1. Basic Information
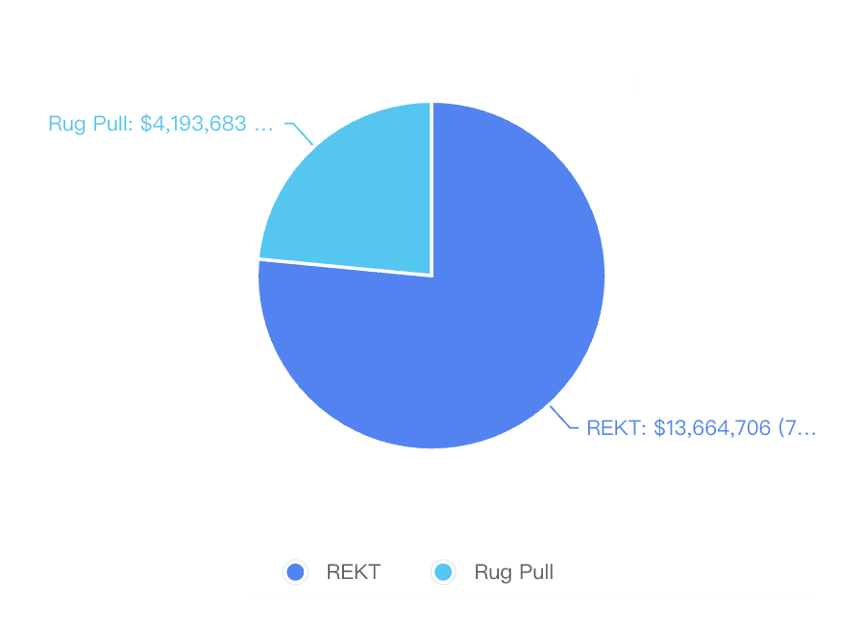
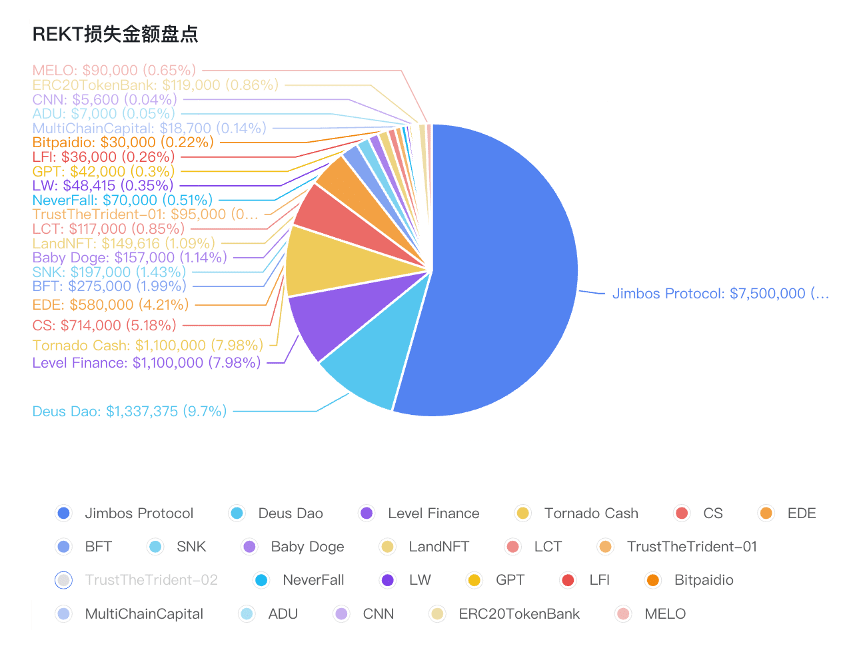
Security incidents in May 2023 caused approximately US$18 million in losses, a significant decrease compared to the previous month, but the frequency of security incidents has not decreased. Among them, the attack on Jimbos Protocol caused approximately US$7.5 million in losses. The Arbitrum chain’s Swaprum project Rug Pull caused losses of approximately $3 million. In addition, social media phishing incidents are still emerging one after another, and the project owner’s Discord is controlled and phishing links are published from time to time.
