I have been thinking about SIGN Protocol and at first glance, SIGN can look underwhelming. Open SignScan and you’ll see rows of attestations—who signed what, for whom, and when. It’s easy to shrug and say: “SIGN is just a simple attestation list.”
When I look closer, though, and that “list” is actually the front door to an evidence layer: a protocol for modeling, signing, storing, and verifying the claims that real systems of identity, money, and governance depend on.
Why SIGN Looks Simple On The Surface
I am astonished that the simplicity is intentional. SIGN wants attestations to feel as boring and routine as database rows, so builders can plug trust into their apps without becoming cryptography or cross chain experts.
From a user or explorer perspective you see:
A schema ID. An issuer and subject. Some structured fields and a timestamp.
I don’t need to believe anyone that’s the “simple list.” But under the hood, each one of those entries is a signed, schema conformant statement with hooks, revocation logic, and cross chain semantics attached.
That’s where trust actually comes from.
Under The Hood: SIGN As An Evidence Layer
SIGN’s own docs literally describe it as the evidence layer of the S.I.G.N. stack: the part that turns facts into durable, verifiable, programmable objects. It does that through four main pieces.
1. Schemas: shared language, not ad hoc JSON
Every attestation must conform to a registered schema that defines field names, types, and rules. This means:
“KYC passed user”, “stablecoin reserve snapshot”, or “audit completed” all have predictable structures.Different dApps, regulators, or chains can interpret the same attestation consistently.
Instead of every project inventing its own ad hoc structs, SIGN gives the ecosystem a common vocabulary for trust.
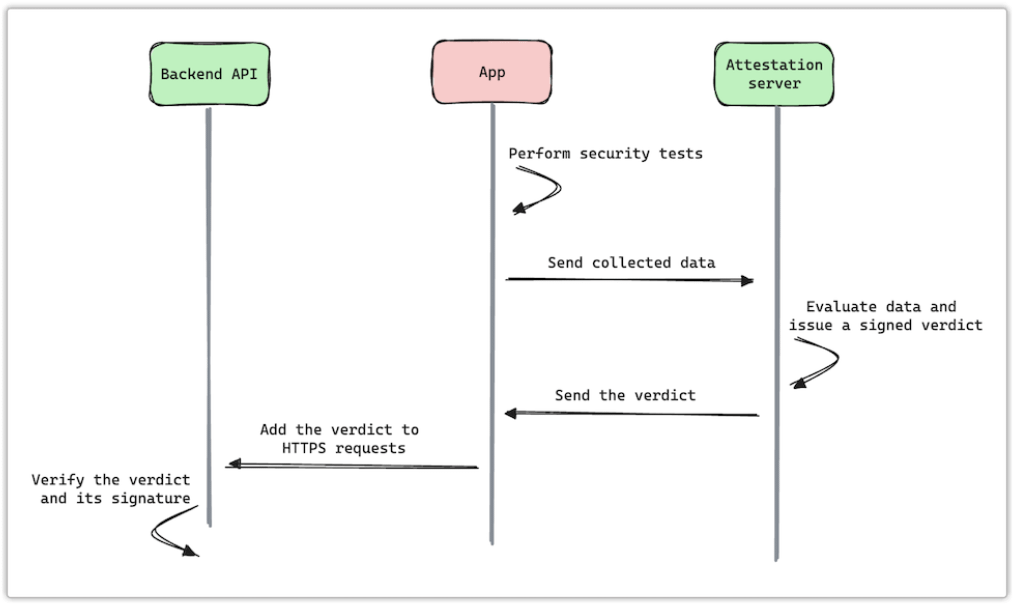
2. Cryptographic binding and integrity
Attestations aren’t just rows; they’re signed evidence:
Issuers sign payloads with their keys. Subjects (people, wallets, contracts) can also be cryptographically linked. The data is anchored on chain or anchored via hashes to off chain storage.
This makes each attestation more like a notarized statement than an editable database row.
3. Schema hooks: logic attached to evidence
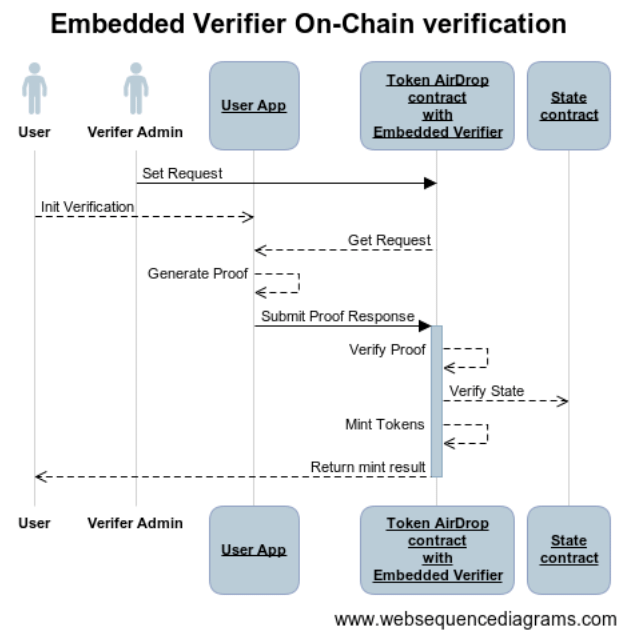
Schema hooks are where SIGN stops being “just a list” and becomes a programmable trust engine. Hooks are smart contract callbacks attached to a schema that can:
Whitelist which addresses are allowed to attest. Enforce fees, rate limits, or role checks. Trigger downstream actions when an attestation is created or revoked.
