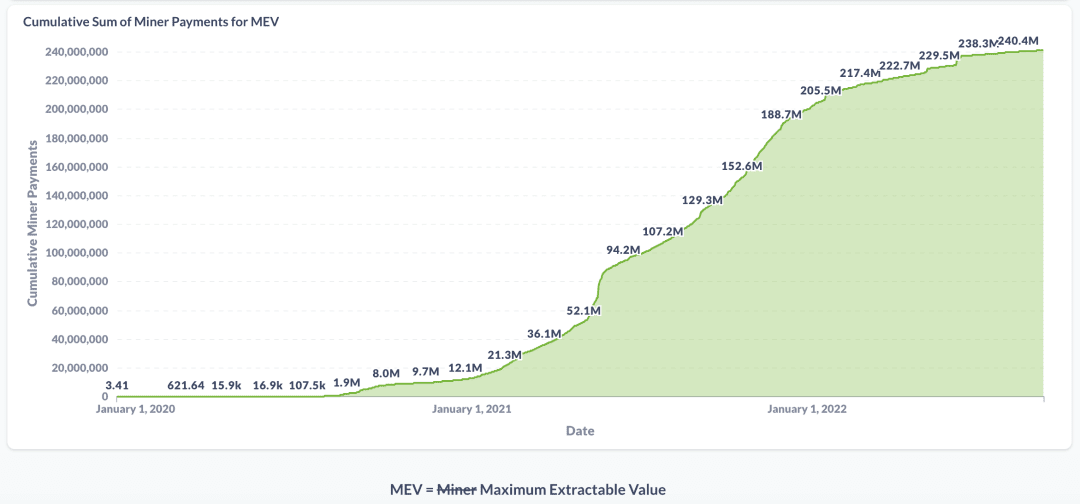
Source: MEV- Explore
MEV Evolution History: From PoW to PoS
MEV is the concept of value captured by miners or validators during the blockchain transaction processing phase. Previously also known as miner extractable value, MEV refers to the maximum value extracted from block production that exceeds the standard block reward and gas fees by including, excluding, and reordering transactions in blocks to obtain as much profit as possible.
In 2019, Phil Daian, Tyler Kell and others first proposed the concept of MEV in their paper "Flash Boys 2.0: Frontrunning, Transaction Reordering, and Consensus Instability in Decentralized Exchanges". This paper describes how miners extract additional value from the transaction sorting process by reordering transactions to maximize profits or inserting new transactions of front-running users. The term "maximum extractable value" was first proposed by Dan Robinson in his blog post "MEV is the new DeFi primitive".
The concept of MEV was originally associated with the Ethereum network, which uses the proof-of-work (PoW) consensus mechanism. Under this mechanism, when a user submits a transaction to the blockchain, the transaction information is not immediately recorded in a block, but is temporarily placed in a public pool of pending transactions that anyone can see. In August 2020, Dan Robinson and Georgios Konstantopoulos likened Ethereum's memory pool to a "dark forest" that can be exploited if others see the order of people's transactions. It was at this time that the concept of MEV gained widespread attention.
In September 2022, Ethereum completed its transformation from proof-of-work (PoW) consensus to proof-of-stake (PoS) consensus. Based on this transformation, block producers are no longer just miners, but also include validators, sorters, etc. In addition, some strategy robots and other network participants (also known as searchers) that focus on DeFi transactions have also joined the ranks of extracting MEV. Therefore, MEV is not an exclusive privilege of block producers, but a value that can be obtained by any participant who can influence the execution of transactions. The concept of MEV is evolving and expanding with the development of blockchain technology and DeFi applications. Some researchers and practitioners have begun to explore issues such as how to classify, measure, allocate, and manage MEV, and have begun to study how to mitigate the negative impact of MEV on blockchain security and fairness.
However, we must be clear that no matter who chooses which transactions to add and in what order to add them, the purpose is undoubtedly to maximize profits. Therefore, in the context of Proof of Stake (PoS), more and more participants are rushing to obtain MEV, and everyone’s goal is unusually consistent - to fill their own pockets.
MEV principle
MEV stems from a property of blockchain transactions: transactions are not executed atomically, but in batches called "blocks." The order of transactions within a block can affect the results and profitability of certain transactions, especially those related to decentralized finance (DeFi) applications.