1.1 REKT Inventory
No.1
On May 1, Level__Finance was attacked and lost about $1.1M. The root cause was a logical problem in the LevelReferralController V2 contract. The claimMultiple function in the contract can pass in a set of epochs for users to claim rewards for each epoch, but if there are duplicate elements in the passed array, these rewards will be claimed repeatedly.
Attack preparation transaction:
https://www.oklink.com/cn/bsc/tx/0x 6 aef 8 bb 501 a 53 e 290837 d 4398 b 34 d5 d 4 d 88126751 2c fe 78 eb 9 ba 7 e 59 f 41 dad 04
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x e 1 f 25704187 2c 075 cbe 6 a 1212827 bc 346 df 3d ef 6 d 01 a 07914 e 4006 ec 43027165
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 61 bbd 8 c 1 bc 09 c 4 f 4549 f 3 f 77 be 5 ad 61 a 9929412 e
No.2
On May 3, the Never Fall project was attacked, resulting in losses of more than $70k. The attacker manipulated the price by exploiting a loophole in price calculation to make a profit.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x ccf 513 fa 8 a 8 ed 762487 a 0 dcfa 54 aa 65 c 74285 de 1 bc 517 bd 68 dbafa 2813 e 4 b 7 cb
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 53 b 757 db 8 b 9 f 3375 d 71 eafe 53 e 411 a 16 acde 75 ee
No.3
On May 3, the AutoDonateUkraine ($ADU) token suffered a flash loan attack, losing about $7k. The attacker used the deliver function to increase the $ADU in the pair, and then used skim to extract the excess $ADU. After repeating the operation several times, the price in the pair became unbalanced.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x c 6 f 6 b 70 e 9 e 35770 b 699 da 9 b 60244 d 461 d 0 2d b 66859 df 42319 c 3207 d 76931423 c
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x daacd 3431 a 29 a 2 1c0 bae 98 ee 220 b 075 bebe
No.4
On May 5, Deus Dao ($DEI) was attacked on both the BSC and Arbitrum chains, resulting in a loss of $1,337,375. The main vulnerability was the incorrect allowance calculation used in the BurnFrom function, which allowed users to manipulate the contract's allowance for themselves and transfer the tokens in the contract.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x de 2c 8718 a 9 efd 8 db 0 eaf 9 d 8141089 a 22 a 89 bca 7 d 1415 d 04 c 05 ba 107 dc 1 a 190 c 3
https://www.oklink.com/cn/arbitrum/tx/0x b 1141785 b 7 b 94 eb 37 c 39 c 37 f 0272744 c 6 e 79 ca 1517529 fec 3 f 4 af 59 d 4 c 3 c 37 ef
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 08 e 80 ecb 146 dc 0 b 835 cf 3d 6 c 48 da 97556998 f 599
https://www.oklink.com/cn/arbitrum/address/0x 189 cf 534 de 3097 c 08 b 6 beaf 6 e b2b 9179 dab 12 2d 1
No.5
On May 6th, the $BFT token appeared to have been attacked, resulting in a loss of approximately 275k USD.
Attack Trade: https://www.oklink.com/cn/bsc/tx/0x 5 a 89 e 083 e 8 e 3 ad 75 c 38 be 65 a 6 a 9 2d 7 e 32249 cf 9 b 5 ceb 304 bf 1 ae 2409241993 ff
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 7 e 39468760 c 45205 b 616 a 385 c 414 d 2 ffd 7 cbdc 33
No.6
On May 6, $MELO was attacked because there was no permission control in the mint function, and anyone could issue additional tokens and transfer them to their own account.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 3 f 1973 fe 56 de 5 ec d5 9 a 815 d 3 b 14741 cf 48385903 b 0 ccfe 248 f 7 f 10 c 2765061 f 7
Attack address:
https://www.oklink.com/cn/bsc/address/0x 9 bf 2c 7 c 21 f 3 c 488 a 1855 dcd 49158841 c 23 e 5 c 35 b
No.7
On May 9, the MultiChainCapital ($MCC) token suffered a flash loan attack. As a reflective deflation token, MCC did not emit a pair in the address, allowing the attacker to call the deliver function to mint the token and sell it for a profit of 10 eth.
