This article lists 24 privacy projects that mainly use zero-knowledge proof technology.
Written by angelilu, Foresight News
This week, the Ethereum developer conference Devconnect was held in Istanbul, Turkey. Among hundreds of surrounding activities, activities related to "zk" accounted for as much as one-fifth. It is not difficult to see how much developers value "zk".
There seems to be an unwritten rule in the crypto world that projects starting with "zk-" usually have a strong technical background. The zk mentioned here actually refers to zero-knowledge proof. ZKP technology was first proposed in the field of cryptography in the 1980s, but it has been tepid due to the lack of more practical implementation scenarios. It was not until the introduction of blockchain technology in recent years that it regained its brilliance. In addition to blockchain, it has also been widely used in cloud computing, machine learning and other fields.
What exactly is zero-knowledge proof? In a recent article, a16z partner Michael Blau even regarded ZKP as a great magic. To better understand this concept, let us compare traditional verification with zero-knowledge proof.
First of all, both traditional verification and zero-knowledge proof have two roles and one event in structure. One of the two roles is called the prover and the other is called the verifier. The prover's task is to prove the authenticity of an event to the verifier.
Traditional verification: The prover must provide conclusive evidence and go through a rigorous verification process to ensure that the event is true. Alternatively, the prover can use proof by contradiction to provide evidence to prove that the event cannot be false.
Zero-knowledge proof: The prover and the verifier can exchange some information that is not directly related to the event. Then, the verifier can determine that the event is true, but only to the extent that he can determine it. Even if a third party closely follows the entire process, they cannot draw the verifier's conclusion.
Application of zero-knowledge proof in blockchain
In the field of blockchain, the characteristics of ZKP make it of great value in solving the two core problems of privacy and expansion. In terms of expansion, the zk-Rollup technology based on ZKP has always been Vitalik’s favorite expansion route. Projects such as StareWare, zkSync and Scroll all use zero-knowledge proofs to improve Ethereum’s expansion capabilities.
In comparison, zero-knowledge proofs have received relatively little attention in solving privacy issues, although privacy has always been one of the most sensitive and concerned topics in the field of blockchain technology. Although blockchain itself has a certain degree of anonymity, its public ledger structure allows all transactions to be viewed by anyone. When a transaction address is linked to an entity, the analysis of the transaction may expose the entity's privacy information, so privacy support is still needed in many niche areas.
Zero-knowledge proof technology plays a vital role here. By using zero-knowledge proof, both parties can prove the transaction without exposing any additional information, which not only protects user privacy, but also prevents fraud and illegal activities to a certain extent. Today, the demand for blockchain privacy applications is far from being fully explored, and the subdivided track has not received much attention. This article will focus on the application and impact of zero-knowledge proof technology in privacy.
The following is an inventory of 24 privacy projects that mainly use zero-knowledge proof technology, which are mainly divided into four categories: Layer 1 public chain, Layer 2, developer tools, and applications.

ZKP Privacy Project Inventory
Privacy public chain
Privacy public chains can be understood as building public chains and privacy at the same time. This type of public chain mainly uses three major technologies to supplement the privacy function of its network, namely: zero-knowledge proof (ZKP), secure multi-party computing (MPC) and trusted execution environment (TEE). Oasis and Secret Network are relatively mature privacy public chain projects at present, but it is worth noting that these two projects do not directly adopt zero-knowledge proof technology. Due to the high complexity of zero-knowledge proof technology, its research and development progress is relatively slow, and real-world applications are even more scarce. This situation suggests that this field still has great future potential, but there is still a lack of clear market leaders.

Come on
Aleo is a blockchain that uses zero-knowledge proof to support privacy and programmability. It builds a private, open-source blockchain by default to supplement the privacy protection that blockchain lacks. The Zexe architecture is its zero-knowledge proof solution, which first performs offline calculations and then generates online transactions that prove the correctness of the calculations without disclosing the details of the calculations, so that transactions can be verified by anyone in a very short time. As a public chain, Aleo has its own virtual machine snarkVM, programming language Leo, development environment Aleo Studio and PoSW consensus algorithm, and has huge market potential in the field of zero-knowledge proof.
