The main point
Application Programming Interface (API) keys can be used to provide easy access to user data for certain programs.
However, API keys can be compromised if not managed properly. Learning how to use your API keys securely is critical to preventing your assets from being compromised.
Binance now supports RSA API key pairs for increased security. Learn how to create and use it.
API keys allow users to easily access their data. From RSA key pairs to API key whitelists, learn five tips from Binance to keep your API keys safe.
Application Programming Interface (API) keys are an efficient way to provide access to user data for certain programs to act on the user's behalf. However, API keys can introduce vulnerabilities if not stored and used properly. For example, a malicious actor who steals or phishes their victim's API key could potentially gain access to the victim's funds. Learn how to keep your assets safe with our five API key security tips.
1. Don't Share Your Keys with Others
The secret key (HMAC) and private key (RSA) of your API key are highly sensitive data. You are strongly advised not to disclose this information. With that key, anyone can initiate API requests on your behalf without being detected by our risk monitoring systems.
You should also frequently check the active API keys in your account via the API management page. If you suspect the security of any API key has been compromised, don't hesitate to delete it and replace it with a new one. It's also a good idea to frequently delete old API keys and replace them with new ones, similar to some systems that require passwords to be changed every 30-90 days – whether you're actively using them or not.
2. Be diligent in access management
API keys are a useful tool for automated trading, position and risk monitoring, and taxes. Therefore, you may be tempted to enable all permissions for a single API key to use for multiple purposes, such as API trading and data querying. However, this reduces the security of the key – if your API key is compromised, hackers can gain full access to your account and funds.
You're safer using an API key for a single app and enabling the permissions required for that purpose only. For example, if you want to monitor trading risk, report taxes, and execute Spot and Futures API trades, you must create at least four keys, each for one of the following purposes:
Spot trading
Futures trading
Tax data query
Trading data query (read only permission)
On Binance, you can create up to 30 API keys for each sub-account.
3. Store Your API Key Data Securely
As mentioned, if your API key falls into the hands of a criminal, your assets may be compromised. Just like how you protect private keys, don't store your API details in plain text. Instead, encrypt or use a trusted secrets manager. You should also avoid using cloud-based solutions to store your API keys, as they may be vulnerable to hacking.
It is also recommended that you do not store your API key in your application's source code or repository.
Consider storing your API key data in files or environment variables outside the third-party management systems you use to avoid sharing your personal information with them.
Because RSA private keys support password protection, users using RSA keys must add a password to any RSA private keys they own.
4. Use IP Whitelist
Binance strongly recommends users use IP whitelisting on all their API keys, regardless of the permissions or purpose of the API key. With IP whitelisting, your API key can only be accessed from a specific IP address. This prevents malicious actors from using your API key if it is compromised. Therefore, you must whitelist all IP addresses used to use your API key.
Beware of fraud
Although API keys cannot be used to initiate pull requests without whitelisting IPs, you need to protect your API keys. If hackers gain access to your keys, they can use assets with relatively small trading volumes to place trades and slowly siphon assets from your wallet. By executing purchases of unwanted assets from hacker accounts and exchanging them for your blue chip assets (BTC, BNB, etc.), you will end up owning the altcoins you never intended to buy. In other words, hackers can use your API key to exchange your assets for their assets in markets that have relatively low liquidity.
To prevent such fraud, Binance implemented an automatic API key deletion policy in December 2022. If your API key does not use a whitelisted IP and is inactive for 30 days, it will be deleted. To avoid automatic deletion, you should whitelist your IP.
5. Use RSA Key Pair
RSA (Rivest-Shamir-Adleman) key pair is a mechanism that uses a public key and a private key to secure data transmission.
With an RSA key pair, the private key used to create the signature does not need to be shared. This means that as long as the private key is kept secret and secure, others cannot initiate authentic requests on your behalf.
Binance Now Supports RSA API Keys
Binance now supports RSA API keys. You can now create an RSA public key and private key pair, register the public key on Binance, and use the corresponding private key to make signed API requests.
How to create an RSA key pair on Binance?
Download the latest version of the official RSA Key Generator.
Launch the app. You can create, copy, or save keys. You can also customize the size of your keys.