For example, let’s say Alice wants to buy 10 ETH with USDC on a decentralized exchange (DEX) like Uniswap. She submits a transaction with a certain amount of USDC and the minimum amount of ETH she expects to receive. However, before her transaction is confirmed and recorded in a block, Bob sees her transaction in the public pool of pending transactions (also known as the mempool) and decides to steal her transaction. He submits a transaction with a higher gas price than Alice’s, offering to buy 10 ETH at a slightly higher price than Alice. In this way, he ensures that his transaction will be recorded in the block before Alice’s transaction, thus getting a better exchange rate than Alice. Bob then sells the 10 ETH he just bought with USDC on another DEX, profiting from the price difference. This profit is Bob’s MEV, and it comes at the cost of Alice receiving less ETH than she expected.
In this example, Bob is a "seeker", an independent network participant who runs complex algorithms to find profitable MEV opportunities in blockchain data and submits transactions to exploit these opportunities. Seekers can be individuals, robots, hedge funds, or other entities. Seekers compete with each other to grab MEV and are willing to pay high gas fees to increase the probability of their transactions being recorded in the block.
However, it is not only the seekers who can extract MEV. Block producers, such as miners in Proof of Work (PoW) or validators in Proof of Stake (PoS), have the final say on which transactions are included in a block and in what order. Therefore, they can extract MEV themselves or in collaboration with seekers. For example, a miner can directly front-run Alice's transaction by inserting his own transaction in the block he generates, or he can accept a bribe from Bob to put Bob's transaction before Alice's transaction. Alternatively, miners can outsource the task of finding MEV opportunities to third-party services, such as Flashbots, which provide a transparent and permissionless platform for seekers and miners to negotiate and execute MEV extraction strategies.
Role Function Driver Seekers Find and exploit MEV opportunities by submitting transactions to the network Capture MEV and profit from them Block Producers Decide which transactions to include in a block and in what order Maximize revenue through block rewards, gas fees, and MEV Flashbots Provide a platform for seekers and miners to coordinate MEV extraction Improve the efficiency and fairness of MEV extraction and reduce its negative impact on the network
Main participants of MEV
Common MEV strategies
MEV is an important and complex issue that affects the security and fairness of blockchain and decentralized finance (DeFi) applications. On the one hand, MEV provides an additional source of income for block producers, which helps protect the network and motivate people. On the other hand, MEV can also cause some problems, such as network congestion, rising gas prices, unfair phenomena, and unstable consensus. Understanding MEV is crucial to designing and improving blockchain protocols and various applications.
MEV includes various factors such as transaction fees, flash loan profits, transaction order manipulation, etc. It has several types according to different extraction methods and purposes. Different types of MEV also have different effects on the blockchain network. Let's take a look at some common MEV types.
1. Sandwich
A sandwich attack involves "sandwiching" the victim's transaction between two transactions initiated by the searcher/attacker, whose reordering of transactions results in hidden losses for the victim user and possible benefits for the attacker.
A sandwich attack is a classic predatory trading strategy where a trader wraps the victim's trade between two malicious trades, one before the victim's trade and one after the victim's trade. In this attack, the malicious attacker first scans pending transactions in the memory pool and finds a user (i.e., the victim) attempting to trade asset X for asset Y. The attacker then buys asset Y at a low price. This trade may precede the victim's trade. If this trade is completed before the victim's trade is completed, the price of asset Y will increase accordingly. When the victim's trade is executed, he/she will receive less asset Y than he/she expected to receive due to the increase in the price of asset Y. Finally, the attacker "sandwiches" the victim's trade by selling asset Y at a higher price than he/she bought it for, thereby profiting on the manipulated price. This attack sequence allows the attacker to profit by front-running and tailing traders, creating artificial price increases.
It is worth mentioning that in the blockchain, miners will sort the transactions in the memory pool according to the gas price, and then select transactions in order of gas price from high to low when creating blocks. Therefore, as long as the attacker sets the gas price of the leading transaction slightly higher than the gas price of the victim transaction, and sets the gas price of the trailing transaction lower than the gas price of the victim transaction, a sandwich attack can be implemented.
