
Web3 decentralized data cloud OORT
·Wikipedia’s explanation of decentralized computing
·The development prospects of decentralized cloud computing
·Advantages of decentralized cloud computing
·Decentralized cloud computing application fields
·OORT core technology·Trusted Proof of Honesty (PoH) consensus algorithm
·Verifiable computational problems
·First mover advantage
·What is POH?
·PoH consists of two stages:
·core team
·Project consultant team
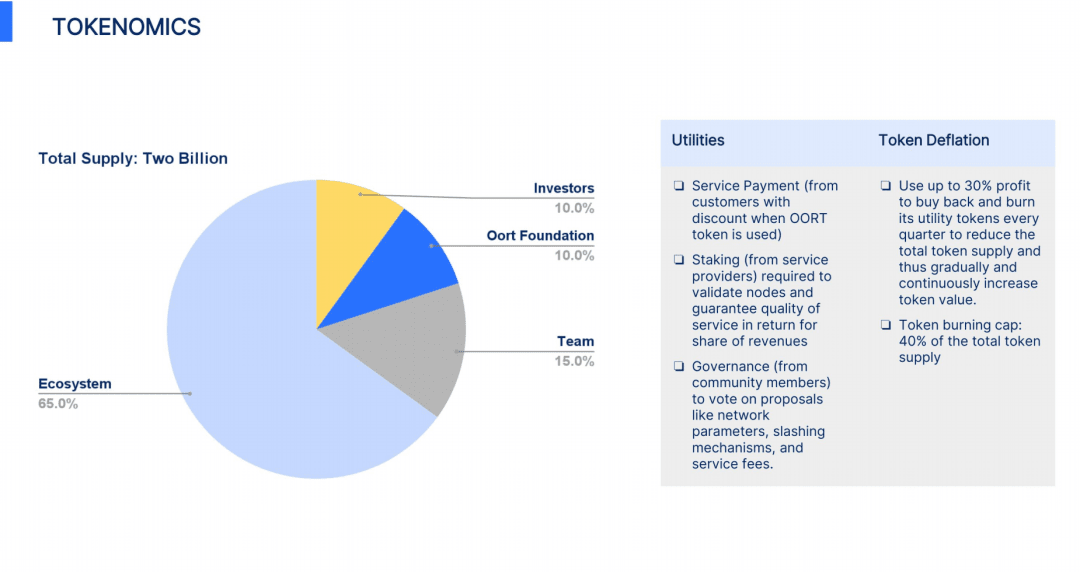
·Tokens rules
This POH verification mechanism, on the one hand, can effectively promote users to become "policemen" to independently check and verify calculation problems through the incentive mechanism, and on the other hand, punish perpetrators through the pledge deposit penalty mechanism.
Source: OORT, Toubao, OFweek Weike.com Artificial Intelligence, Sina Finance, NetEase News, Golden Finance and major public media
Compilation: Reporting Finance
Preface
Today, centralized tech giants dominate the world of cloud computing — but this decentralized platform believes there may be another way forward.
Industry analysts believe that traditional cloud computing infrastructure is characterized by its centralized points of failure and lack of data privacy. In fact, data protection and integrity are currently not a guaranteed guarantee for any of the major cloud service providers. To make matters worse, "insider threats, moral hazard" are still cited as one of the most common ways in which private data is leaked.
The team behind Web3 Data Cloud OORT is taking a different approach to cloud computing.
Wikipedia’s explanation of decentralized computing
Decentralized computing is a computing model that allocates hardware and software resources to each workstation or office. In contrast, centralized computing centralizes most computing functions locally or remotely. Decentralized computing is a modern computing model. In contrast, centralized computing was prevalent in early computing environments. A decentralized computing system has many advantages over traditional centralized networks. Desktop computers are evolving rapidly, and their potential performance far exceeds the performance requirements required by most business applications. As a result, most desktop computers have a surplus of idle computing power. A decentralized computing system can unleash this potential and maximize efficiency. However, whether it increases the effectiveness of the overall network is still debatable. https://zh.wikipedia.org/wiki/%E5%8E%BB%E4%B8%AD%E5%BF%83%E5%8C%96%E8%AE%A1%E7%AE%97
The development prospects of decentralized cloud computing
In the future, with the in-depth development of new technology applications of the Internet and blockchain and the further expansion of data volume, the development prospects of the decentralized application market are broad.