Aleo was founded in 2019 and has received nearly $300 million in financing. It has not yet launched its mainnet. The previously announced plan to launch the mainnet in July 2023 seems to have been postponed. The incentive deployment submission plan for Testnet 3 just ended on August 21. It seems that it will take some time for the mainnet to be launched.
Zcash
Zcash is the earliest "anonymous coin" and was the first to propose the idea of deploying zk-SNARK to achieve shielded transmission and provide stronger privacy guarantees than anonymous transactions. It focuses on decentralized payments with privacy and anonymity. It uses zk-SNARK zero-knowledge proof technology to prove off-chain data while hiding on-chain data content, allowing users to create private transactions that hide user transaction amounts and sender and receiver addresses. Zcash has opened up the creative use of ZKP in the field of privacy coins, providing transparent addresses (t addresses) that can be monitored on the blockchain and fully encrypted and untraceable shielded addresses (z addresses).
Mina
Mina claims to be the lightest blockchain in the world. Its size is designed to remain constant as usage grows. It uses ZKP to compress the blockchain state to a very small size (~22 KB), and Mina uses zero-knowledge succinct non-interactive zk-SNARKs to bring access and privacy to Web3. Its smart contract zkApps use encryption technology to protect user privacy, allowing users to interact by proving the authenticity of personal data instead of sharing the data directly. This not only increases user security and privacy, but also reduces the developer's responsibility to protect sensitive data. And its zkApps use Typescript, a general programming language, as a smart contract language, which lowers the development threshold, but perhaps due to the complexity of zk and its incompatibility with EVM, the current ecosystem is not prosperous.
Mina recently announced that the mainnet will undergo a major upgrade. The mainnet will introduce ZK smart contracts, and developers can use o1js to program zkApp more easily. Currently, preparations are being made for the upgrade. The testnet is divided into 4 phases, including zkApp end-to-end (E2E) testing, external security audits, protocol and performance testing, and preparations for the upcoming upgrade. The first two phases have been completed.
Horizen
Horizen is a blockchain platform powered by zero-knowledge proofs and equipped with zk-SNARKs for selective privacy, giving users optional anonymity. Horizen is EVM-compatible and has the Ethereum virtual machine Horizen EON.
Its biggest feature is that its architecture consists of a main chain and side chains, which can perform cross-chain transfers of ZEN coins through its Cross-Chain Transfer Protocol (CCTP). However, due to the regulatory environment, Horizen announced in April this year that it would remove privacy from the main chain and ZEN, and it is expected to abandon the main chain shielded pool in September and cancel support for shielded transactions with transparent inputs (T address -> Z address) from the Horizen main chain level. However, it does not completely not support privacy, and the side chain will be focused on scalable data privacy.
Horizen's transformation shows that privacy public chains are proposing governance and self-help in the current harsh regulatory environment. At the same time, we can also see the impact of the regulatory environment on privacy. The arrest of the founder of Tornado Cash is also sounding the alarm for major privacy protocols.
Dusk
Dusk is a privacy-preserving Layer 1 blockchain protocol designed for commercial compliance. Its network security is guaranteed by a new proof-of-stake (PoS) consensus mechanism called Succinct Attestation, which also meets the important need for settlement consistency in financial scenarios.
Dusk is characterized by both privacy and compliance. Dusk provides an identity verification (KYC) solution that guarantees customer privacy. The algorithm is based on PLONK's ZK algorithm.
Iron Fish
Iron Fish is a decentralized, proof-of-work (PoW)-based, censorship-resistant, and publicly accessible blockchain project inspired by the zk-SNARK-based Sapling protocol, designed to provide privacy guarantees for every transaction. Unlike other optional privacy public chains, Iron Fish hides transaction information, mining information, wallet information, etc., which cannot be seen by any second party except the private key owner, which can be said to be absolute privacy.
Manta Network
Manta is the first zk-SNARK-based Web3 privacy protection network in the Polkadot ecosystem. It has its own UTXO-based wallet address system, allowing users to store, transfer and redeem privacy assets. Manta's main products include privacy payment MantaPay, zkSBT with privacy function, and privacy wallet Manta Wallet.