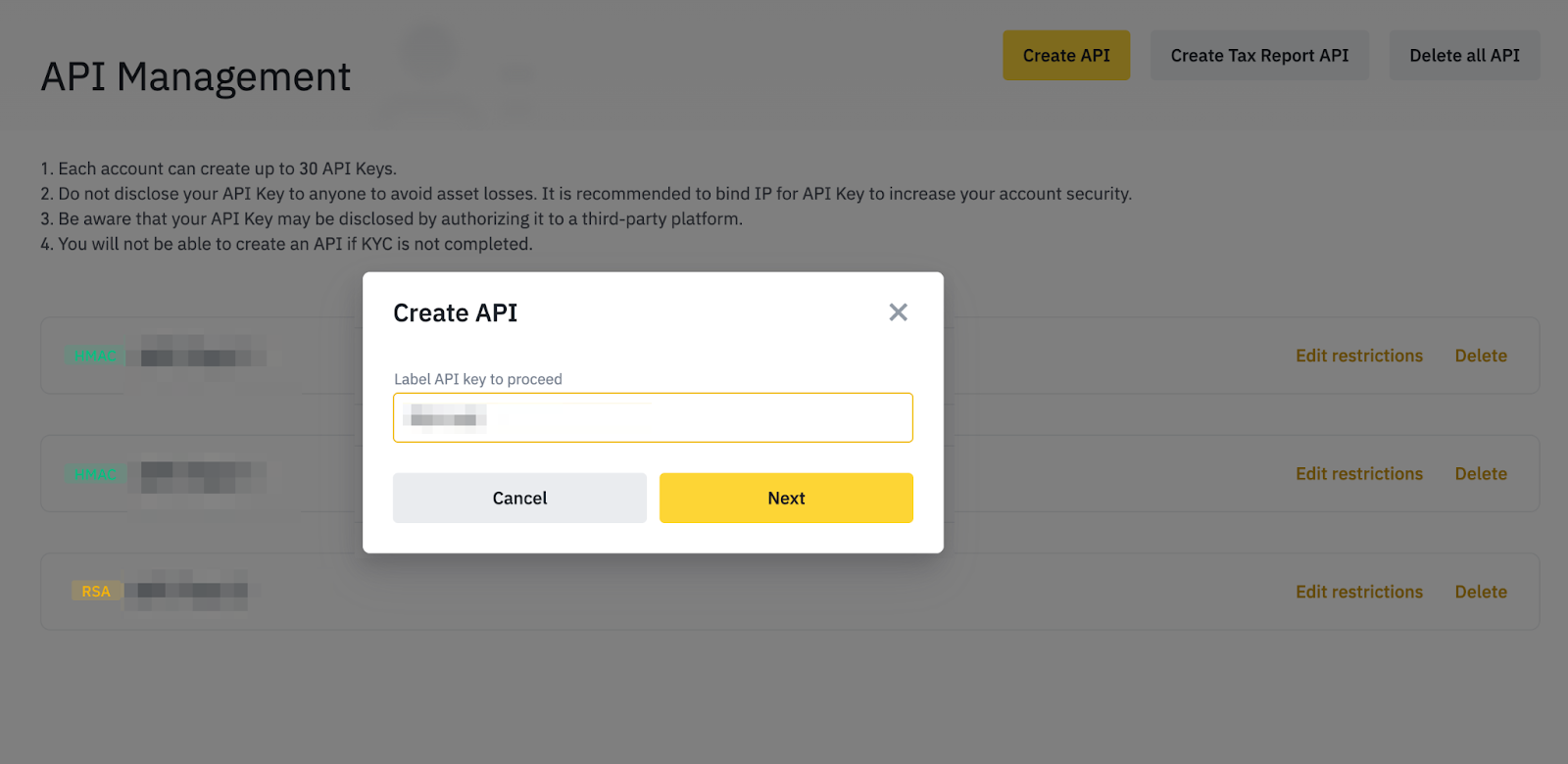
To register your RSA key via the Binance App, go to [Profile] - [API Management] - [Create API] - [Create API Key].