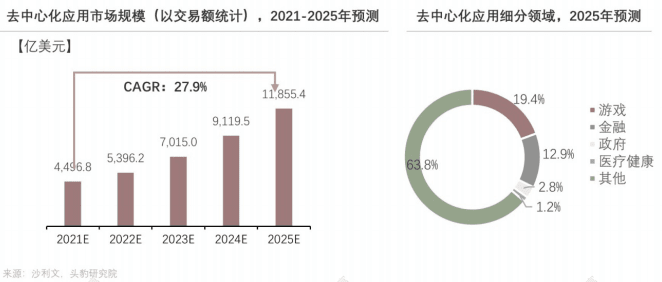
The decentralized application market benefits from the development of 5G, IoT, artificial intelligence, and Internet technology and has huge potential for future development.
It is expected that the decentralized application market will achieve an average annual compound growth rate of 27.9% from 2021 to 2025, and the global decentralized application market size (in terms of transaction volume) will reach US$1.18554 billion in 2025. Among them, applications in the gaming field account for the highest proportion (accounting for 19.4%), followed by the financial field (accounting for 12.9%). Medical health and government agency applications also occupy a certain scale, mainly due to decentralized applications compared to centralized applications. The application focuses on user-centeredness, reducing users' dependence on huge data servers controlled by cloud vendors, and attaches great importance to personal data security and privacy.
Decentralization has brought unprecedented data innovation value, and users have become contributors and beneficiaries of value creation. It will stimulate everyone's innovation ability. As the bottom layer of the entire environment, the infrastructure can better protect everyone's privacy and data security through decentralization. This new wave of Web3 is driving a new round of IT changes. The era of digital innovation is extending from mobile phones to all things in the ecosystem, with data as the core radiating to all fields.
Advantages of decentralized cloud computing
Compared with traditional centralized cloud computing, decentralized cloud computing has outstanding advantages in construction cost, security performance, user experience and operation methods.
Decentralized cloud computing applications
Decentralized cloud computing is used in many fields such as finance, medical care, social communications, games, energy, etc., and its application scope is constantly expanding.
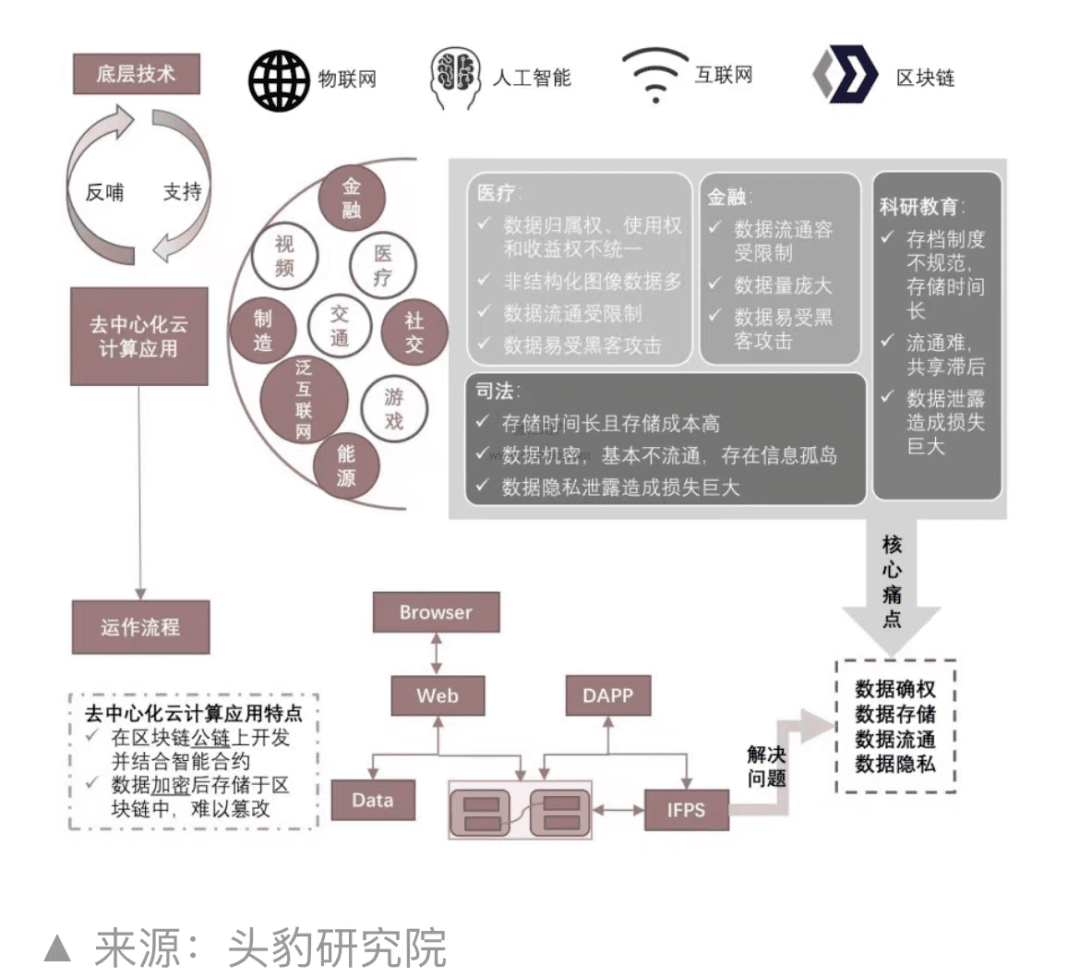
Decentralized cloud computing application areas
Decentralized cloud computing can be used to solve data confirmation, data storage, data circulation and data privacy issues in various fields such as finance, medical care, scientific research and education, justice, and social networking. For example, a lot of judicial data in the judicial field involves court trial notarization materials, prisoner private information and other confidential data. The information system between courts is relatively closed, and judicial data involves state secrets and private case information. Once data privacy is leaked, it will cause great losses. .
