I have been thinking about how privacy is handled in Web3, and it often feels contradictory. Systems claim transparency as a strength while users increasingly expect control over their data. When I look at Sign Protocol, the idea of preserving privacy through encryption sounds promising at first. Attestations can represent claims without exposing raw data. That seems like a step in the right direction.
But I remain cautious.
Encryption is often presented as a complete solution. In reality, it is only part of a larger system. Data can be encrypted, but questions still remain about who holds the keys, who can access the data, and how it is shared over time. Privacy is not just about hiding information; it is about controlling how and when it is revealed.
In theory, Sign Protocol’s approach aligns with selective disclosure.
A user can prove that something is true without revealing all underlying details. For example, an identity credential could confirm eligibility without exposing full personal information. This reduces unnecessary data exposure and aligns with principles of minimal data sharing.
That sounds efficient.
But I keep asking how this works in practice.
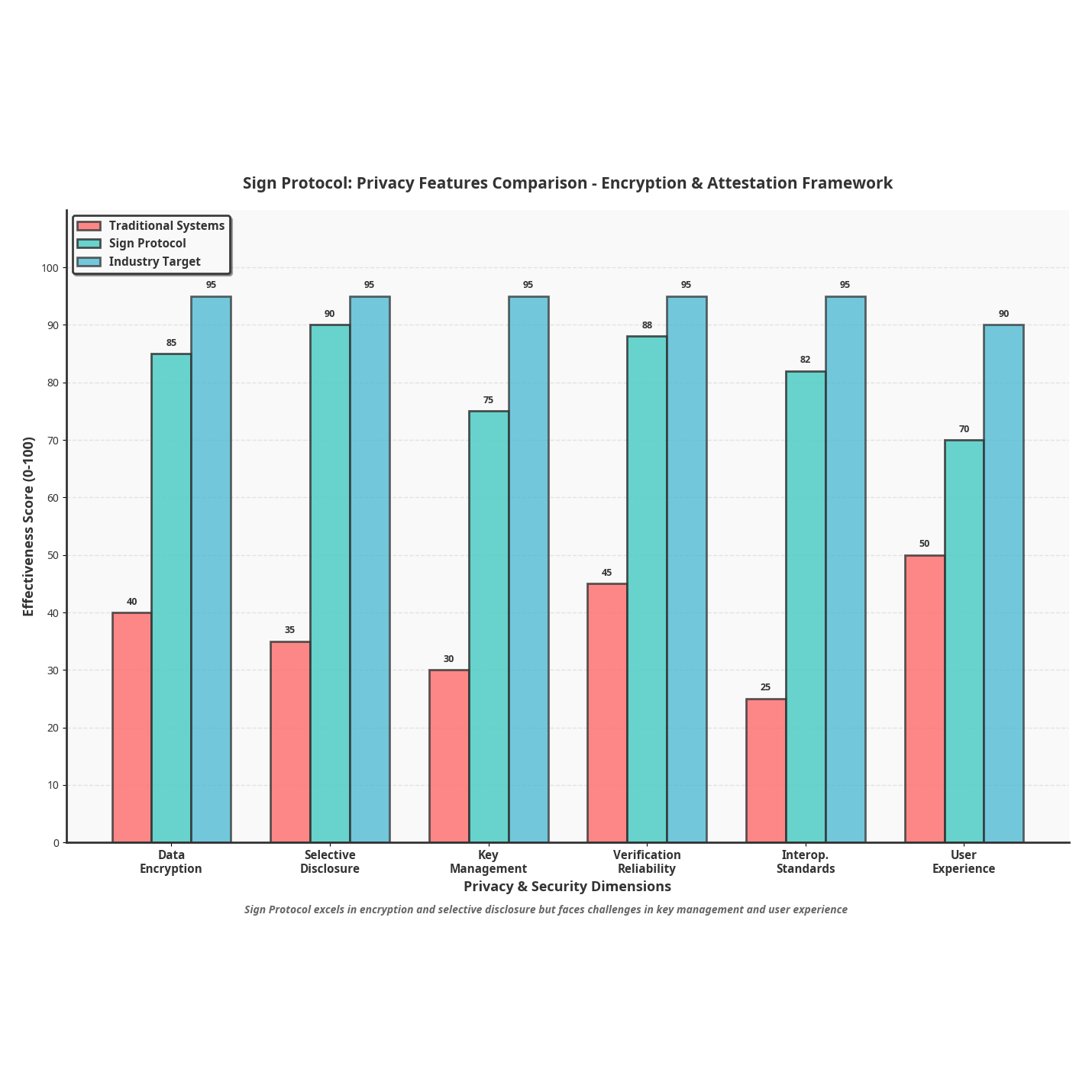
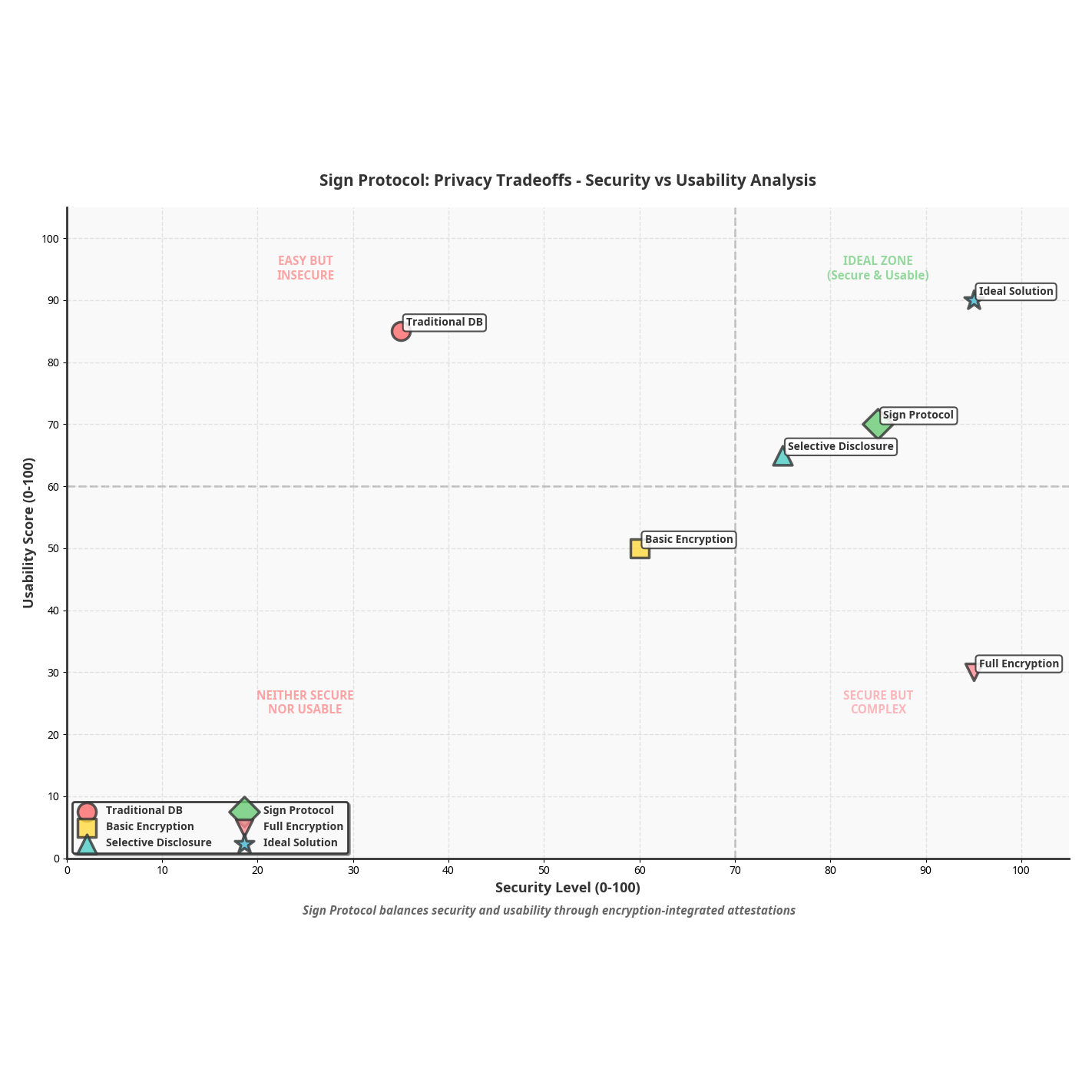
Encryption introduces complexity. Key management becomes critical. If users lose access to their keys, they may lose access to their own data. If keys are managed by external systems, the model starts to resemble centralized control again. The balance between usability and security is difficult to maintain.
Another aspect I think about is trust in the system.
Even if data is encrypted, the process of issuing and verifying attestations must be reliable. If issuers are compromised or verification rules are weak, the system can produce misleading results while still appearing secure. Encryption protects data, but it does not guarantee correctness.
There is also the question of interoperability.
