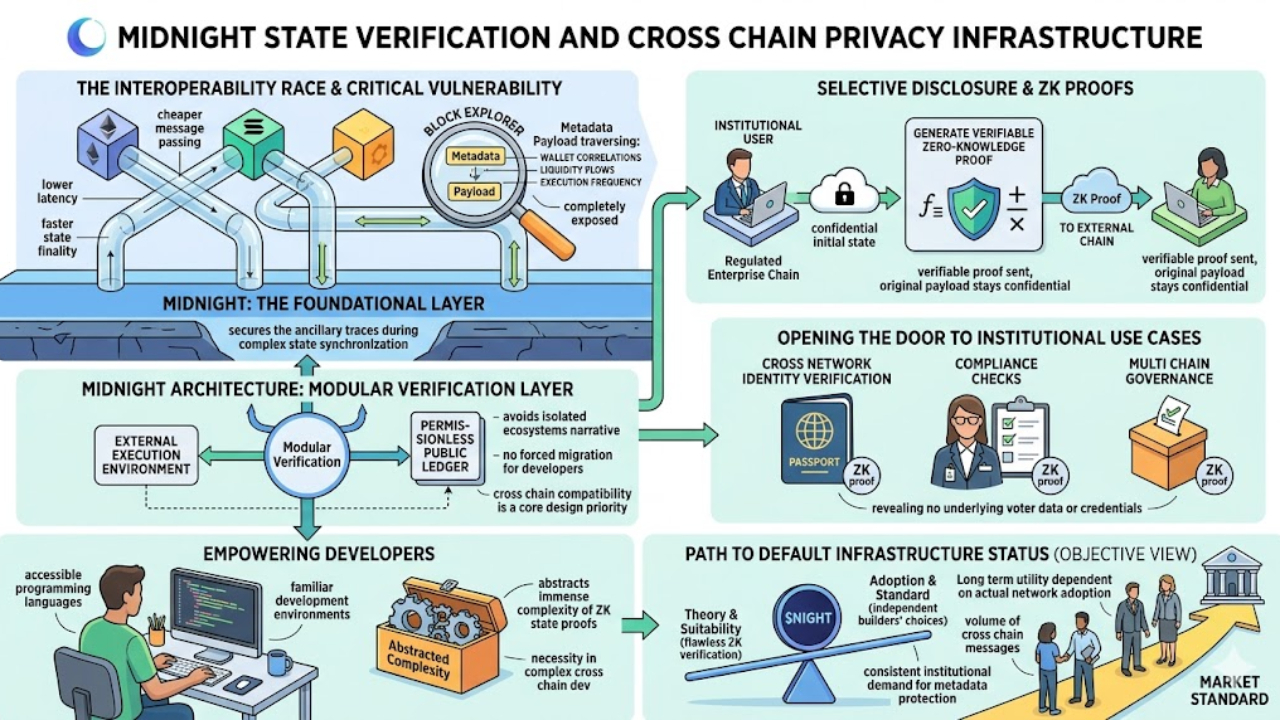
Yesterday I was reviewing various bridge exploits and interoperability protocols while dissecting the technical documentation of Midnight. Many projects in the interoperability space are clearly racing for cheaper message passing, lower latency, or faster state finality across different networks.