Findora
Findora is a privacy-preserving blockchain based on zero-knowledge proofs, with programmability that enables developers to build privacy-focused applications (zkDapps) on its chain, deploy modular subnets that can be customized according to the needs of specific dApps, and enable users to control the visibility of their on-chain data through zkDapps. In addition, it is EVM-compatible and can act as a second layer to extend Ethereum privacy through its cross-chain transfer function. Findora recently launched a Game Specific Chain (GSC), a new subnet that provides a development environment for zero-knowledge Web3 games.
In the mail
Namada is a proof-of-stake L1 for inter-chain asset-agnostic privacy, designed to support shielded transfers of any type of (fungible and non-fungible) assets held by multi-chain users using zero-knowledge proof technology. Its development company, Anoma Foundation, announced in May that it had completed a $25 million financing led by CMCC Global.
MobileCoin
MobileCoin (MOB) is a cryptocurrency designed for everyday transactions, mobile first, where no one except the sender and receiver can see the details of the transaction. MobileCoin achieves privacy through zero-knowledge proof technology, which uses a special ZKP called Bulletproofs to build "range proofs" for encrypted values. Bulletproofs are short, non-interactive ZKPs.
Privacy Layer 2
In addition to building a new public chain with integrated privacy features from scratch, many projects also choose to use zero-knowledge technology to add a privacy protection layer to existing public chains, solving the scalability problem while ensuring privacy for existing public chains, or using zero-knowledge technology and blockchain in combination to solve specific problems, which is more composable than public chains.

Starknet
Starknet is a decentralized ZK rollup based on Ethereum launched by StarkWare, which aims to improve the scalability and privacy of the blockchain by leveraging zk-STARK proof technology.
Aztec
Aztec is a privacy and expansion solution based on ZK Rollup. It has a zk-zkRollup with two layers of zero-knowledge circuits. One layer of zk is used to encrypt private user transactions, and the second layer of zk is used to compress transactions, enabling Aztec to concisely prove a large number of encrypted state transitions and is not compatible with EVM. In March, it announced that it would shut down its privacy infrastructure Aztec Connect, and the future development center would shift to the development of zero-knowledge universal language Noir and blockchain.
Aztec's latest progress is to build privacy abstractions to provide developers with smart contract privacy, supporting default anonymity, private state read/write functions, and private smart contract function execution.
Ola
Ola is a scalable, privacy-preserving, compliance-friendly ZK-ZKVM Rollup platform that focuses on programmable privacy, programmable scalability, and multi-language compatibility. It aims to become a Layer 2 that can supplement privacy and scalability capabilities for all programmable Layer 1 blockchains. It is Turing complete and supports storage access operations.
The main product parts include the ZK-friendly virtual machine Ola-VM and the smart contract language Ola-lang: Ola-lang is a general language (GPL) based on ZK-VM, with higher programmability, and can deploy any smart contract according to project requirements, whether public or private. The ZK-friendly virtual machine Ola-VM uses the reduced instruction set computer (RISC) architecture to achieve higher performance through a full-featured zk-friendly design and non-deterministic computing support. The code of these two components was officially open sourced during DevConnect in Turkey last week.
Ola completed a $3 million seed round in July this year. Recently, it supported Poseidon2 hash in its proof system, which brought more than 40% prover performance improvement compared to the original Poseidon hash. In addition, Ola announced the opening of Ola Dev Testnet whitelist applications during DevConnect in Turkey, providing a channel for developers and ordinary users to participate in Ola. Its public testnet and mainnet will be launched next year.