For example, a “verified business” schema can have a hook that only allows government approved registrars to issue, and automatically updates allowlists in other contracts.
4. Omni chain resolution and indexing
Signing a claim is only half the story; other systems must be able to find and trust it. SIGN handles:
Indexing and querying via SignScan, APIs, and SDKs. Resolving attestations across networks, so you’re not tied to a single L1.
To the outside, it still looks like “just querying a list.” In reality, there’s a cross chain resolver and indexing layer doing the heavy lifting.
Concrete Things People Are Building On SIGN
Once you stop thinking of SIGN as a list and start thinking of it as evidence infrastructure, the use cases line up quickly.
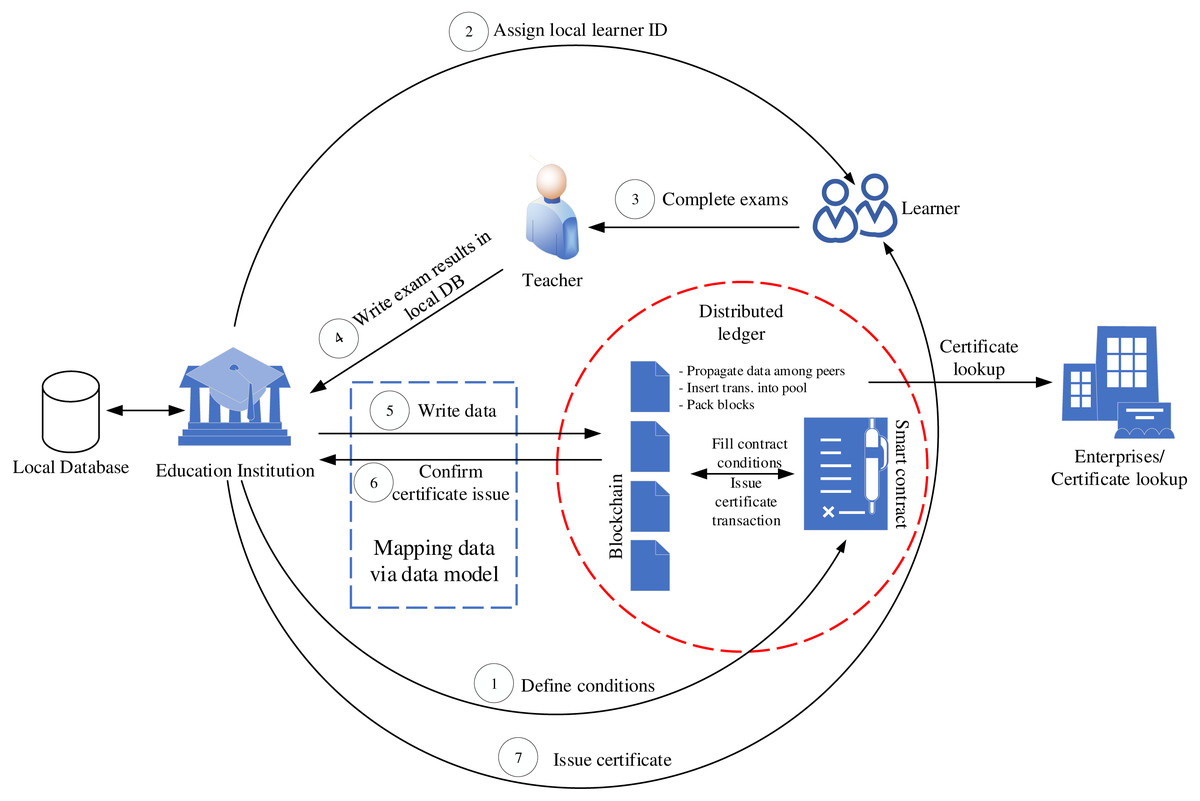
Identity & KYC: issuers create attestations like “this wallet passed KYC under X rule,” reusable across DeFi, launchpads, and national platforms.
Stablecoins and reserves: stablecoins modeled as signed claims on reserves and policy, rather than opaque ERC 20 balances.
Audit trails: OtterSec’s “Proof of Audit” case study shows audits turned into attestations that reference code versions, findings, and status—queryable instead of buried in PDFs.
Cross chain assertions: with Lit’s TEEs, SIGN records delegated attestations about what’s true on other chains, giving you verifiable cross chain checks.
In all of these, the interface is “issue and read attestations,” but the real value is that the evidence is now standard, verifiable, and programmable.
Why The “Just A List” Mental Model Can Mislead You
Calling SIGN “just a simple attestation list” is like calling DNS “just a list of names” or Git “just a list of commits.” Technically true at a glance, but deeply misleading about what those systems enable.
From my own experience, the moment SIGN clicks is when you:
Take one noisy, trust heavy process in your product (KYC, approvals, document signing, roles). Model it as a schema.
Let SIGN issue, store, and expose the attestations.
Suddenly, “Do we trust this?” becomes a query instead of a bespoke integration project.
If You’re Building With SIGN, Treat The List As An Interface, Not The Product
If you’re curious about SIGN, here’s a practical way to explore it:
Read the Sign Protocol overview and schema hooks docs to understand the evidence layer mindset. Use the Quickstart to register a schema and issue a few test attestations from code. Ask: “What decisions in my app could be an attestation instead of a private flag?”
#SignDigitalSovereignInfra @SignOfficial $SIGN