Attack transaction:
https://www.oklink.com/cn/eth/tx/0x f 72 f 1 d 10 fc 6923 f 87279 ce 6 c 0 aef 46 e 37 2c 6652 a 696 f 280 b 0465 a 301 a 92 f 2 e 26
Attacker Address:
https://www.oklink.com/cn/eth/address/0x 8 a 4571 c 3 a 618 e 00 d 04287 ca 6385 b 6 b 020 ce 7 a 305
No.8
On May 10, $SNK tokens were attacked, and the attacker gained about 197k BUSD. The main vulnerability was that the reward calculation method was the amount of deposited funds * the deposit time. However, there was no corresponding relationship between the control time and the amount of deposited funds in the contract. The attacker could use an earlier time parameter and the current amount of funds for calculation.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 7394 f 2520 ff 4 e 913321 dd 78 f 67 dd 84483 e 396 eb 7 a 25 cbb 02 e 06 fe 875 fc 47013 a
Attacker Address:
https://www.oklink.com/cn/bsc/tx/0x 7394 f 2520 ff 4 e 913321 dd 78 f 67 dd 84483 e 396 eb 7 a 25 cbb 02 e 06 fe 875 fc 47013 a
No.9
On May 11, the LW token was attacked and the attacker made a profit of 48,415 $USDT. This was a price manipulation attack. When the attacker exchanged USDT for LW tokens, the repurchase mechanism of the marketing wallet was triggered, which increased the price of the token. The attacker then sold the LW tokens to make a profit.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x d 0 dd 0 c 8 aa 71860 ff 2d 7 fe 6 f 976389 2d 936 e 31 fb 8 c 1 aef 01 ec 5 ffbc 947 dbedbeb
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x ffc 21396 bc 3 c 981 f 057 b 4 ec 993 edb 2 a 305 ef 8 a 62
No.10
On May 11, TrustTheTrident was attacked and lost about $95k. The main reason is that listToken[] in the contract can be set in the addLiquidity() function. However, this operation should be done by the administrator. By exploiting this vulnerability, hackers can set their own tokens in listToken and call sell to sell.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 247 e 61 bd 0 f 41 f 9 ec 56 a 99558 e 9 bbb 8210 d 6375 c 2 ed 6 efa 4663 ee 6 a 960349 b 46 d
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x c 67 af 66 b 8 a 7 2d 3 3d edd 8179 e 1360631 cf 5169160
No.1 1
On May 13, bitpaidio was attacked and lost about $30K. The root cause of the problem was that Lock_Token() did not update the lock time correctly. The attacker did a lock() 6 months ago, which resulted in an excessive reward being calculated during withdraw().