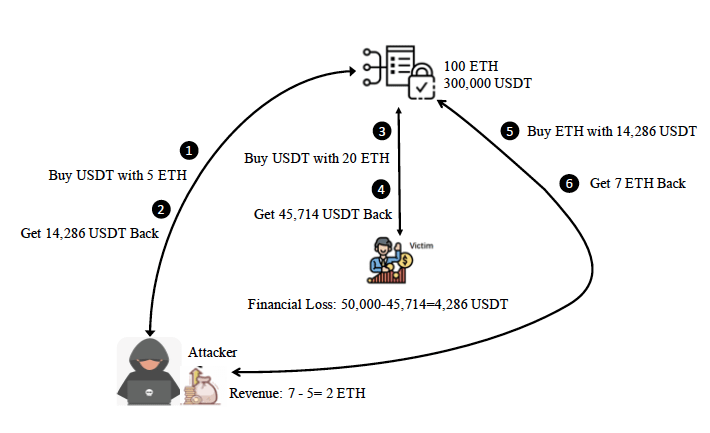
Source: Impact and User Perception of Sandwich Attacks in the DeFi
For example, as shown in the figure, the attacker front-runs the victim's trade with a buy USDT order and tails the victim's trade with a sell order. Specifically, the victim's trade attempts to buy USDT on the market with 20 ETH. If there is no attacker, the trader will get 500,000 USDT. However, the attacker uses 5 ETH to exchange 14,286 USDT in advance in steps ①-② and sandwiches the victim's trade in it. Because the reserves in the liquidity pool change after each transaction. The original state of ETH/USDT is 1/3,000. After the attacker's first transaction, the state of ETH/USDT becomes 1/2,721. Therefore, in steps ③-④, the victim can only exchange 20 ETH for 45,714 USDT, losing 4,286 USDT. After the victim's transaction, the state of ETH/USDT in the liquidity pool becomes 1/1,920. Finally, the attacker uses all the 14,286 USDT held in steps ⑤-⑥ to exchange for 7 ETH, making a profit of 2 ETH.
2. Arbitrage
Arbitrage is the practice of buying and selling the same asset simultaneously in two or more different markets to take advantage of price differences or market imbalances to make a profit. Arbitrageurs buy and sell the same asset in two or more markets to take advantage of price differences. For example, if a stock is priced lower in one market than in another, an arbitrageur can buy the stock in the market where the price is lower and sell it in the market where the price is higher to make a profit.
In DeFi, arbitrage is also a common strategy used by arbitrageurs, who make profits by quickly buying and selling assets on different DeFi platforms, exchanges, or markets. When the price of an asset is inconsistent between different exchanges, there is an immediate arbitrage opportunity. If the price of a token on one exchange is lower than another, arbitrageurs can buy the token on the exchange with the lower price and then sell it on the exchange with the higher price to make a profit.
The figure below is a simple illustration of arbitrage.
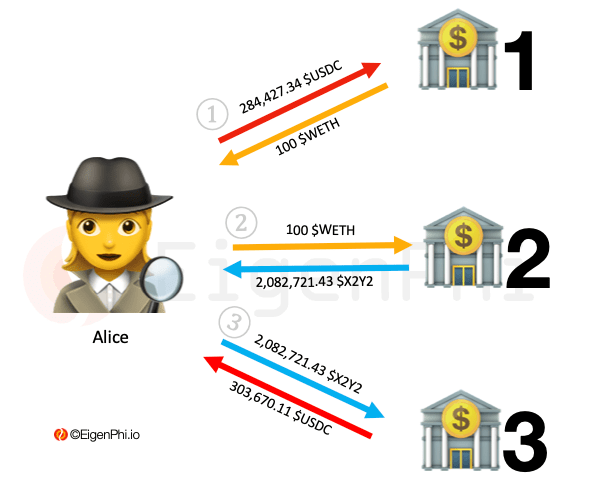
Source: Arbitrage Involving 3 Tokens Among 3 Trading Venues
Alice sells 284,427.34 $USDC and buys 100 $WETH at an exchange rate of 1 $WETH to 2,844.27 $USDC in a liquidity pool called LP1 on Uniswap.
Alice sells 100 $WETH and buys 2,082,721.43 $X2Y2 at the exchange rate of 1 $WETH to 20,827.21 $X2Y2 in another liquidity pool called LP2 on Uniswap.
In another liquidity pool called LP3, Alice exchanged 2,082,721.43 $X2Y2 for 303,670.11 $USDC.
Alice's income from this arbitrage is 19,242.77 $USDC. The cost is the gas fee of three transactions, assuming it is 0.05 $WETH, which is equivalent to the price of 150 US dollars at the time. And assume that the exchange rate between USDC and USD is 1:1. Finally, Alice's profit is 19,092.77 US dollars.
3. Liquidation
Liquidation is a process that occurs when the value of a borrower's collateral is insufficient to cover the value of their loan/debt. Liquidation can occur in the event of a negative movement in the price of the debt collateral (i.e., below the liquidation threshold). In a permissionless blockchain, users are allowed to borrow using deposited digital assets as collateral. If the market moves and the value of the collateral drops below a certain price, the position is liquidated. The smart contract involved usually pays a reward or fee for the transaction that triggers the liquidation.
This creates a MEV opportunity where any searcher or block producer running a bot looking for such transactions can insert their own clearing transaction into a block ahead of anyone else, thereby extracting reward value.
The following diagram is a simplified illustration of the liquidation process.