Encrypted attestations must be usable across different platforms. Applications need to understand how to interpret and verify them without exposing sensitive information. This requires shared standards and consistent implementation. Without that, the system risks fragmentation.
From a technical perspective, the combination of encryption and attestations makes sense.
Data remains protected. Proofs remain verifiable. Applications can operate without direct access to sensitive information. This creates a model where privacy and functionality coexist rather than compete.
Still, I wonder how widely this approach will be adopted.
Developers often prioritize simplicity. Encryption adds layers that can slow development and introduce new points of failure. If the system becomes too complex, it may struggle to gain traction despite its advantages.
Another factor is user awareness.
Most users do not think about encryption directly. They care about whether their data feels safe and whether systems are easy to use. If privacy features create friction, they may be ignored or bypassed.
What I find interesting about Sign Protocol is that it does not position encryption as an isolated feature.
It integrates it into a broader framework of attestations and verification. Privacy becomes part of how data is structured and used rather than an add-on.
That integration is important.
But it does not eliminate tradeoffs.
Security, usability, and scalability must all be balanced. Improving one often impacts the others. Designing systems that handle these tradeoffs effectively is challenging.
For now, I see Sign Protocol’s encryption approach as a step toward more privacy-aware infrastructure.
It addresses real concerns about data exposure.
It introduces mechanisms for selective disclosure.
But it also highlights how complex privacy becomes when applied to decentralized systems.
Whether this model becomes standard will depend on how well it can handle these complexities in real-world applications.
Because preserving privacy is not just about protecting data.
It is about building systems that people can trust to manage that data responsibly over time.