Attack transaction: https://www.oklink.com/cn/bsc/tx/0x 1 ae 499 ccf 292 a 2 ee 5 e 55070 2b 81 a 4 a 7 f 65 cd 03 af 2c 604 e 2d 401 d5 2786 f 459 ba 6
Attack preparation transaction:
https://www.oklink.com/cn/bsc/tx/0x d 4 ee 8 a 5 ad 903 a 00 b 03 af 10653 cebde 64 d 81781 e 7 d 4140 a 309 ea 707613106 d 4 bb
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 878 a 36 edfb 757 e 8640 ff 78 b 612 f 839 b 63 adc 2 e 51
No.1 2
On May 13, TrustTheTrident was attacked again and lost about 279 BNB. TrustTheTrident allows users to short tokens, but the price depends on the pair and is easily manipulated.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 7 d 04 e 95 3d ad 4 c 880 ad 7 2b 655 a 9 f 56 bc 5638 bf 4908213 ee 9 e 74360 e 56 fa 8 d 7 c 6 yr
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 1581262 fd 72776 ba 5 da 2337 c 4 c 4 e 1 b 9 2c 6 e 36 ae 6
No.1 3
On May 14, TrustTheTrident was attacked again, and the amount of loss was unknown. The root cause was that the Claim() function of the StakingRewards contract did not correctly verify the input parameters, allowing the attacker to pass a fake token instead of USDT to obtain more rewards.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x fe 80 df 5 d 689137810 df 01 e 83 b 4 bb 51409 f 13 c 865 e 37 b 23059 ecc 6 b 3d 32347136
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x a 3 aa 817587556 c 023 e 78 b 2285 d 381 c 68 cee 17069
No.1 4
On May 14, landNFT was attacked. The main reason was that the project's mint function lacked permission control. The attacker minted 200 LandNFTs for himself and made a profit of approximately 149,616 BUSD.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 4 db 1550 3 aa 78 05 93 bfd 8 fbe 21 b 6 eba 5 cce 50 dc 06688949 ab 479 ebed
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 96 b 89 c 2560 bcc 43 c 34 2c 1 2b a 9 c 3 3d ab 7 eb 571 a 90
No.1 5
On May 20, Tornado Cash was attacked by a malicious proposal. The loss was about $1.1M. The attacker proposed a malicious proposal. After the proposal was passed, the proposal contract code was changed by self-destructing the contract and then redeploying it. When the Tornado Cash contract executed the proposal, additional votes were issued to the address prepared by the attacker to gain control of the contract.
Attack transaction:
https://www.oklink.com/cn/eth/tx/0x 3274 b 6090685 b 842 aca 80 b 304 a 4 dcee 0 f 61 ef 8 b 6 afee 10 b 7 c 7533 c 32 fb 75486 d
Attacker Address:
https://www.oklink.com/cn/eth/address/0x 592340957 ebc 9 e 4 afb 0 e 9 of 221 d 06 fdddf 789 de 9
No.1 6
On May 23, the LFI token was attacked, resulting in a loss of approximately 36k USD.
Attack transaction:
https://www.oklink.com/cn/polygon/tx/0x a 0480 d 0 f 7 c 8 d 8 bf 898 cadde 954 e 77 3d dc 3740 f 1 ffa 31 cdd 98 fe 4 c 5 f 5 d 8266243
Attacker Address:
https://www.oklink.com/cn/polygon/address/0x 11576 cb 3d 8 d 6328 cf 319 e 85 b 10 e 09 a 228 e 84 a 8 de
No.1 7
On May 23, $CS tokens were attacked by flash loans, and the attackers made a profit of about 714k USD. The main reason for the vulnerability is that $CS tokens will destroy part of the tokens in the pair to increase the price during each transaction (or transfer). The burnAmount is calculated by sellAmount, but the value of sellAmount is not updated. This allows the attacker to push up the token price through multiple transactions and sell the token at a high price to make a profit.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 906394 b 2 ee 093720955 a 7 d5 5 bff 1666 f 6 cf 6239 e 46 place 8 of 99 d 635 2b 9687 baa
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x 2 cdeee 9698 ffc 9 fcabc 116 b 820 c 24 e 89184027 ba
No.1 8
Related Links:
On May 23, LOCALTRADERSCL ($LCT) was attacked and lost about 384 BNB.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 57 b 589 f 631 f 8 ff 20 e 2 a 89 a 649 c 4 ec 2 e 35 be 72 eaecf 155 fdfde 98 1c0 fec 2b e 5 ba
https://www.oklink.com/cn/bsc/tx/0x 49 a 303862 2b f 6 dc 367 2b 1 b 7366382 a 2c 51 3d 713 e 06 cb 7 c 91 ebb 8 e 256 ee 300 dfb
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x d 771 dfa 8 fa 59 bd 2d 1251 a 0481 fca 0 cf 216276 dd 7
No.1 9
On May 25, GPT was attacked and lost about 42k USD. The main reason for the vulnerability is that it can trigger the token burn mechanism by inserting tokens into the pair and then skimming, thereby pushing up the price.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 49 a 303862 2b f 6 dc 367 2b 1 b 7366382 a 2c 51 3d 713 e 06 cb 7 c 91 ebb 8 e 256 ee 300 dfb
No.20
On May 26, CNN was attacked and the attacker made a profit of about 5.6k USD.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x d 3 bf d5 6 c 1 f 501 d 449199 a 4739 f 213631419 dc 6630 e 28355 ce 58196791 eed 63 fc
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x d 771 dfa 8 fa 59 bd 2d 1251 a 0481 fca 0 cf 216276 dd 7
No.2 1
On May 28, jimbosprotocol was attacked, resulting in a loss of approximately $7.5M.