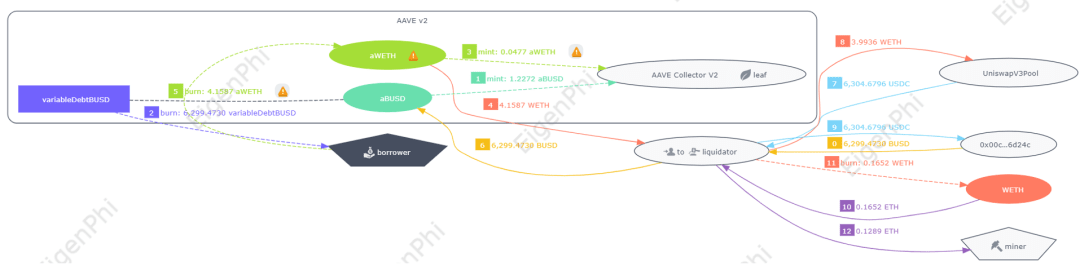
Source: Liquidation transaction with Aave V2 involved
This transaction involves Aave V2, and we can see that all transfers within the Aave protocol are grouped together.
In order to obtain the guarantee, the liquidator must repay the debt of the borrower. In the sixth step, the liquidator repaid the debt of 6299 BUSD for the borrower.
In the second step, we can see that 6299 virtual debt BUSD has been destroyed, which you can regard as the borrower’s debt proof (IOU) in Aave.
In return, the liquidator received the borrower's guarantee, which is 4.1587 WETH. Correspondingly, the same amount of aWETH, or the guarantee certificate, was destroyed from the borrower in step 5.
This process is a typical liquidation strategy for Aave (and many other DeFi protocols) to ensure the security and stability of the protocol. When the value of the borrower's collateral falls to the point where it can no longer cover their debts, the liquidator will step in, repay the borrower's debt, and collect the borrower's collateral as compensation.
In this case, the application of MEV is to enable liquidators to operate at the best price on the public chain and obtain the maximum benefit. Liquidators can take advantage of this debt liquidation opportunity by optimizing their trading strategies without worrying too much about transaction fees or slippage. At the same time, since the debt has been liquidated, the security and stability of the protocol are maintained, and the borrower's remaining collateral may be released back to their wallet.
4. Front-running
Front-running refers to the act of placing a transaction into a transaction queue after knowing future transaction information. On the blockchain, front-running usually occurs after miners have information about pending transactions. Miners conduct transactions that they believe will bring profits based on these pending transactions. For example, a robot can quote a higher gas price than the pending transaction to speed up its processing, and front-running will occur at this time.
Searchers and block producers can use their ability to queue transactions in blocks to rush major buy orders that are still waiting in the transaction pool. MEV occurs when a similar buy order is placed before a large buy order to obtain a more favorable price.
5. Back-running
A tailing transaction occurs when the sender wants their transaction to be placed immediately behind an unconfirmed target transaction. For example, a tailing bot that wants to tail a newly released token would monitor Ethereum's mempool for newly created trading pairs on Uniswap. When it finds a new trading pair, the bot initiates a buy transaction immediately after the initial liquidity. The bot immediately buys as many tokens as possible (not all, because it also needs to leave room for others to buy the tokens). The bot then waits for other traders to buy the tokens from Uniswap, causing the price to rise, and then sells the tokens at a higher price. The key to this strategy is to be the first to buy the token, but you can only do this after the token is released.
6. Time-bandit attack
The main goal of a time bandit attack is to obtain higher rewards than normal block rewards by reorganizing past blocks. This strategy is usually applicable when the arbitrage opportunities or other types of MEV in a block are much larger than the normal block reward.
In a blockchain network, generally speaking, once a block is mined and added to the blockchain, it is considered immutable. However, in some cases, if a miner has enough hash power, he can choose to re-mine some blocks that have already been mined to capture the MEV in these blocks. This is the basic concept of a time bandit attack.
For example, suppose there are two miners, Miner A and Miner B. Miner A has mined three blocks, and there is an arbitrage opportunity worth $10,000 in the first block. The reward for each block is only $100. In this case, Miner B can choose to re-mine the three blocks and modify the original transactions to capture this arbitrage opportunity worth $10,000.
The time bandit attack is a rather complex and risky MEV strategy that requires miners to have a lot of hash power and be able to accurately predict and find blocks that contain a lot of MEV. However, if successfully executed, the time bandit attack may bring benefits far beyond the block reward. For some miners who are capable and willing to take risks, this may be a strategy worth trying.
7. Snipping bots
Sniper bots are automated programs running on Ethereum and other EVM-compatible blockchain networks that earn MEV by looking for potential profit opportunities in the unconfirmed transaction pool (mempool). These bots specifically monitor transactions that may bring large profits, such as flash loan arbitrage, new token issuance, limit orders, etc.