With the rapid development of the Internet and blockchain technology, the industrial chain is prosperous, the platform economy is developing rapidly, related large-scale enterprises continue to emerge, and entrepreneurs frequently flock in; the sharing economy is also developing very hotly in the current global market, and attracts a large amount of capital After many years of development of the sharing economy, few people are interested in this field due to the difficulty of technical requirements in the field of computer resource sharing.
The Web3 decentralized data cloud platform OORT team seized the market opportunity. After years of research, it filled the gap in the shared computing power market in the computer field. The OORT team released the Web3 decentralized data cloud platform in 2019, aiming to achieve global computing resources. Sharing to increase the utilization rate of global idle computing power, and to meet the needs of multiple parties by using cryptocurrency as a means of payment for computing power.
Web3 decentralized data cloud platform OORT faces many challenges when outsourcing computing tasks to another party, one of which is verifiable computing problems. Verifiable computing problems refer to Verifiable Computing ("VC" for short), which means that computing tasks can be outsourced to third-party computing power providers; (untrusted) third-party computing power providers need to submit A proof of correctness of the calculation results. A long-standing problem is how users can effectively verify calculation results without re-executing the task. This problem has troubled computer scientists for many years. It was not until the emergence of the honesty proof mechanism POH that this problem had an achievable solution.
OORT has currently obtained 2 patents in the most important aspects of this field.
The first is a distributed computing network based on blockchain technology,
The second is Proof of Honesty (PoH). This is the first verifiable problem to solve the distributed cloud computing process. This is where we stand out and stay ahead of other projects. It is worth mentioning that PoH allows us to verify the outsourced calculation results, which establishes a foundation of trust for our ecosystem.