Espresso Systems
Espresso Systems is a decentralized sequencer and data availability system that connects various Layer 2 expansion solutions, supporting Optimistic Rollup and ZK Rollup. In terms of privacy, it has developed a configurable asset privacy smart contract CAPE using technologies such as zero-knowledge proof and has been open sourced, enabling digital asset creators to configure who can view data about the custody and transfer of the assets they created. Users can create new tokens and wrap existing Ethereum tokens to give them the desired privacy attributes.
zkPass
zkPass is a privacy-preserving protocol for private data verification. It is built on multi-party computation (MPC), zero-knowledge proof (ZKP), and three-party transport layer security technology (3P-TLS). zkPass provides TransGate, which enables users to selectively and privately verify their data on HTTPS websites in the Web3 world. It can cover a variety of data types, such as legal identity, financial records, healthcare information, social interactions, work experience, education and skills certification, etc. The project was incubated by Binance Labs and completed a $2.5 million financing in August this year.
Developer Tools

NuLink
NuLink is committed to developing out-of-the-box privacy protection solutions, allowing decentralized application developers to achieve privacy through its solutions through APIs. The architecture of the NuLink network includes the application layer, cryptographic layer, storage layer, blockchain layer, and observer network. It is expected to launch a ZKP-supported data availability mechanism and private data computing supported by FHE by 2024.
Railgun
Railgun is a privacy and anonymity solution built on the Ethereum platform that can interact directly with DEX, lending and smart contract applications. Railgun uses zero-knowledge proof technology to achieve privacy protection of users' financial status, personal identity and behavior patterns, and supports selective transparency, allowing users to disclose certain identity or financial information in a targeted manner when necessary, such as when facing audit or compliance requirements.
The system features three core functions: Add, Split, and Remove. These three operations are built on zero-knowledge proofs and provide different levels of privacy and anonymity. Users can flexibly choose these operations according to their needs, and have the option to combine multiple operations into one transaction to reduce the Ethereum network gas fee.
Earthquake
Sismo leverages zero-knowledge proofs (ZKP) and privacy-preserving technologies to enable users to aggregate their identities and selectively disclose personal data to applications. Sismo Connect is a developer-friendly layer on top of the proof scheme that allows developers to request and verify ZK proofs to access personal data without violating user privacy. Compared to other protocols that focus on data privacy, Sismo focuses more on identity privacy.
Privacy Apps

Tornado Cash
Tornado Cash is a privacy transaction tool that uses zero-knowledge proof (ZKP) technology, especially zk-SNARKs, to achieve transaction anonymity. The basic working principle is coin mixing. Due to its privacy transaction characteristics, Tornado Cash is often associated with hacker attacks and money laundering. SlowMist's report last year stated that Tornado Cash received nearly 75% of the total money laundering on the Ethereum network.
Tornado Cash has also been caught up in a regulatory storm recently. On August 24, the U.S. Department of Justice arrested Tornado Cash co-founder Roman Storm, and Roman Storm and another co-founder of Tornado Cash, Roman Semenov, were accused of conspiracy to launder money, violating sanctions, and operating an unlicensed remittance business.
Elusiv
Elusiv is a zero-knowledge compliant privacy protocol currently built on Solana. It uses zk-SNARKS to achieve private transactions while emphasizing decentralized compliance, allowing users to freely choose which transactions to disclose using Elusiv. Elusiv was launched on Solana in March this year, and has now launched the privacy token trading function on Solana.
zkBob
zkBob is a privacy solution based on stablecoins, deployed on Polygon and Optimism. It uses zero-knowledge proof technology to achieve anonymous senders, receivers, and amounts in fund transfers. It supports use on more than 15 EVM-compatible networks. Its token BOB is a multi-chain and multi-collateral stablecoin with optional privacy features.
Brine
Brine is an order book privacy trading DEX that implements privacy transactions through StarkWare's zk-STARK proof technology. It adopts an on-chain and off-chain dual-component design, and zero-knowledge proof technology is used in two aspects: privacy and proof of validity of off-chain transactions transmitted to the chain.
It launched its mainnet in June this year, with a current total transaction volume of approximately US$500 million. In September this year, it completed a US$16.5 million financing round led by Pantera Capital with a valuation of US$100 million, with participation from StarkWare, Spartan Group and others.
zkMe
zkMe is a decentralized Web3 credential network that uses zero-knowledge proof technology to achieve secure and private credential issuance and verification, focusing on end-to-end zero-knowledge processing and selective information disclosure. When a user (credential holder) creates a DID using zkMe, they will obtain a unique SBT, which is cryptographically bound to their public key and used as proof of identity. ZKP enables users to verify their identity without revealing any sensitive information.