The working principle of sniper robots is based on the public and delayed characteristics of blockchain. When they find a profitable transaction, they will send a transaction with a higher fee as quickly as possible, hoping to be packaged into the block before or after the target transaction, thereby achieving the so-called "preemptive attack" or "sandwich attack". If the attack is successful, the sniper robot can get a part of the profit from the target transaction.
The construction of sniper bots usually requires writing smart contracts and scripts in programming languages such as Python and JavaScript, or leveraging open source projects or platforms such as Flashbots, Pancake Sniper Bot, etc. It is worth noting that while the potential returns of sniper bots may be high, it is also a high-risk strategy. If the robot's algorithm or execution is wrong, it may result in transaction failure or loss. Sniper bots also have a certain impact on the security and fairness of the blockchain. Because sniper bots can increase the priority of transactions by bidding higher fees, this may cause ordinary users to pay higher fees to get their transactions packaged.
8. Gas golfing
The purpose of Gas Golf is to conduct efficient transactions and reduce gas fees as much as possible. Gas Golf increases the competitive advantage of seekers (independent participants who look for and execute profitable MEV opportunities) because it allows them to set higher Gas prices while keeping the total Gas fee constant (Gas fee = Gas price * Gas used). In this way, their transactions are more likely to be included in the block by validators (nodes responsible for packaging and sorting transactions), thereby earning MEV income.
For example, let's say there is a DEX arbitrage MEV opportunity that could allow a seeker to make $100 in profit, but there are many other seekers who want to execute the same trade. To ensure that his trade is processed first, the seeker must bid the highest Gas price. If the seeker can reduce the Gas required for his trade from 1000 to 500 through Gas Golf, he can increase his Gas price from $0.1 to $0.2 without affecting his total Gas fee (which is still $100). This way, he has a greater chance of winning this MEV opportunity, rather than being outbid by other seekers who bid lower.
Gas Golf is a way to optimize transaction efficiency and save costs, but it can also bring some risks and challenges. For example, if searchers sacrifice transaction security or reliability in order to reduce Gas consumption, they may face problems such as replay attacks or transaction failures. Gas Golf may also increase network congestion and Gas price volatility because searchers will compete to bid higher Gas prices in order to protect limited block space.
MEV Advantages and Disadvantages Analysis
MEV is closely related to the security, fairness, and efficiency of blockchain. MEV can cause various problems, including attacks on traders, increased transaction fees on the network, network congestion, and may also cause security vulnerabilities. In this section, we will explore the pros and cons of MEV in depth.
Network congestion
In order to increase the possibility of transactions being packaged, searchers who specialize in finding and conducting transactions such as arbitrage or liquidation will compete to submit high Gas fees. They work with validators or miners to share MEV income. This interest incentive also means that searchers are willing to pay higher Gas fees than regular users to ensure that their transactions are executed before other transactions. Therefore, the public memory pool may become congested due to high Gas fee transactions of searchers, resulting in longer waiting times or higher fees for ordinary users. This may reduce the network's throughput and increase transaction delays.
Poor user experience
First of all, the most significant problem brought by MEV is that it exposes users to malicious MEV attacks, such as sandwich and front-running transactions, which in turn affects the execution results and costs of user transactions. For example, seekers can preempt users’ bids for NFTs or domain names on the Ethereum Name Service (ENS), taking items from users, forcing users to pay more for their transactions or lose the opportunity, degrading the user experience.
Secondly, MEV also increases the gas fee of Ethereum transactions. Seekers are willing to pay higher gas fees to force transactions first, so ordinary users may need to compete with seekers for block space, resulting in higher gas fees and increasingly unpredictable transactions.
Finally, MEV creates uncertainty for users and undermines their trust in the blockchain. When users submit transactions on blockchain networks such as Ethereum, due to the existence of MEV, they may not be able to ensure that their transactions can be executed as expected, such as forced transactions, increased gas fees, or transactions being canceled. In addition, MEV creates incentives so that miners or validators may try to reorganize the blockchain to obtain more benefits. Reorganizing the blockchain may change the history of transactions that have been completed, which will directly undermine users' trust in the immutability of the blockchain. There are also cases where miners may choose to censor certain transactions, that is, they may choose not to include certain transactions in the new block because they have found another more profitable way to trade, or they have been bribed by attackers and decided to block specific transactions. This situation may also make users doubt whether their transactions can be processed fairly.
Although MEV has many disadvantages, it is not without merits. It has the following benefits:
Keep the network active. MEV can provide validators or miners with an additional source of income, in addition to standard block rewards and gas fees. As a result, validators or miners have more motivation to compete for block production rights and keep the network running well. MEV can also attract more searchers to join the network, specifically looking for and conducting lucrative transactions, helping validators or miners optimize block construction and share MEV revenue.