Attack transaction:
https://www.oklink.com/cn/arbitrum/tx/0x 44 a 0 f 5650 a 038 ab 522087 c 02 f 734 b 80 e 6 c 748 afb 207995 e 757 ed 67 ca 037 a 5 eda
Attacker Address:
https://www.oklink.com/cn/arbitrum/address/0x 10 2b e 4 bccc 2696 c 35 f d5 f 5 bfe 54 c 1 dfba 416 a 741
No.2 2
On May 29, babydogecoin was attacked, resulting in a loss of approximately $157,000. The key to the attack was that in the FarmZAP contract, the purchase and sale of babydoge enjoyed a 0 fee rate. The attacker used the babydoge reflux mechanism to create a price difference between FarmZAP's babydoge router and the babydoge pair in pancake to achieve arbitrage.
Attack transaction:
https://www.oklink.com/cn/bsc/tx/0x 098 e 7394 a 1733320 e 0887 f 0 de 2 2b 18 f 5 c 71 ee 18 d 48 a 0 f 6 d 30 c 76890 fb 5 c 85375
Attacker Address:
https://www.oklink.com/cn/bsc/address/0x cbc 0 d 0 c 1049 eb 011 d 7 c 7 cfc 4 ff 556 d 281 f 0 afebb
No.2 3
On May 30, ede_finance’s vault was exploited, resulting in a loss of approximately $580,000. The attacker has since returned 90% of the funds.
Attacker Address:
https://www.oklink.com/cn/arbitrum/address/0x 80826 e 9801420 e 19 a 948 b 8 ef 477 fd 20 f 75493 2d c
No.2 4
On May 31, ERC 20 TokenBank was attacked, resulting in a loss of approximately $119,000.
Attack transaction:
https://www.oklink.com/cn/eth/tx/0x 578 a 195 e 05 f 04 b 19 fd 8 af 6358 dc 6407 aa 1 add 87 c 3167 f 053 beb 990 d 6 b 4735 f 26
Attacker Address:
https://www.oklink.com/cn/eth/address/0x c 0 ffeebabe 5 d 496 b 2d de 509 f 9 fa 189 c 25 cf 29671
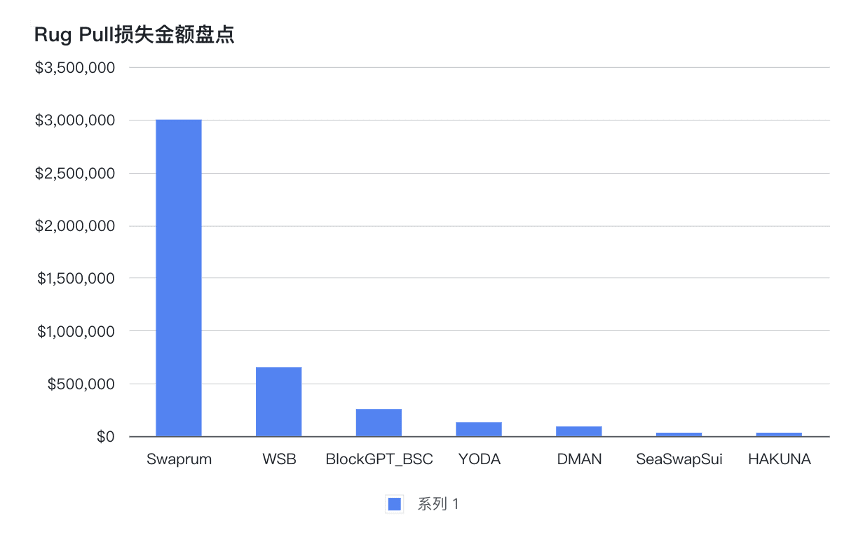
1.2 RugPull Inventory
No.1
On May 04, zjz.eth rugpull of wsbcoinofficial ($WSB), $WSB fell 86%, zjz.eth sold most of WSB and made a profit of 334 ETH (about 653k USD).