ZK-Team
ZK-Team is one of the 18 projects selected for the ERC-4337 account abstraction funding round announced by the Ethereum Foundation in September. Launched by Canadian blockchain company PriFi Labs, it is a proof-of-concept for privacy-preserving abstract accounts that allows organizations to manage team members while maintaining their personal privacy. Through zero-knowledge proofs, transactions implemented by ZK-team ensure the confidentiality of different addresses of team members and their associated quotas.
Track Analysis
Financing
After analyzing the above projects, we can see that a16z has invested in Aleo, Iron Fish, and Nym, and Sequoia Capital has invested in Iron Fish, Espresso Systems, etc. The ZK privacy project has attracted the attention of top venture capitals in terms of market demand, technological innovation, and long-term value. The large amount of investment further proves the potential and importance of this field.
From a funding perspective, Aleo is the most funded privacy public chain project to date, so the market has high expectations for it, but the repeated delays in the launch of the project's mainnet have gradually reduced the project's attention. Aleo has recently successfully entered the third phase of its testnet. Once its mainnet is successfully launched, it will be an important milestone in the field of privacy technology.
Established
The above mainstream privacy public chains were all launched in 2018 and 2019. The reason is that the basic technologies of blockchain and cryptography gradually matured in 2018 and 2019, making zero-knowledge proof easier to use in the blockchain field. Secondly, in terms of compliance, the EU General Data Protection Regulation (GDPR) officially came into effect in May 2018. In addition to the implementation of other privacy regulations, companies and individuals are paying more and more attention to data privacy, which has promoted the demand for privacy public chains. Market factors cannot be ignored. In 2017, the blockchain and cryptocurrency market experienced a round of prosperity, which made the market have more abundant funds. Compared with Ethereum and Bitcoin, privacy features have become a clear competitive advantage, which has caused some funds to flow to privacy public chains.
However, most of the infrastructure using ZKP technology was established after 2021. This shows that the privacy public chain is becoming increasingly saturated and the demand for privacy in ordinary public chains is becoming more and more obvious. More and more ZKP infrastructures have emerged in the past two years.
The choice of ZKP technology
There are currently many ways to implement zero-knowledge proofs, which can be divided into zk-SNARKS, zk-STARKS, PLONK and Bulletproofs. Among all the projects mentioned in this article, zk-SNARKs is the most used. zk-SNARKs is used to prove that a given calculation has been performed correctly while keeping the input private. Its characteristics are that the proof size is relatively small, and zk-STARKS does not require an initial trusted setup scenario.

PLONK is a variation of the zk-SNARK proof system. PLONK's trusted setup is universal, which means it can be started once and reused by all circuits. It is also updateable: people can always add new randomness until they are sure that the setup has not been compromised. Bulletproofs is a general zero-knowledge proof, mainly used for range proofs, generally used in confidential transactions.
As shown above, different algorithms have different technical features. Therefore, many projects use hybrid zero-knowledge proof algorithms in their implementation logic. Take the programmable privacy and expansion solution Ola as an example. It uses Starky as the proof generation algorithm and Plonky2 as the recursive circuit algorithm. The common point between the two is that they are both based on STARK, which means that neither requires a third-party trusted setup.
Smart contracts and programmability
Programmability refers to the feature of a privacy project that enables other developers or organizations to build and expand its privacy features. Zero-knowledge proof technology and specially developed programming languages help developers build privacy-enabled applications. As the demand for privacy increases, programmability in privacy projects is increasingly favored by developers and users. Aleo, Aztec, etc. introduced above all have programmable features.
There are two forms of programmability: ZKDSL and ZKVM. ZKDSL allows developers to directly write low-level circuit constraints, lowering the threshold for writing circuits and zkDapps. For example, Aztec's programming language Noir and Aleo's programming language Leo both use ZKDSL, but the characteristics of ZKDSL determine that its expressive power still has inherent limitations. Another form is ZKVM, which is a better choice for programmability. Protocols that use ZKVM include Ola, whose smart contract language Ola-lang is built on ZKVM.