Promote market efficiency. MEV can eliminate some arbitrage opportunities and price differences in the market. For example, on decentralized exchanges (DEXs), the same asset may have different prices due to different liquidity pools and trading volumes. This provides a great opportunity for arbitrageurs, who can earn the difference by buying at a low price on one DEX and selling at a high price on another DEX. This arbitrage behavior can make prices in the market more consistent and reasonable, thereby improving market efficiency. In addition, MEV can also help liquidate some over-leveraged or high-risk lending protocols and reduce systemic risks.
Provide additional benefits. MEV has become a new source of income for groups such as searchers, validators or miners and traders. Searchers run complex algorithms to see which transactions can bring rich returns, and then cooperate with validators or miners to share the MEV revenue. Validators or miners extract MEV by packaging transactions and charge high gas fees from searchers. Traders use specific services or protocols to optimize their transaction order or privacy and obtain MEV revenue. For example, Flashbots launched the MEV-Share protocol, which aims to distribute part of the MEV revenue to users of the Ethereum ecosystem, thereby achieving public and fair distribution of revenue.
How to avoid losing money
Let’s look at an example of a MEV arbitrage bot: jaredfromsubway.eth. Just like hoarding a whole sandwich, this bot spent over $7 million (3720 ETH) in gas fees to run its MEV operations in just two months. A Twitter user recently discovered that jaredfromsubway.eth earned a whopping 387 ETH (about $696,000) in just a few days!
jaredfromsubway.eth is the culprit that caused the Ethereum mainnet gas price to rise significantly and confused the mainnet users. This MEV robot is keen on meme coin transactions (such as PEPE, WOJAK, etc.), and has initiated more than 600,000 transactions. Etherscan data shows that jaredfromsubway.eth has been trading at a high frequency in seconds, with an interval of about 12 seconds between each round of transactions, which means that its operations cover almost every block. It is estimated that although the single profit amount brought by each transaction is not large, the high frequency of transactions makes this robot extremely profitable-excluding gas costs, jaredfromsubway.eth can make a huge profit of 466,000 US dollars in just one day.
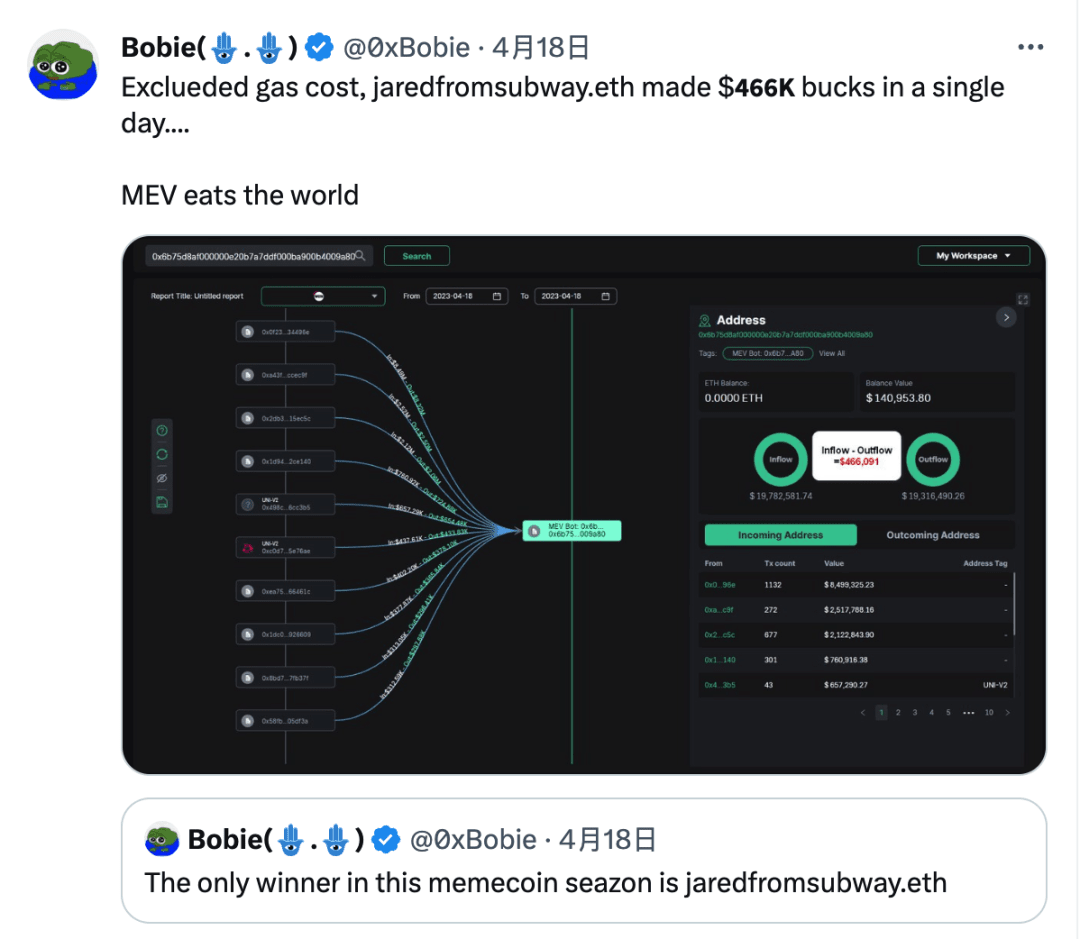
People were talking about this crazy move. Some people thought that the address was making reasonable use of the network rules and accelerating the deflation of ETH; some people were neutral and believed that the impact was only that their main network operations were not as convenient as before; some people were firmly opposed because their transactions that should have been profitable were intercepted by jaredfromsubway.eth. In any case, the most important thing at the moment is to hold on to your wallet.