No.2
On May 05, YODA token rugpull, YODA fell -100%, yodacoineth has deleted its social accounts/groups, scammers have transferred 68 ETH ($ 130 K) to FixedFloat.
No.3
On May 08, Hakuna Matata rugpull, HAKUNA fell by -100%.
No.4
On May 09, Derpman rugged, DMAN fell -100%, with a profit of about 48.55 $ETH.
No.5
On May 15, the rugpull gang has been creating fake tokens such as #PEPEPE, #LADYS, #BENZ, #GGBOND, #BENEN, #NEWPEPE, #PEN, #TURBOO,#PEPELOLin the past 3 days. The scammers have transferred about 12 ETH to MEXC.
No.6
On May 19, Swaprum on Arbitrum rugged, making a profit of approximately $3 million. The deployers of Swaprum used the add() backdoor function to steal the LP tokens staked by users, and then removed liquidity from the pool for profit.
No.7
On May 26, @SeaSwapSui’s rugpull, which deleted its Twitter and other social accounts, caused the administrator to urgently withdraw SUI from the token sale contract, totaling 32,787 SUI ($32,000).
No.8
On May 30, BlockGPT_BSC rugged. Profit of about 816 BNB (about $256K).
1.3 Social Media Scams and Phishing
No.1
On May 01, a phishing website promoted on Twitter appeared. Do not interact with hxxps://claimbob.site/.
No.2
On May 02, a fake CertiK phishing website appeared. Do not interact with hxxps://claim.certik.app/.
No.3
On May 04, the Syncera_io Discord server was attacked. Please do not click on any links until the team confirms that they have regained control of the server.
No.4
On May 04, a fake Pepe Coin account appeared on Twitter. Do not interact with hxxps://pepegives.xyz/.
No.5
On May 05, the FeetLabsHQ Discord server was attacked. Please do not click on any links until the team confirms that they have regained control of the server.
No.6
On May 6, the STFX_IO Discord server was attacked. Please do not click on any links until the team confirms that they have regained control of the server.
No.7
May 07, fake Pepe claim website appears, do not interact with hxxps://pepegift.org/
No.8
On May 08, phishing links were posted in the Evmos Discord server. Please do not click on any links until the team confirms that they have regained control of the server.
No.9
On May 08, fake MetaMask accounts appeared on Twitter. Do not connect to the hxxps://meta-token.net/# website.
No.10
On May 08, a fake Bob claim website appeared, do not interact with hxxps://bob-airdrop.com/.
No.11
On May 9, a fake PeckShield account appeared on Twitter. Do not believe any eye-catching content posted by this account.
No.12
On May 09, a fake Ben airdrop website appeared. Do not interact with hxxps://bencoineth.net/.
No.1 3
On May 10th, a fake Pepe claim website appeared, do not interact with hxxps://rewardspepe.com/.
No.1 4
On May 11th, please be aware of the fake layerzero claim website being promoted on Twitter and do not interact with the hxxps://layerzero-network.app/ website.