Privacy by Design
In the field of blockchain privacy design, there are generally two main data structure models: UTXO (Unspent Transaction Output) model and Account model.
UTXO: This is the model used by some early blockchains such as Bitcoin. In the UTXO model, transactions are not conducted directly between accounts, but by referencing unspent transaction outputs (UTXO). Each new transaction generates a new UTXO and consumes the old UTXO. This model has high scalability and flexibility.
Account model: Smart contract platforms such as Ethereum usually use the account model. In this model, each participant has one or more accounts, and the account has a state associated with it (e.g., balance, contract data, etc.). Transactions are conducted directly between accounts, more like the way traditional banking systems work. Although it is relatively intuitive and simple in design, it has relatively low operability in terms of privacy.
Most privacy protocols use the UTXO model in their design. Zcash’s UTXO-based Note structure can easily hide the sender and receiver information of transactions. Actec, Railgun, Ola, etc. also use the Note structure, but several projects are slightly different, each with its own advantages and disadvantages.
DApp-specific privacy
Aztec's privacy design relies on the UTXO (Unspent Transaction Output) model, which makes it excellent for simple privacy transactions, but limits the possibility of developing complex smart contracts. At present, Aztec's main application is its own zk.money, a privacy payment platform based on zero-knowledge proof. Although the platform performs well, the limitations of the UTXO model mean that if other projects want to integrate Aztec's privacy features, they need to do so through a specially designed interface - the Aztec Connect gateway contract. This gateway contract acts as a bridge, making it easier for external projects to integrate with Aztec, although doing so may introduce additional complexity and overhead.
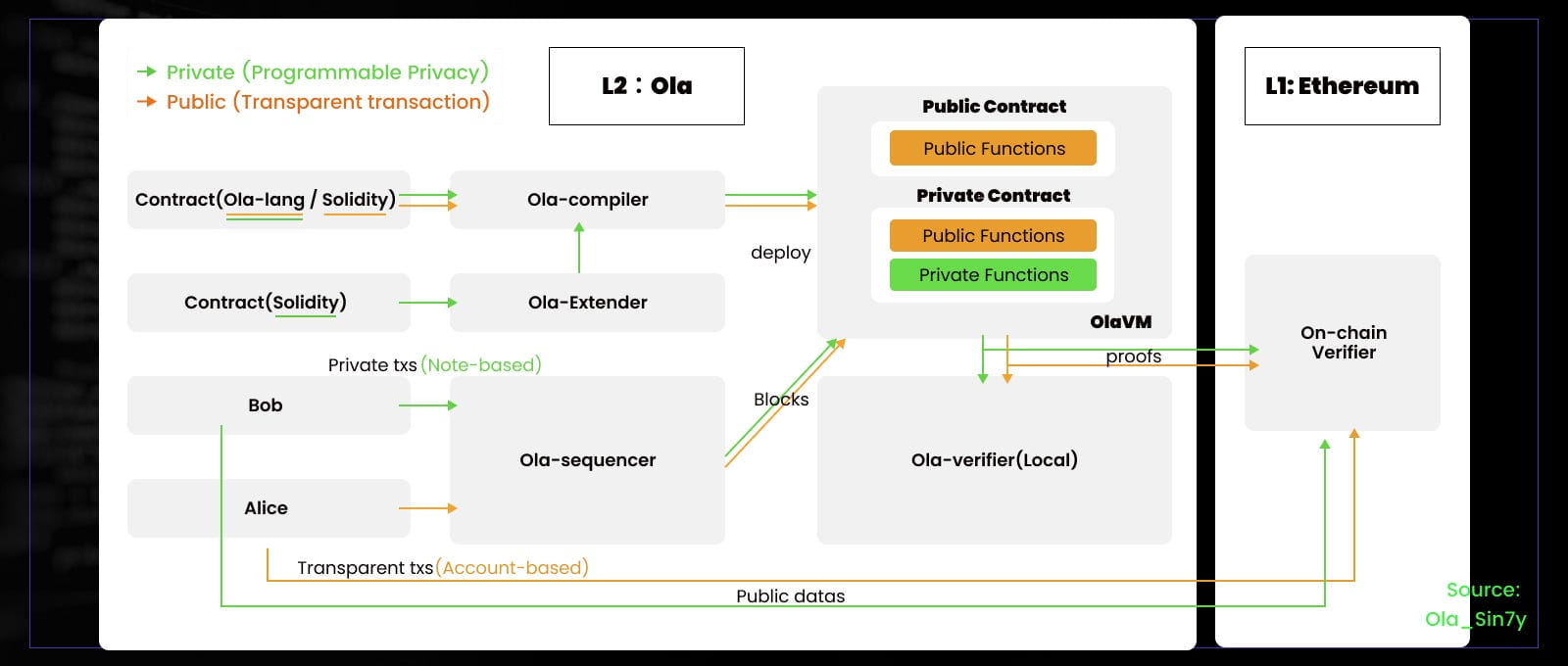
Programmable Privacy
As mentioned in the programmability section above, if programmability is introduced on Aztec’s privacy, can it solve the problem of limiting the development of complex smart contracts? For example, Ola did not choose DApp-specific privacy in its settings, but introduced programmability. Developers can freely choose to deploy public contracts (based on Account), privacy contracts (based on Note), and ordinary contracts (based on Account & Note), so that the project can not only meet diverse privacy needs, but also provide developers with greater flexibility and creativity.
Compliance
The biggest challenge currently facing privacy protocols is the chilling effect of strong supervision. In August 2022, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) announced sanctions against Tornado Cash. After being sanctioned, Tornado Cash’s capital inflows dropped significantly, reaching 30 dropped 68% in one day. In August this year, the U.S. Department of Justice arrested Tornado Cash co-founder Roman Storm and charged him and another co-founder with conspiracy to launder money, violating sanctions, and operating an unlicensed remittance business.