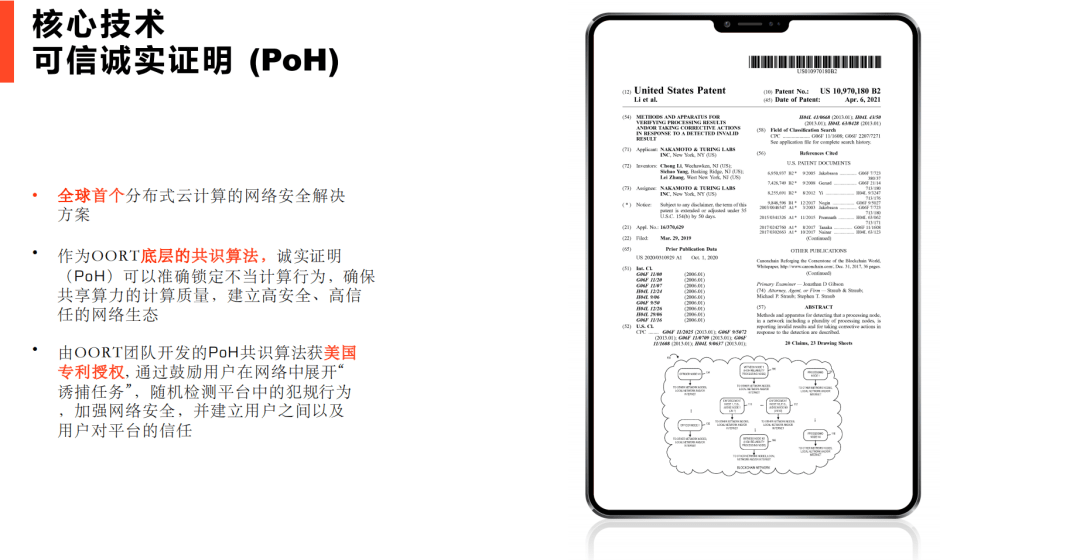
OORT core technology·Proof of Honesty (PoH) consensus algorithm
• The world's first distributed cloud computing network security solution.
• As the underlying consensus algorithm of OORT, Proof of Honesty (PoH) can accurately lock inappropriate computing behaviors, ensure the computing quality of shared computing power, and establish a highly secure and high-trust network ecosystem.
• The PoH consensus algorithm developed by the OORT team is authorized by the United States patent. It encourages users to carry out "trap tasks" in the network, randomly detects foul play in the platform, strengthens network security, and establishes relationships between users. and users’ trust in the platform.
verifiable computational problems
The problem of outsourcing computational tasks to another party so that clients/users can efficiently verify results without having to re-perform the tasks represents a long-standing dilemma in computer science. For one thing, providers don't necessarily have a strong incentive to ensure correctness. On the other hand, it is difficult for complex and large-scale providers (e.g., cloud servers) to guarantee that tasks are always executed correctly 15 due to configuration errors, hardware randomness, etc. For nearly a decade, computer scientists have been studying this problem, called verifiable computation.
Written by the Oort (CCN) research team on April 6, 2021, US patent - "Methods and apparatus for verifying processing results and/or taking corrective actions in response to a detected invalid result Methods and apparatus for taking corrective actions)" (https://uspto.report/patent/grant/10,970,180) certified by the U.S. Patent Office. This patent uses the tools of probability theory and economic models, and is based on blockchain technology - the "Proof of Honesty (PoH)" consensus algorithm, to provide a long-standing computer science problem - verifiable computing problem. The solution is regarded by the edge computing community as the world's first effective solution to verifiable computing problems.
It is another major technological breakthrough to achieve large-scale commercial use of distributed sharing of global computing resources in the current economic era where the idle computing power market is in urgent need of integration.