No.1 5
On May 14, the OnchainTrade Discord server has been hacked. Please do not click on any links until the team confirms that they have regained control of the server.
No.1 6
On May 14, the opentensor Discord server was compromised. Please do not click on any links until the team confirms that they have regained control of the server.
No.1 7
On May 15th, the BTFDRabbits Twitter and#Discordservers were both compromised. Please do not click on any links on either platform until the team has confirmed control.
No.1 8
On May 15th, a phishing link was posted in the Tyche Protocol Discord server. Please do not click on any links until the team confirms that they have regained control of the server.
No.19
On May 16th, the taskonxyz Discord server has been compromised by a fake phishing link being posted, do not interact with hxxps://airdrop.taskon.tech/.
No.2 0
As of May 16th, the freshcut#Discordserver has been compromised. Please do not click on any links until the team confirms they have regained control of the server.
No.2 1
As of May 16th, the MorphexFTM#Discordserver has been compromised. Please do not click on any links until the team confirms they have regained control of the server.
No.2 2
The NEARProtocol Discord server has been compromised on May 17th. Please do not click on any links until the team confirms that they have regained control of the server.
No.2 3
The lifiprotocol Discord server has been compromised on May 17th. Please do not click on any links until the team confirms that they have regained control of the server.
No.2 4
As of May 17th, the auroraisnear Discord server has been compromised. Please do not click on any links until the team confirms that they have regained control of the server.
No.25
As of May 18th, the Probably 0 Discord server has been compromised. Please do not click on any links until the team confirms that they have regained control of the server.
No.26
On May 18th, the oDDbOOG Discord server was attacked. Please do not click on any links until the team confirms that they have regained control of the server.
No.27
On May 19th, TheHoraHub Discord server was attacked. Please do not click on any links until the team confirms that they have regained control of the server.
No.28
The ArbitrumNewsDAO Discord server has been compromised on May 19th. Please do not click on any links until the team confirms that they have regained control of the server.
No.29
As of May 20th, the avianfoundation Twitter account has been compromised and is promoting a phishing site, do not interact with hxxps://avn.finance/.
No.30
May 20th, beware of the fake yoda coin claim website promoted on Twitter, do not interact with hxxps://claim-yoda.com.
No.31
May 20th, Beware of the fake Psyop claim website promoted on Twitter, do not interact with hxxps://claim-psyop.live/.
No.3 2
The VenomBridge Discord server has been compromised as of May 21st. Please do not click on any links until the team confirms they have regained control of the server.
No.3 3
The asymmetryfin Discord server has been compromised on May 22nd. Please do not click on any links until the team confirms they have regained control of the server.
No.3 4
May 22, fake Dex Tools Twitter account. Do not interact with the hxxps://dextoois.com/ website.
No.35
On May 22nd, the Superlotl Discord server was attacked, please do not click on the link until the team confirms that they have regained control of the server.
No.36
As of May 23rd, the zerpmonxrp Discord server has been compromised, please do not click on the link until the team confirms they have regained control of the server.
No.37
On May 23rd, the mail3dao Discord server was attacked. Please do not click on the link until the team confirms that they have regained control of the server.
No.38
On May 23rd, a phishing link was posted in the MetaStars Striker Discord server. Do not click on the link until the team confirms that they have regained control of the server.
2. Safety Summary
In May 2023, DeFi experienced multiple security incidents. Code logic vulnerability exploitation and flash loan price manipulation are still common attack methods used by hackers. Tokens with more complex economic models such as reflection mechanism and reflux mechanism are more likely to become targets of attack. At the same time, some new attack methods have also emerged, such as the malicious proposal attack suffered by Tornado Cash. In order to avoid similar incidents from happening again, developers need to take actions to ensure the security of the project, including fully verifying the code logic and economic model, regularly auditing the project, and publishing a bug bounty program after the project goes online. At the same time, social media phishing incidents have also occurred frequently this month. Investors need to remain vigilant and pay attention to fully verifying the authenticity of the link before interacting with it to avoid asset losses.