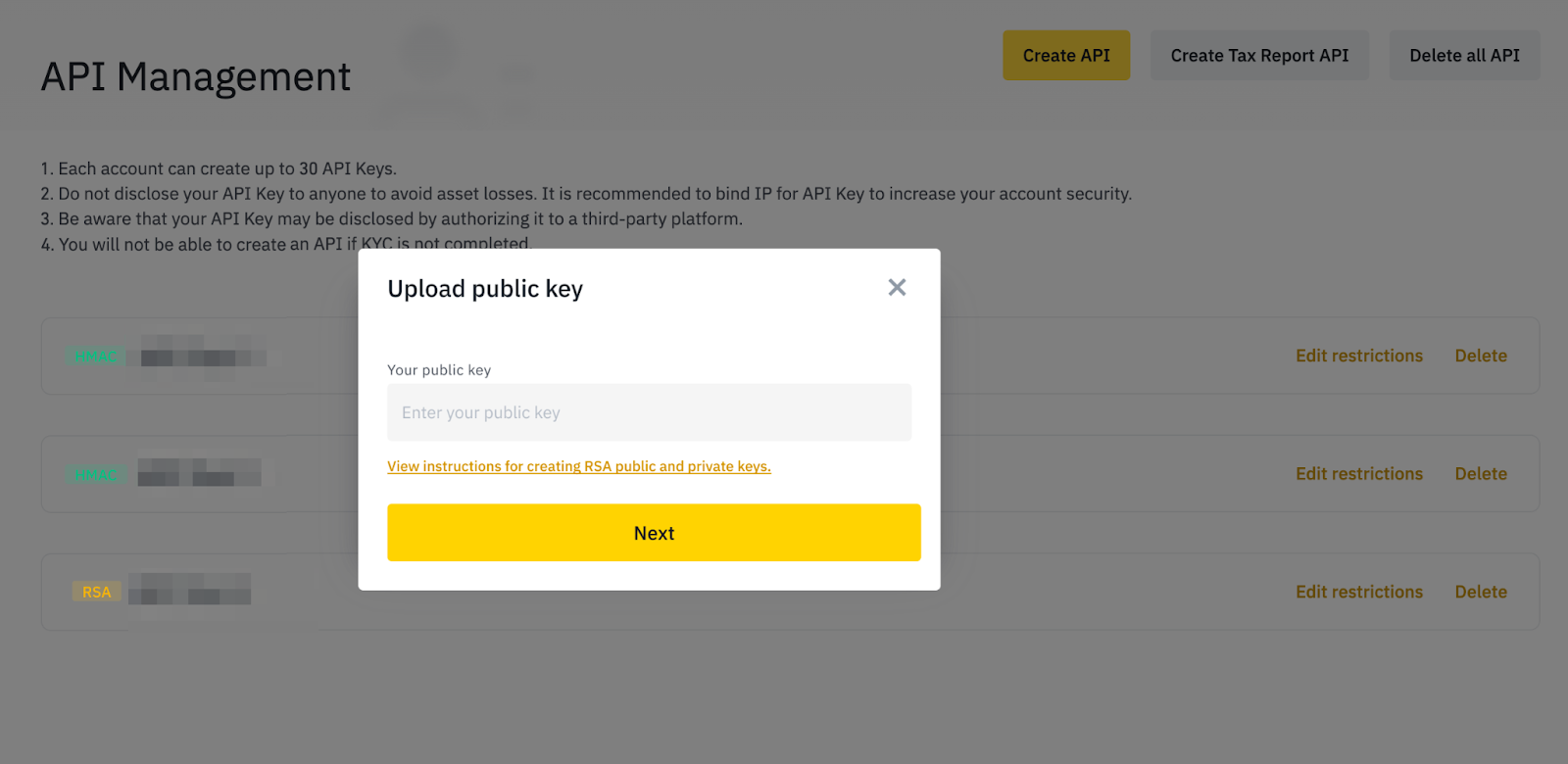
Copy the public key from the RSA Key generator, then paste it into the box to register.
Enter a name for your API key, click [Next], and then complete 2FA to complete registration.
For more details, please see our guide on How to Create an RSA Key Pair to Send API Requests on Binance.
Further Reading
(Announcement) Binance Now Supports RSA API Keys (2022-12-29)
(Blog) How to Identify and Avoid Scams from Common Crypto Scammers
(Blog) Fake Funds Recovery Services: How to Avoid This Type of Scam
(Blog) How to Recognize and Avoid P2P Fraud
(Blog) Fraudster Creates AI Hologram of Me to Defraud Crypto Projects