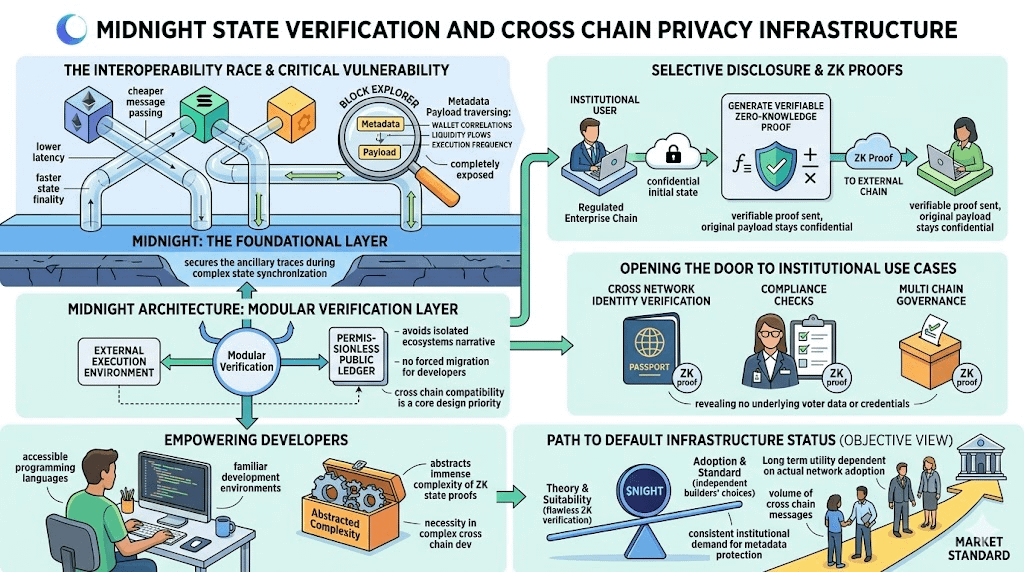
Midnight gives me a very different read because the deeper I look into the architecture, the more I see they are addressing a fundamentally harder operational logic. They are actively asking if cross chain communication inherently requires complete public exposure of state transitions to function securely across disparate ecosystems.
That specific technical question is exactly why I view Midnight as a highly viable foundational layer for interconnected ecosystem privacy. When looking at the current state of blockchain bridging, the critical vulnerability is not merely the locking, minting, or burning mechanics of wrapped assets.
What builders frequently ignore is that the metadata payload traversing between networks is completely exposed to block explorers and analytical tools. This systemic transparency allows anyone to map entire liquidity flows, execution frequencies, and wallet correlations across multiple ecosystems simultaneously.
Midnight explicitly targets this structural flaw by attempting to secure the metadata traveling between heterogeneous ledgers alongside the core transaction payload. A genuine cross chain infrastructure layer must protect the ancillary traces left behind during complex state synchronization processes.
In sophisticated institutional environments, these metadata traces often reveal the exact nature of the cross network arbitrage, internal corporate transfers, or large scale institutional capital flight. The architectural flexibility of Midnight is another strong indicator of its potential in this specific infrastructure role.
They completely avoid the isolated ecosystem narrative that plagues many legacy privacy networks, which is where Midnight truly diverges from older designs. Instead, they position the architecture to operate as a modular verification layer capable of connecting with external execution environments and established public ledgers.
This structural decision matters deeply because a default cross chain privacy layer cannot realistically force developers to migrate their entire user base onto a completely new execution environment just to utilize zero knowledge proofs.
Midnight clearly treats cross chain compatibility as a core design priority. The system is built to work smoothly with major networks and to expose familiar application interfaces without forcing ecosystems into isolation.
The capability to support selective disclosure during cross chain state updates is where the practical application truly solidifies. Moving sensitive data between a highly regulated enterprise chain and a permissionless public ledger typically forces a binary choice between total opacity or total transparency.
Midnight takes a more practical route. The initial state stays confidential, while the system still produces a verifiable zero knowledge proof. That proof can then be sent to a different chain and checked there without exposing the original payload.
That mechanism opens the door to institutional use cases well beyond token wrapping or liquidity transfers. It can support cross network identity verification, compliance checks, and multi chain governance without revealing the underlying voter data or user credentials to the public.
Furthermore, any protocol aiming for default infrastructure status must abstract the immense complexity of zero knowledge state proofs away from the end user and the application developer. Midnight focuses heavily on accessible programming languages and familiar development environments.
This specific approach is an absolute necessity because cross chain development is already highly complex and prone to critical security failures without introducing dense academic cryptography hurdles into the daily builder workflow.
Yet, we must maintain extreme objectivity and clearly separate architectural suitability from the reality of becoming the default market standard. The long term economic utility of $NIGHT will be entirely dictated by actual network adoption and the sheer volume of cross chain messages utilizing this specific privacy standard.
A decentralized protocol can possess theoretically flawless zero knowledge verification, but independent builders must actively choose to route their interoperability needs through Midnight rather than relying on cheaper standard transparent bridges.
The long-term case for $NIGHT depends on whether real network effects emerge over time. Institutional capital and decentralized applications will have to consistently demand this level of metadata protection across connected ledger operations before Midnight can be treated as default infrastructure.
$NIGHT #night @MidnightNetwork