Of course no one wants to pay more money when trading. Here we can use Flashbots RPC to protect ourselves from MEV robots. Interested readers can read this: https://youtu.be/x6aqTtY8OqM
By using Flashbots Protect RPC, you can enjoy the following benefits:
Front-running prevention: Your transaction will be invisible to those greedy sandwich bots lurking in the public mempool.
Ensure that the transaction will not fail: The transaction will only be effective if it does not cause the failure of any step, thus eliminating the fees incurred by failed transactions.
Privacy: Flashbots Protect RPC does not track or store any user information (such as IP, location, etc.).
In addition to using Flashbots Protect RPC, there are a few other strategies that can help protect transactions:
When exchanging assets, keep the maximum slippage low to minimize the impact of MEV.
Lower your expected gas price so that the MEV robot pays less attention to your transaction.
Use optimized decentralized exchanges (DEXs) like CowSwap, which have built-in mechanisms to reduce MEV risk.
In addition to the above methods, there are several ways to protect yourself from MEV.
1. Hiding transactions
In blockchain networks such as Ethereum, all transactions are visible in a public memory pool before they are packaged into blocks and mined by miners. MEV types that exploit strategies such as front-running trading robots can profit by viewing these unpackaged transactions. One solution is to send transactions to a private memory pool, such as Flashbots, which can only be seen by miners (block proposers or builders) who are preparing to package these transactions. However, this method can only be used to prevent sandwich attacks and front-running transactions.
2. Introducing off-chain computing to find the optimal solution
Since the smart contract on the chain can only see limited data, and the on-chain computation is expensive, we cannot expect it to always find the best market transaction price. However, if off-chain computation is introduced, it becomes possible to find a solution close to the optimal one. The off-chain software can access all markets in real time, find the best transaction price for any asset at any given time, and the best transaction path. In this way, we can construct better transactions, thereby reducing the possibility of users being profited by others through MEV (maximum extractable value).
3. Auction transactions
You can make the right to submit transactions public and allow other people or robots to bid and extract MEV. However, doing so may bring risks and uncertainties, because you need to pay both the relay (the entity that submits the transaction) and the robot that works for the relay. Not only that, users also need to prevent information abuse. Doing so may make your smart contract too dependent on the relay, and once the relay fails, the smart contract may not work properly.
4. Use your own robot
By using your own bot, you can resist other bots and prevent them from profiting from MEV. To do this, you may need to design and build a bot that can outcompete other bots, and the specific implementation method depends on your protocol and the blockchain you are on.
How to mitigate the impact of MEV
There is a lot of discussion about the MEV problem. Some people try to solve this problem by eliminating MEV from the blockchain. They try to modify the blockchain's protocol or mechanism to reduce or eliminate the possibility of miners and validators extracting additional profits. Others believe that MEV cannot be completely solved, and their goal is to democratize MEV to reduce its negative impact. "Democratization" may mean allowing more people to participate in the process of extracting MEV, thereby dispersing the profits and impacts brought by MEV, or establishing a mechanism so that everyone can benefit from MEV fairly. Others believe that MEV is an inevitable phenomenon. As long as there is profit to be made, there will always be people trying to extract MEV. Their focus is on finding a solution that can mitigate the negative impact of MEV while retaining its positive aspects. Currently, there are some projects and initiatives exploring different ways to solve the MEV problem or transform MEV into a positive force for the ecosystem. Current solutions and future directions for MEV include:
1. MEV smoothing
This is a strategy designed to reduce the variance and unpredictability of MEV by distributing it more evenly among blocks and validators. This approach prevents collusion or concentration among validators around high-value blocks, and reduces network congestion and gas fees caused by searchers competing for block space.