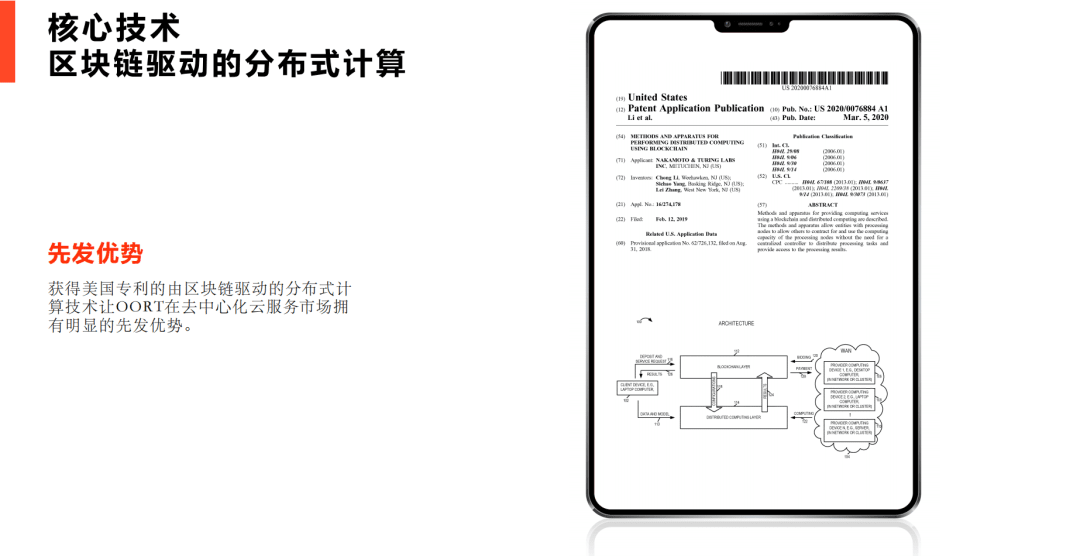
first mover advantage
The U.S. patented distributed computing technology driven by blockchain gives OORT a leading position in the decentralized cloud service market.
There is a clear first-mover advantage.
What is POH?
The full name of POH is "Proof of Honesty", which was proposed by the OORT research team on March 29, 2019. It aims to solve the problem of verifiable computing and realize the trustworthiness of the decentralized/distributed computing power sharing platform.
Until then, computer scientists had two solutions to the problem of trustworthy computing.
1. Perform repeated verification calculations on multiple computing devices. This solution is not only expensive, but also requires the assumption that the computing device itself will not cause errors in the calculation results due to malfunctions. Obviously, this verification method is not often effective. For example, the hardware and software of all devices in cloud services are usually exactly the same. If the calculation error is caused by the device, the consistency of repeated calculation results cannot guarantee the final correctness. In the end, high costs are spent, and accurate results cannot be obtained. verification results, causing a loss of manpower and material resources.
2. Run a small set of sample calculations and then review the results of those samples. However, insufficient sample size makes this solution less effective. There are other solutions, such as trusted hardware, but the premise is that there needs to be a complete chain of hardware trust.
The above solutions obviously cannot effectively solve the verifiable computing problem. The "Proof of Honesty (POH)", which has been studied by the OORT R&D team for many years, is based on blockchain technology and was inspired by "police trapping offenders". Let the rental end user act as a "policeman", and assign the computing power provider a decoy task with a pre-known result, and verify the task result through the smart contract, so as to detect and capture the malicious computing power provider in the network, and crack down on cheating Severe financial penalties will be imposed on offenders. This method has been verified by many parties and can effectively solve computer verification problems.
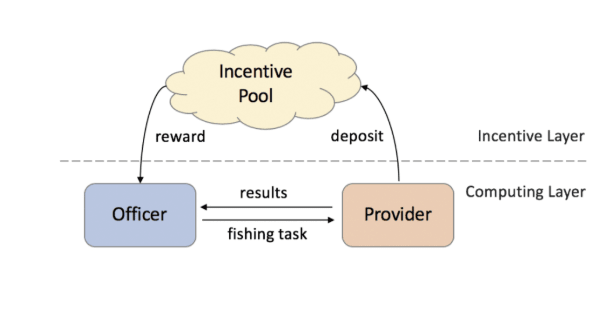
PoH consists of two stages:
Phase 1 - Preparation: Users wishing to become "cops" will build a database of sting missions. The database contains one or more computing tasks that have been verified by network nodes and saved on the chain. Every user can become a "cop" to receive trapping rewards. At the same time, computing power providers must submit a deposit before sharing computing power. The deposit amount will be much higher than their task rewards. For cheating computing power providers, their rewards and their deposits will be forfeited. This will effectively guarantee the platform’s computing power. Trustworthiness.