Because of the privacy feature, privacy protocols have become an essential tool for hackers. North Korean hackers use privacy protocols such as Tornado Cash and Railgun to launder money. Therefore, cryptocurrencies in the privacy track have experienced multiple rounds of "delisting". The compliance design of privacy protocols is particularly important. Vitalik recently proposed the concept of "privacy pool" in his paper to balance the supervision and compliance of privacy protocols, allowing users to publicly prove information about which deposits their withdrawals may come from, but without losing privacy.
Many projects currently have a "view key" function that allows users to selectively disclose their transaction information. However, most protocols fail to enforce the view key function, which makes it difficult to ensure the degree of privacy protection for users. In addition, these protocols usually adopt an appendix-style private tree design, which makes it difficult to provide the necessary traceability for compliance purposes.
It is worth noting that Ola uses an updateable Private Tree design and a key viewing function. Ola's Private Tree is updateable and supports tracing transaction paths, making privacy disclosure more automated and compliant. Through this design, users can manage their privacy more flexibly and share necessary information with regulators when needed, while still maintaining a high degree of privacy protection.
summary
However, zero-knowledge proof technology is not without flaws. Its implementation requires a lot of computing resources, which may have a certain impact on the efficiency of the system. Therefore, in current research and development, how to ensure privacy while not reducing system performance has become an important challenge.
In the Web3 era, the importance of privacy is obvious. Users' need to protect sensitive information makes private public chains and privacy applications an indispensable part of the Web3 field. These private public chains provide powerful programming languages and complete development tools, attracting developers to actively participate in the construction. However, one of the biggest risks facing privacy infrastructure is that the scale of its future demand cannot be determined. In addition, it cannot be ruled out that various public chains or projects will directly launch native privacy protection mechanisms in the future, which may have an impact on third-party privacy projects. At present, projects that have attracted much attention from the community, such as Aleo and Espresso Systems, are still in the testnet stage, and their development prospects have not yet been determined. Therefore, the development of the privacy field still needs to pay close attention to the evolution of the market and technology.