An example of MEV smoothing is MEV-Boost, a protocol auxiliary program that allows validators to outsource block production to experts called block builders, who can optimize block construction and share MEV revenue with validators. Another example is EIP-1559, an Ethereum Improvement Proposal. It changes the fee market mechanism and burns a portion of the base fee, which can reduce the incentive for validators to manipulate gas prices and reorganize blocks.
2. MEV burning
This is a strategy designed to reduce the total amount of MEV by destroying it or redirecting it to public goods. This prevents validators from being bribed or corrupted by searchers, as well as reducing the incentive for searchers to perform malicious MEV attacks.
An example of MEV burning is EIP-1559, which burns a portion of the base fee that would have been captured as MEV by validators or searchers. Another example is EIP-3368, an Ethereum Improvement Proposal that increases block rewards and makes them gradually decrease over time, which can reduce MEV's relative share of validator revenue and increase Ethereum's security budget.
3. MEV sharing
MEV smoothing/burning mainly addresses the end stage of the MEV supply chain, that is, the interaction between validators and block builders. However, there are other strategies that are being studied to minimize the instability of MEV in the early stages of the supply chain, which are generally referred to as "MEV sharing".
This is a strategy designed to redistribute MEV to users or other stakeholders in the ecosystem. This prevents validators or searchers from monopolizing MEV, as well as increasing the fairness and transparency of MEV distribution.
An example of MEV sharing is Flashbots, a research and development organization that provides transparent and democratized MEV extraction tools and services. Flashbots also launched the MEV-Share protocol, which aims to distribute part of the MEV revenue to users of the Ethereum ecosystem, such as through refunds or subsidies. Another example is Archer DAO, a decentralized autonomous organization that provides a platform for searchers and validators to collaborate and share MEV revenue with Ethereum infrastructure providers.
4. MEV Detection
Another possible way to mitigate the impact of MEV is to develop a sound and effective MEV detection algorithm or system. By detecting and resolving MEV, our goal is to promote fairness, transparency, and equal opportunities for all participants in the blockchain ecosystem. Specifically, we can start from the following aspects:
Comprehensively study existing MEV detection technologies and analyze their advantages and limitations. Deeply understand various MEV strategies, such as forced first transactions, sandwich attacks, and miners extracting liquidity.
Develop mechanisms to collect relevant data from blockchain networks, including transaction data, block data, and memory pool information. Use existing blockchain browsers or node APIs to collect real-time data for analysis.
Design and implement advanced algorithms to detect patterns and anomalous behaviors associated with MEV. These algorithms should be able to identify transaction ordering, time inconsistencies, gas price manipulation, and other indicators related to MEV strategies.
Machine learning techniques, statistical analysis, and graph neural networks are used to train models that can effectively classify and predict MEV situations. As new MEV strategies emerge, it is necessary to develop anomaly detection models that can adapt and evolve.
Integrate MEV detection systems with blockchain networks for real-time monitoring and analysis. Develop intuitive dashboards or interfaces that provide actionable insights to network participants, allowing them to identify and respond to possible MEV situations.
The above are some of the current solutions and future directions for MEV, but they are not the only solution. There are still many unresolved questions and challenges about how to measure, manage, and mitigate MEV in a way that is consistent with the values and goals of Ethereum. As Ethereum develops and grows, so will MEV, so more research and innovation is needed in this area.
Summarize
MEV is an emerging hot topic that makes profits by taking advantage of information asymmetry in blockchain transactions. Currently, the market is extremely heatedly discussing MEV. Some people are optimistic about MEV and believe that we can properly solve it, while others are pessimistic and believe that MEV can only be mitigated or exploited. We must pay attention to weighing the pros and cons of MEV and reducing its negative impact. We need to face the problem, deeply explore the advantages of MEV, and use it to serve us. At the same time, we need to change our mindset and not regard MEV as an enemy, but as an indispensable part of practice. Just like facing a dark forest, we should be cautious and vigilant about unknown situations to prevent potential threats and losses.
As the research on MEV continues to develop and mature, we look forward to more discussions and exchanges around this concept. Deeper research can develop solutions that effectively address the challenges posed by MEV. We also look forward to more regulatory intervention in the future to help build a more comprehensive and secure system. Such an approach will help build an environment in which MEV can have a positive impact, thereby contributing to the overall health and fairness of the blockchain ecosystem.