Phase 2 - Execution: In this phase, the network randomly assigns tasks in the database to computing power providers. After the Provider feeds the results back to the "Police", the "Police" can easily determine the correctness of the Provider's calculations by comparing the results to the correct results in their repository of sting missions. This "police" will publish these two results on the blockchain by validating the smart contract. The "judge", i.e. some or all of the nodes running this verification smart contract, will decide whether the "cop's" judgment is correct. If proven correct, the rewards in the reward pool will be allocated to the "police" as an incentive, and the provider's deposit will be forfeited and entered into the reward pool.
This POH verification mechanism, on the one hand, can effectively promote users to become "policemen" through the incentive mechanism to autonomously check and verify calculation problems. On the other hand, it can punish evildoers through the pledge deposit penalty mechanism. Due to the high cost of evildoing, this will effectively reduce The emergence of evildoers. It is obvious that PoH has become the lowest cost and most efficient solution to verifiable computing problems so far. It is a very effective technical means to establish a global decentralized/distributed trusted shared computing power network. Today, with the rapid development of the decentralized/distributed/sharing economy, a good technical foundation has been laid for the realization of global computing resource sharing. The future of decentralized/distributed/shared computing power is here.
OORT core team
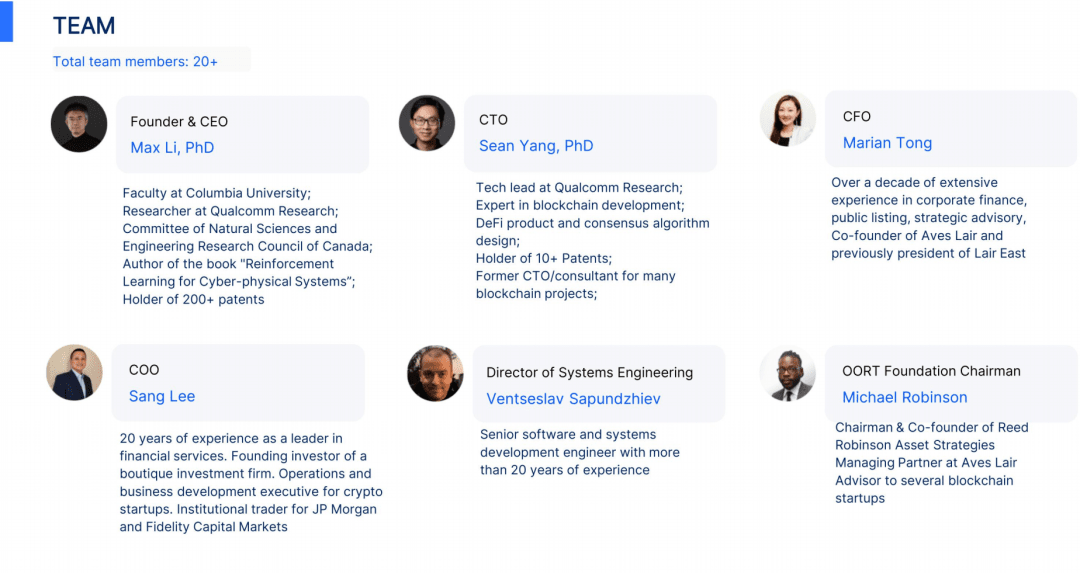
OORT project consultant and mentor team

Tokens rules
About Oort
OORT is a decentralized data cloud platform that aims to integrate global computing and storage resources, maximize privacy and cost-effectiveness, and provide a set of enterprise-level, decentralized solutions for generative artificial intelligence and data-driven businesses. .
Oort's core technology is endorsed by U.S. patents and academic publications, and has established solid partners with more than 40 projects/companies and more than 20 prestigious American universities (such as Harvard, MIT, University of Chicago, etc.) or customer relations.
*20+渠道/生态/客户;BNB Chain(币安)、Tencent(腾讯)、DEll(戴尔)、EMURGO Ventures(加密市值前十的Cardano(ADA)公链、Lenovo Image(联想图像)现为至像、Supermoon Camp、Midas wireless、1024bank、waterdrip、 etc 等